You are investigating issues with to gateway cluster members are not able to establish the first initial cluster synchronization. What service is used by the FWD daemon to do a Full Synchronization?
What is a best practice before starting to troubleshoot using the “fw monitor” tool?
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Wire Mode configuration, chain modules marked with ____________ will not apply.
To enable Dynamic Dispatch on Security Gateway without the Firewall Priority Queues, run the following command in Expert mode and reboot:
Both ClusterXL and VRRP are fully supported by Gaia R81.10 and available to all Check Point appliances. Which the following command is NOT related to redundancy and functions?
What level of CPU load on a Secure Network Distributor would indicate that another may be necessary?
Check Point Support in many cases asks you for a configuration summary of your Check Point system. This is also called:
When running a query on your logs, to find records for user Toni with machine IP of 10.0.4.210 but exclude her tablet IP of 10.0.4.76, which of the following query syntax would you use?
Alice & Bob are going to deploy Management Data Plane Separation (MDPS) for all their Check Point Security Gateway(s)/Cluster(s). Which of the following statement is true?
Which Check Point process provides logging services, such as forwarding logs from Gateway to Log Server, providing Log Export API (LEA) & Event Logging API (EL-A) services.
Installations and upgrades with CPUSE require that the CPUSE agent is up-to-date. Usually the latest build is downloaded automatically. How can you verify the CPUSE agent build?
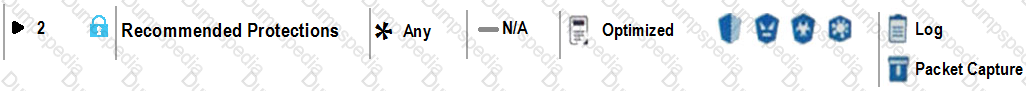
View the rule below. What does the lock-symbol in the left column mean? (Choose the BEST answer.)
Which process is used mainly for backward compatibility of gateways in R81.X? It provides communication with GUI-client, database manipulation, policy compilation and Management HA synchronization.
After having saved the Clish Configuration with the "save configuration config.txt" command, where can you find the config.txt file?
In which VPN community is a satellite VPN gateway not allowed to create a VPN tunnel with another satellite VPN gateway?
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
According to out of the box SmartEvent policy, which blade will automatically be correlated into events?
Aaron is a Syber Security Engineer working for Global Law Firm with large scale deployment of Check Point Enterprise Appliances running GAiA R81.X The Network Security Developer Team is having an issue testing the API with a newly deployed R81.X Security Management Server Aaron wants to confirm API services are working properly. What should he do first?
What is the recommended way to have a redundant Sync connection between the cluster nodes?
In terms of Order Rule Enforcement, when a packet arrives at the gateway, the gateway checks it against the rules in the top Policy Layer, sequentially from top to bottom Which of the following statements is correct?
Which VPN routing option uses VPN routing for every connection a satellite gateway handles?
Due to high CPU workload on the Security Gateway, the security administrator decided to purchase a new multicore CPU to replace the existing single core CPU. After installation, is the administrator required to perform any additional tasks?
According to the policy installation flow the transfer state (CPTA) is responsible for the code generated by the FWM. On the Security Gateway side a process receives them and first stores them Into a temporary directory. Which process is true for receiving these Tiles;
Choose the correct syntax to add a new host named “emailserver1” with IP address 10.50.23.90 using GAiA Management CLI?
The customer has about 150 remote access user with a Windows laptops. Not more than 50 Clients will be connected at the same time. The customer want to use multiple VPN Gateways as entry point and a personal firewall. What will be the best license for him?
What API command below creates a new host object with the name "My Host" and IP address of "192 168 0 10"?
Alice & Bob are concurrently logged In via SSH on the same Check Point Security Gateway as user "admin* however Bob was first logged in and acquired the lock Alice Is not aware that Bob is also togged in to the same Security Management Server as she is but she needs to perform very urgent configuration changes - which of the following GAlAclish command is true for overriding Bobs configuration database lock:
Which Mobile Access Application allows a secure container on Mobile devices to give users access to internal website, file share and emails?
Fill in the blank: The command ___________________ provides the most complete restoration of a R81 configuration.
Tom has been tasked to install Check Point R81 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
Fill in the blank: The R81 feature _____ permits blocking specific IP addresses for a specified time period.
If you needed the Multicast MAC address of a cluster, what command would you run?
How many images are included with Check Point TE appliance in Recommended Mode?
Sticky Decision Function (SDF) is required to prevent which of the following? Assume you set up an Active-Active cluster.
GAiA Software update packages can be imported and installed offline in situation where:
Check Point recommends configuring Disk Space Management parameters to delete old log entries when available disk space is less than or equal to?
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
Fill in the blank: Identity Awareness AD-Query is using the Microsoft _______________ API to learn users from AD.
Which of the following Windows Security Events will not map a username to an IP address in Identity Awareness?
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Stateful Mode configuration, chain modules marked with __________________ will not apply.
What key is used to save the current CPView page in a filename format cpview_”cpview process ID”.cap”number of captures”?
In what way is Secure Network Distributor (SND) a relevant feature of the Security Gateway?
What kind of information would you expect to see using the sim affinity command?
What is the recommended number of physical network interfaces in a Mobile Access cluster deployment?
You notice that your firewall is under a DDoS attack and would like to enable the Penalty Box feature, which command you use?
Fill in the blank: The R81 SmartConsole, SmartEvent GUI client, and _______ consolidate billions of logs and shows then as prioritized security events.
Capsule Connect and Capsule Workspace both offer secured connection for remote users who are using their mobile devices. However, there are differences between the two.
Which of the following statements correctly identify each product's capabilities?
For best practices, what is the recommended time for automatic unlocking of locked admin accounts?
Which file contains the host address to be published, the MAC address that needs to be associated with the IP Address, and the unique IP of the interface that responds to ARP request?
Vanessa is firewall administrator in her company. Her company is using Check Point firewall on a central and several remote locations which are managed centrally by R77.30 Security Management Server. On central location is installed R77.30 Gateway on Open server. Remote locations are using Check Point UTM-1570 series appliances with R75.30 and some of them are using a UTM-1-Edge-X or Edge-W with latest available firmware. She is in process of migrating to R81.
What can cause Vanessa unnecessary problems, if she didn’t check all requirements for migration to R81?
Pamela is Cyber Security Engineer working for Global Instance Firm with large scale deployment of Check Point Enterprise Appliances using GAiA/R81.10. Company’s Developer Team is having random access issue to newly deployed Application Server in DMZ’s Application Server Farm Tier and blames DMZ Security Gateway as root cause. The ticket has been created and issue is at Pamela’s desk for an investigation. Pamela decides to use Check Point’s Packet Analyzer Tool-fw monitor to iron out the issue during approved Maintenance window.
What do you recommend as the best suggestion for Pamela to make sure she successfully captures entire traffic in context of Firewall and problematic traffic?
Which file gives you a list of all security servers in use, including port number?
During the Check Point Stateful Inspection Process, for packets that do not pass Firewall Kernel Inspection and are rejected by the rule definition, packets are:
With MTA (Mail Transfer Agent) enabled the gateways manages SMTP traffic and holds external email with potentially malicious attachments. What is required in order to enable MTA (Mail Transfer Agent) functionality in the Security Gateway?
Joey wants to upgrade from R75.40 to R81 version of Security management. He will use Advanced Upgrade with Database Migration method to achieve this.
What is one of the requirements for his success?
What CLI command compiles and installs a Security Policy on the target’s Security Gateways?
Which of the following technologies extracts detailed information from packets and stores that information in state tables?
When deploying SandBlast, how would a Threat Emulation appliance benefit from the integration of ThreatCloud?
The fwd process on the Security Gateway sends logs to the fwd process on the Management Server via which 2 processes?
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
Where you can see and search records of action done by R81 SmartConsole administrators?
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
Which of the following is a new R81 Gateway feature that had not been available in R77.X and older?
To help SmartEvent determine whether events originated internally or externally you must define using the Initial Settings under General Settings in the Policy Tab. How many options are available to calculate the traffic direction?
What is a feature that enables VPN connections to successfully maintain a private and secure VPN session without employing Stateful Inspection?
You want to gather and analyze threats to your mobile device. It has to be a lightweight app. Which application would you use?
What are the attributes that SecureXL will check after the connection is allowed by Security Policy?
The Security Gateway is installed on GAIA R81. The default port for the Web User Interface is ______ .
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
Which command can you use to verify the number of active concurrent connections?
You can select the file types that are sent for emulation for all the Threat Prevention profiles. Each profile defines a(n) _____ or _____ action for the file types.
NAT rules are prioritized in which order?
1. Automatic Static NAT
2. Automatic Hide NAT
3. Manual/Pre-Automatic NAT
4. Post-Automatic/Manual NAT rules
Can multiple administrators connect to a Security Management Server at the same time?
: 131
Which command is used to display status information for various components?
Customer’s R81 management server needs to be upgraded to R81.10. What is the best upgrade method when the management server is not connected to the Internet?
With Mobile Access enabled, administrators select the web-based and native applications that can be accessed by remote users and define the actions that users can perform the applications. Mobile Access encrypts all traffic using:
Traffic from source 192.168.1.1 is going to www.google.com. The Application Control Blade on the gateway is inspecting the traffic. Assuming acceleration is enabled which path is handling the traffic?
To accelerate the rate of connection establishment, SecureXL groups all connection that match a particular service and whose sole differentiating element is the source port. The type of grouping enables even the very first packets of a TCP handshake to be accelerated. The first packets of the first connection on the same service will be forwarded to the Firewall kernel which will then create a template of the connection. Which of the these is NOT a SecureXL template?
John is using Management HA. Which Smartcenter should be connected to for making changes?
For Management High Availability, which of the following is NOT a valid synchronization status?
SmartConsole R81 requires the following ports to be open for SmartEvent R81 management:
SandBlast has several functional components that work together to ensure that attacks are prevented in real-time. Which the following is NOT part of the SandBlast component?
When Dynamic Dispatcher is enabled, connections are assigned dynamically with the exception of:
SandBlast offers flexibility in implementation based on their individual business needs. What is an option for deployment of Check Point SandBlast Zero-Day Protection?