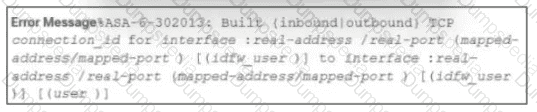
Refer to the exhibit.
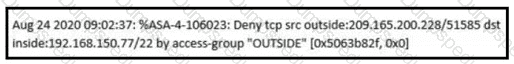
An analyst received this alert from the Cisco ASA device, and numerous activity logs were produced. How should this type of evidence be categorized?
What does an attacker use to determine which network ports are listening on a potential target device?
What is the key difference between mandatory access control (MAC) and discretionary access control (DAC)?
An analyst is investigating an incident in a SOC environment. Which method is used to identify a session from a group of logs?
What is the practice of giving employees only those permissions necessary to perform their specific role within an organization?
Refer to the exhibit.
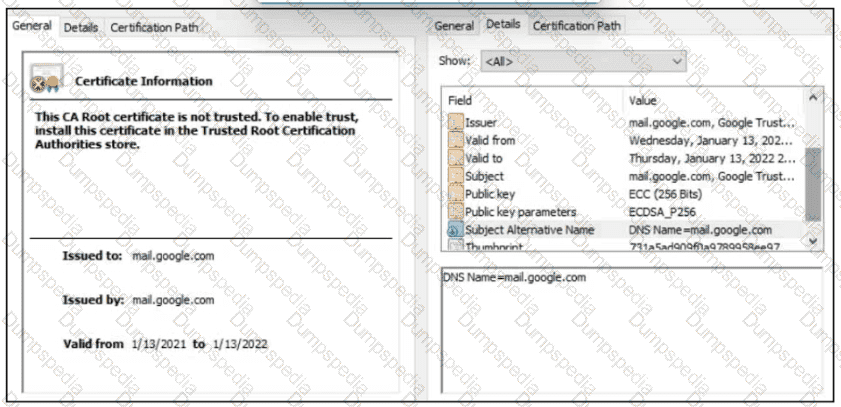
A company employee is connecting to mail google.com from an endpoint device. The website is loaded but with an error. What is occurring?
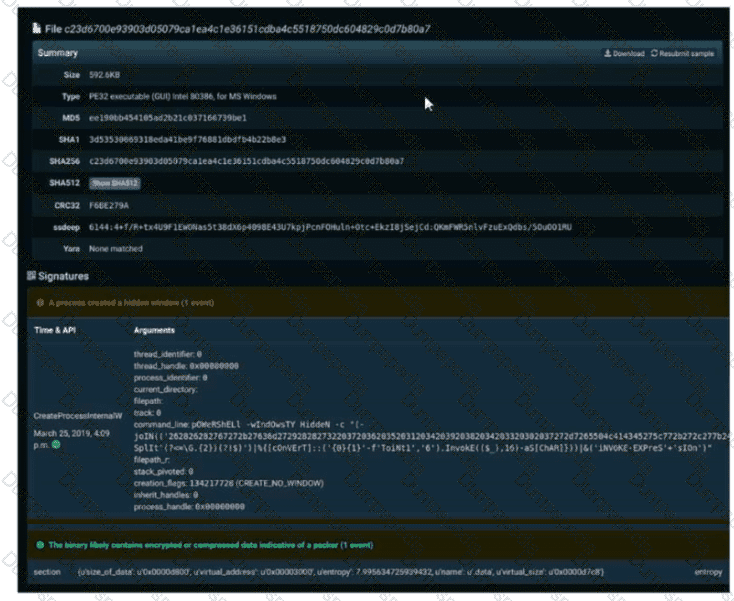
Refer to the exhibit. A SOC engineer is analyzing Cuckoo Sandbox report for a file that has been identified as suspicious by the endpoint security system. What is the state of the file?
Refer to the exhibit.
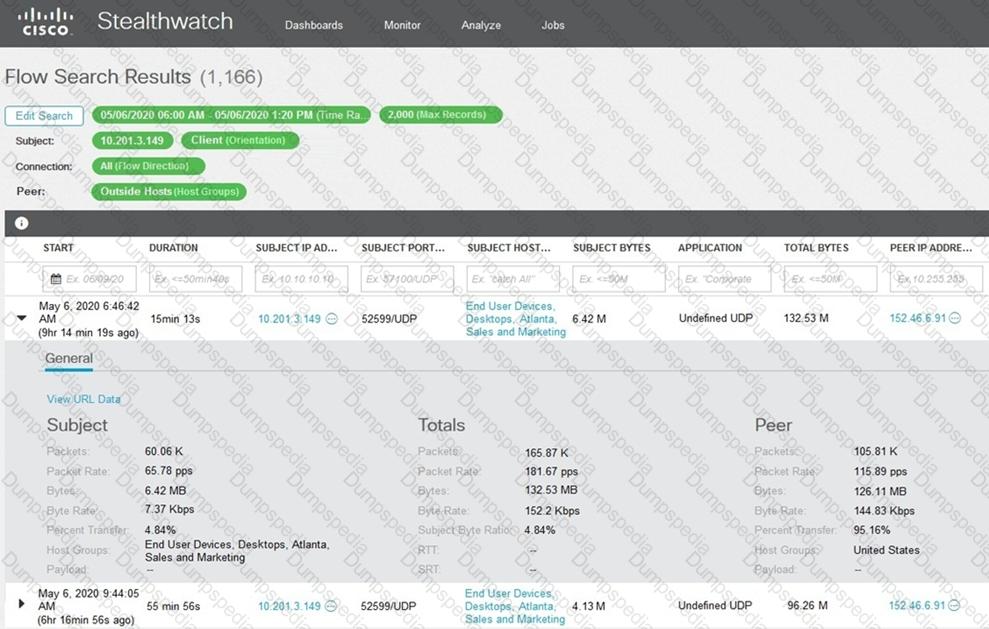
What is the potential threat identified in this Stealthwatch dashboard?
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
Which type of evidence supports a theory or an assumption that results from initial evidence?
An automotive company provides new types of engines and special brakes for rally sports cars. The company has a database of inventions and patents for their engines and technical information Customers can access the database through the company's website after they register and identify themselves. Which type of protected data is accessed by customers?
What describes the difference when comparing attack surface and vulnerability in practice?
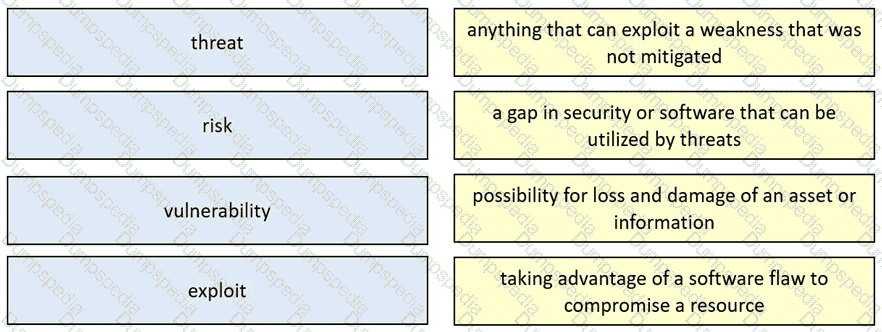
Drag and drop the security concept from the left onto the example of that concept on the right.
A security engineer deploys an enterprise-wide host/endpoint technology for all of the company's corporate PCs. Management requests the engineer to block a selected set of applications on all PCs.
Which technology should be used to accomplish this task?
An analyst is using the SIEM platform and must extract a custom property from a Cisco device and capture the phrase, "File: Clean." Which regex must the analyst import?
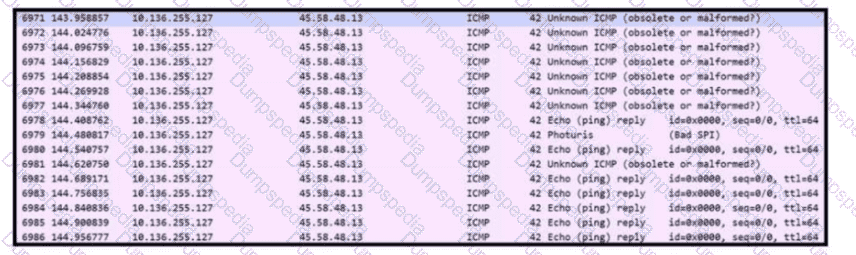
Refer to the exhibit
An engineer is analyzing DNS response packets that are larger than expected The engineer looks closer and notices a lack of appropriate DNS queries What is occurring?
What is a difference between inline traffic interrogation and traffic mirroring?
Refer to the exhibit.
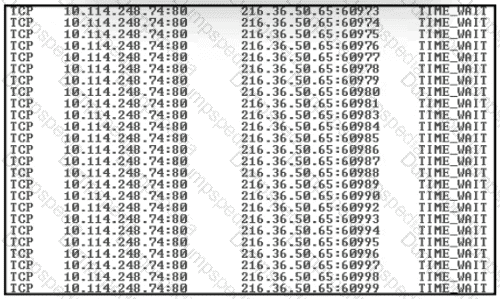
An engineer received a ticket about a slowed-down web application. The engineer runs the #netstat -an command. How must the engineer interpret the results?
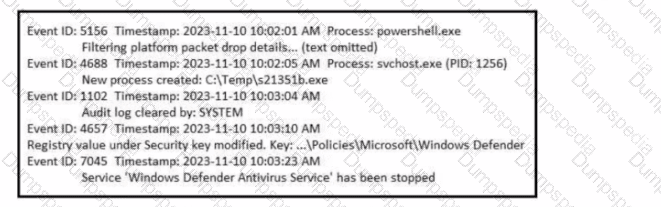
Refer to the exhibit. A SOC analyst is examining the Windows security logs of one of the endpoints. What is the possible reason for this event log?
An engineer needs to fetch logs from a proxy server and generate actual events according to the data received. Which technology should the engineer use to accomplish this task?
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
An organization has recently adjusted its security stance in response to online threats made by a known hacktivist group.
What is the initial event called in the NIST SP800-61?
An analyst received a ticket about degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed disabled antivirus software and could not determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
An engineer runs a suspicious file in a sandbox analysis tool to see the outcome. The analysis report shows that outbound callouts were made post infection.
Which two pieces of information from the analysis report are needed to investigate the callouts? (Choose two.)
The SOC team detected an ongoing port scan. After investigation, the team concluded that the scan was targeting the company servers. According to the Cyber Kill Chain model, which step must be assigned to this type of event?
What is a difference between rule-based and role-based access control mechanisms?
Which technology should be used to implement a solution that makes routing decisions based on HTTP header, uniform resource identifier, and SSL session ID attributes?
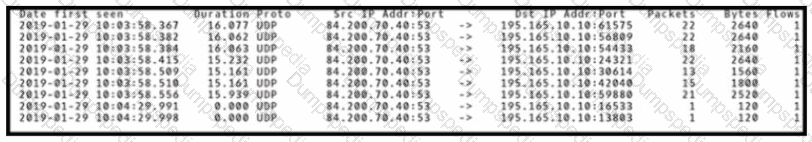
Refer to the exhibit. An engineer received a ticket to analyze unusual network traffic. What is occurring?
Which security model assumes an attacker within and outside of the network and enforces strict verification before connecting to any system or resource within the organization?
A company recently encountered a breach. Critical services went through a disturbance and the integrity of the data was altered. An engineer is investigating the issue and searching through the logs in the SIEM. Which phase of the incident response is an engineer working on?
What is the difference between the rule-based detection when compared to behavioral detection?
Refer to exhibit.
An analyst performs the analysis of the pcap file to detect the suspicious activity. What challenges did the analyst face in terms of data visibility?
An engineer needs to have visibility on TCP bandwidth usage, response time, and latency, combined with deep packet inspection to identify unknown software by its network traffic flow. Which two features of Cisco Application Visibility and Control should the engineer use to accomplish this goal? (Choose two.)
An investigator is examining a copy of an ISO file that is stored in CDFS format. What type of evidence is this file?
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
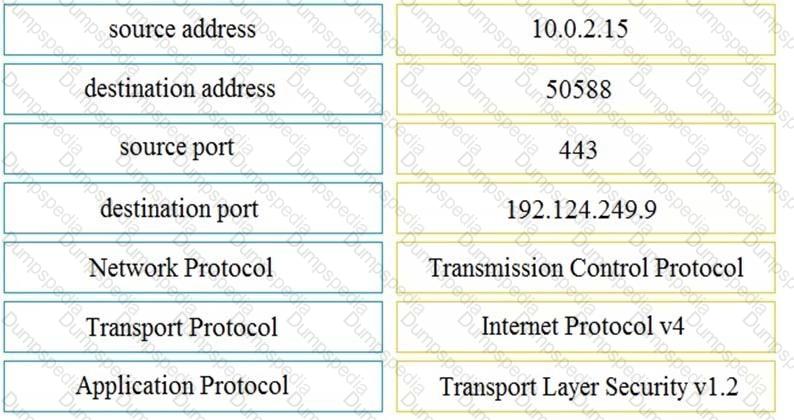
Refer to the exhibit.
Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
At a company party a guest asks questions about the company’s user account format and password complexity. How is this type of conversation classified?
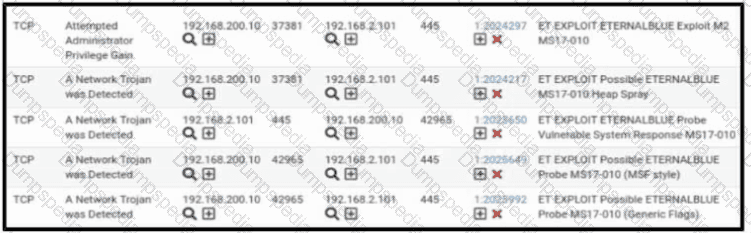
Refer to the exhibit. A security engineer receives several alerts from the SNORT IPS/IDS reporting malicious traffic. What should the engineer understand by examining the SNORT logs?
A security expert is working on a copy of the evidence, an ISO file that is saved in CDFS format. Which type of evidence is this file?
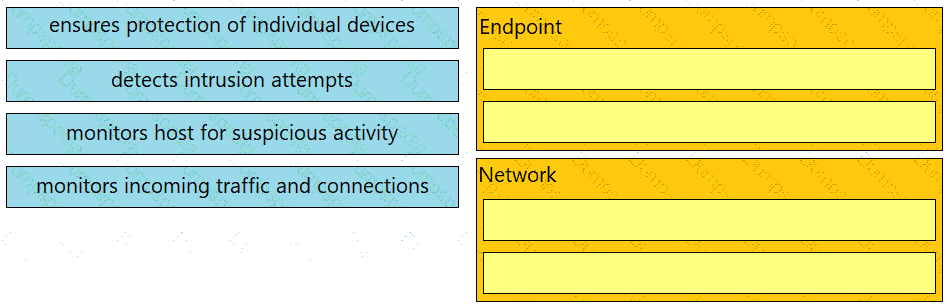
Drag and drop the uses on the left onto the type of security system on the right.
Refer to the exhibit.
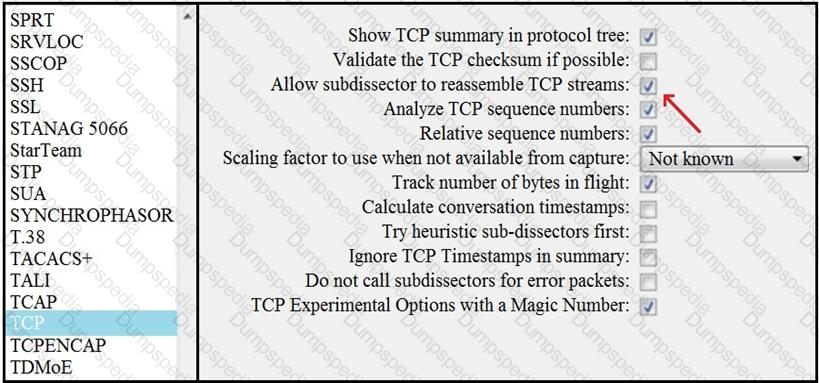
What is the expected result when the "Allow subdissector to reassemble TCP streams" feature is enabled?
A compliance analyst receives a complaint from a customer regarding personal data being unlawfully retained despite a deletion request. The company is based in Europe and must comply with GDPR. The only data collected is the email address 0524l9i75@gmail.com. How should the compliance analyst act?
What are two differences between tampered disk images and untampered disk images'? (Choose two.)
Refer to the exhibit.
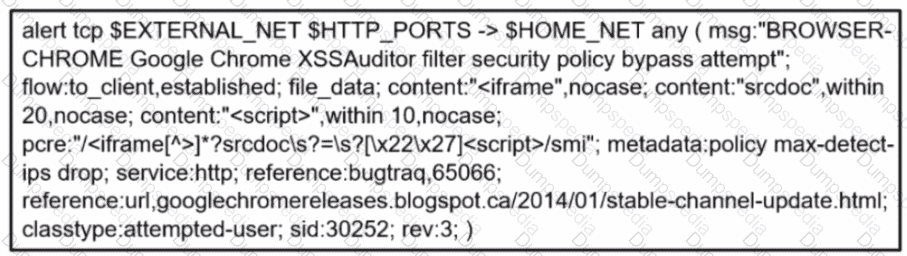
A company's user HTTP connection to a malicious site was blocked according to configured policy What is the source technology used for this measure'?
Which two elements are assets in the role of attribution in an investigation? (Choose two.)
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load. What is the next step the engineer should take to investigate this resource usage?
Which security principle is violated by running all processes as root or administrator?
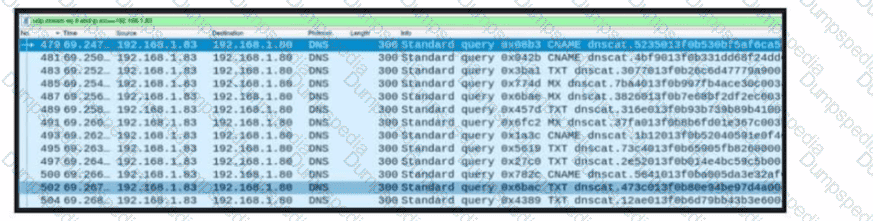
Refer to the exhibit. A network engineer received a report that a host is communicating with unknown domains on the internet. The network engineer collected packet capture but could not determine the technique or the payload used. What technique is the attacker using?
What is a difference between authorization and authentication from an access control perspective?
What describes the impact of false-positive alerts compared to false-negative alerts?
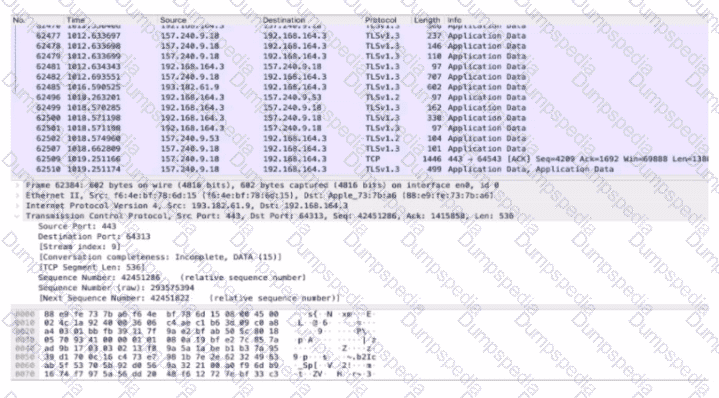
Refer to the exhibit.
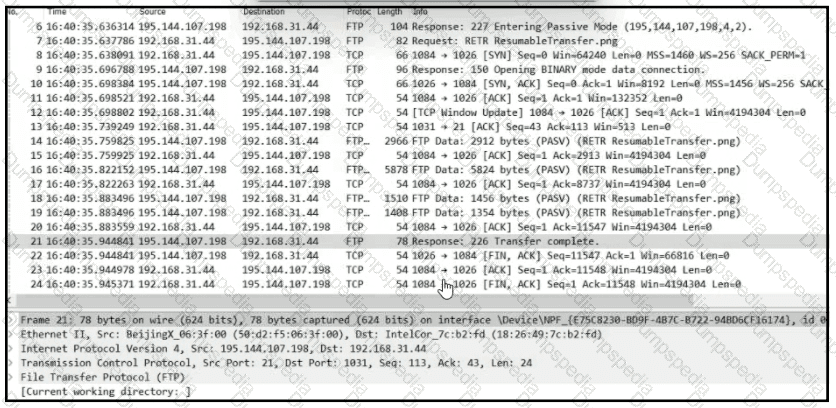
Which frame numbers contain a file that is extractable via TCP stream within Wireshark?
What is a benefit of agent-based protection when compared to agentless protection?
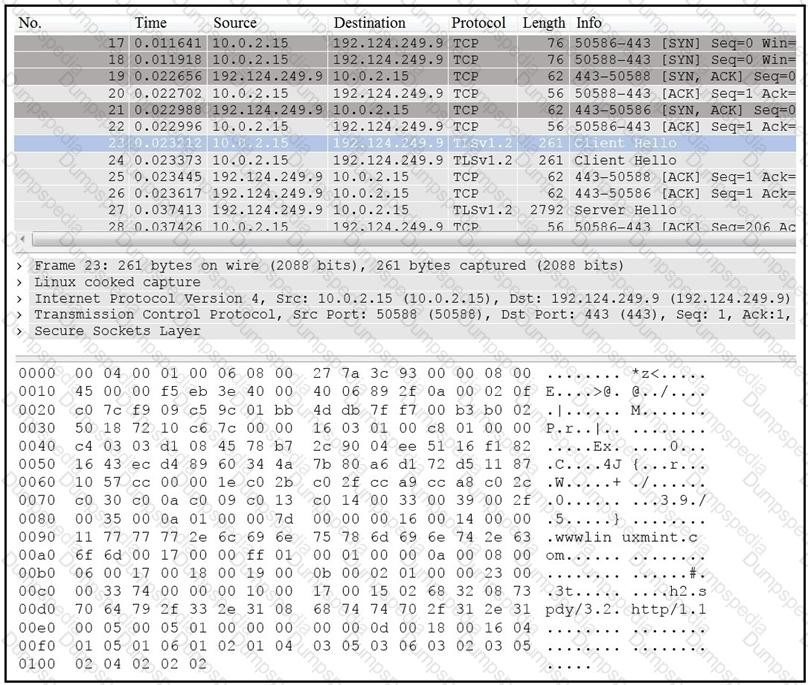
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
What is the difference between statistical detection and rule-based detection models?
A data privacy officer at a marketing firm has received a request from a former client to delete all personally sensitive information held by the company. The firm operates globally and follows international data protection standards. The only information retained about the client is a unique customer ID, "051473912", which is not directly tied to the name, address, or any other identifiable details. Which action should the data privacy officer take?
An organization recently experienced a major incident in which servers were attacked and data integrity was compromised. The attacker exploited a vulnerability in TLS 1.2 and performed a man-in-the-middle attack by downgrading the connection. Which action should a security specialist take to prevent similar attacks in the future?
Refer to the exhibit.
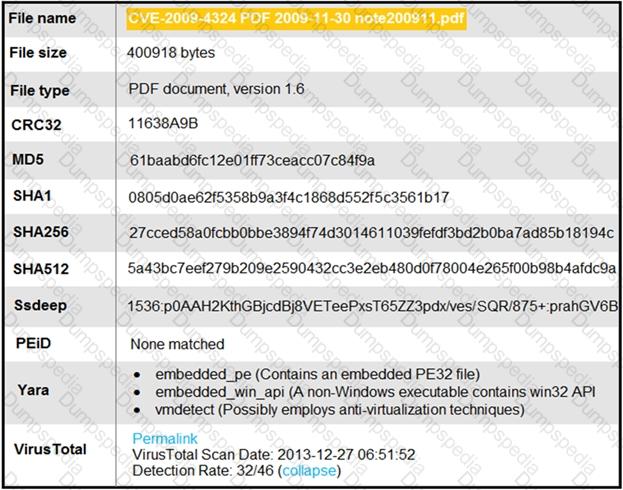
An engineer is analyzing this Cuckoo Sandbox report for a PDF file that has been downloaded from an email. What is the state of this file?
What is the difference between the ACK flag and the RST flag in the NetFlow log session?
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action. Which type of evidence has the company presented?
If a web server accepts input from the user and passes it to a bash shell, to which attack method is it vulnerable?
When an event is investigated, which type of data provides the investigate capability to determine if data exfiltration has occurred?
Refer to the exhibit.
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
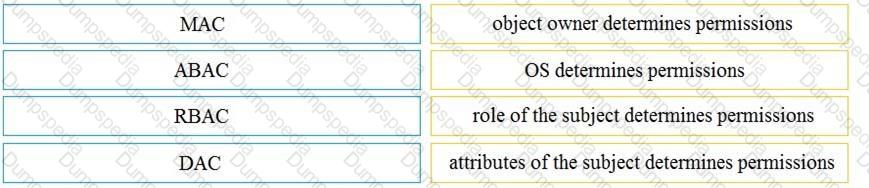
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
A user reports difficulties accessing certain external web pages. When an engineer examines traffic to and from the external domain in full packet captures, they notice that many SYNs have the same sequence number, source, and destination IP address, but they have different payloads. What is causing this situation?
After a large influx of network traffic to externally facing devices, a security engineer begins investigating what appears to be a denial of service attack When the packet capture data is reviewed, the engineer notices that the traffic is a single SYN packet to each port Which type of attack is occurring?
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
A member of the SOC team is checking the dashboard provided by the Cisco Firepower Manager for further Isolation actions. According to NIST SP800-61, in which phase of incident response is this action?
Refer to the exhibit.
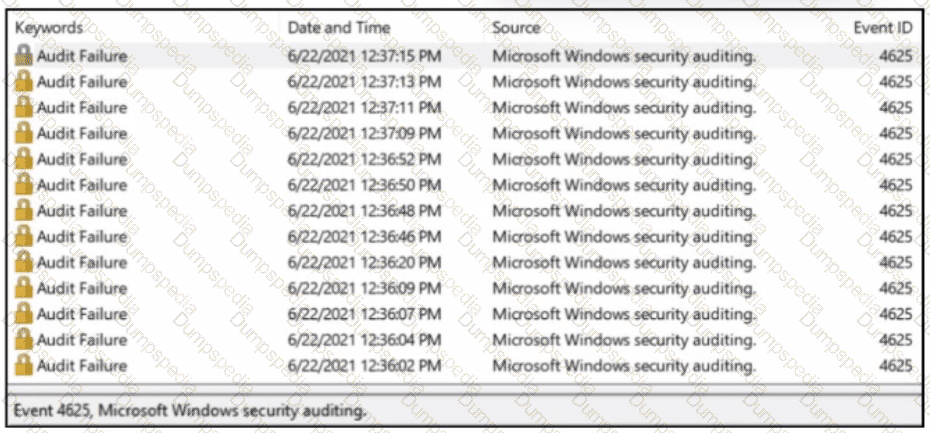
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
An engineer must configure network systems to detect command-and-control communications by decrypting ingress and egress perimeter traffic and allowing network security devices to detect malicious outbound communications. Which technology must be used to accomplish this task?
A large load of data is being transferred to an external destination via UDP 53 port. Which obfuscation technique is used?
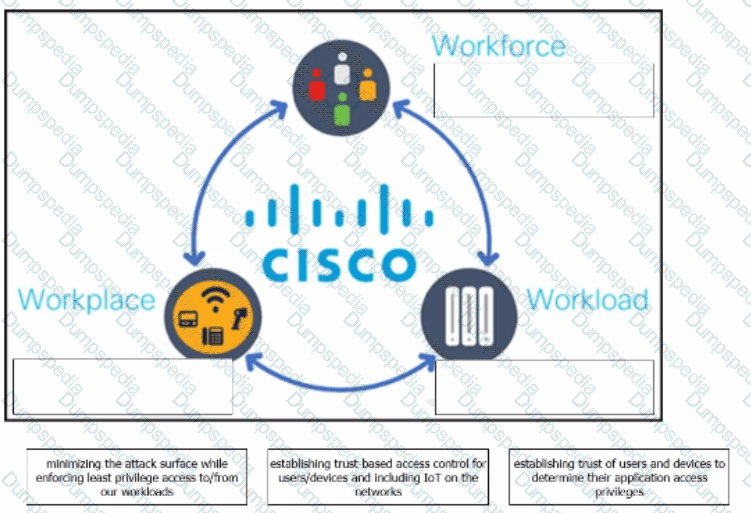
The Cisco Zero Trust Architecture simplifies the zero trust journey into three critical areas. Drag and drop the definitions onto the graphic to describe zero trust from the Cisco perspective.
An engineer is addressing a connectivity issue between two servers where the remote server is unable to establish a successful session. Initial checks show that the remote server is not receiving an SYN-ACK while establishing a session by sending the first SYN. What is causing this issue?
Which access control should a chief information security officer select to protect extremely sensitive data categorized at various levels of confidentiality?
A company is using several network applications that require high availability and responsiveness, such that milliseconds of latency on network traffic is not acceptable. An engineer needs to analyze the network and identify ways to improve traffic movement to minimize delays. Which information must the engineer obtain for this analysis?
A security incident occurred with the potential of impacting business services. Who performs the attack?
A security engineer must determine why a new core application does not work as desired The client can send requests toward the application server but receives no response One of the requirements is to gather all packets Data needs to be reliable without any delay or packet drops Which solution best meets this need?
A network engineer noticed in the NetFlow report that internal hosts are sending many DNS requests to external DNS servers A SOC analyst checked the endpoints and discovered that they are infected and became part of the botnet Endpoints are sending multiple DNS requests but with spoofed IP addresses of valid external sources What kind of attack are infected endpoints involved in1?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
Which evasion method involves performing actions slower than normal to prevent detection?
An engineer is analyzing a recent breach where confidential documents were altered and stolen by the receptionist. Further analysis shows that the threat actor connected an externa USB device to bypass security restrictions and steal data. The engineer could not find an external USB device Which piece of information must an engineer use for attribution in an investigation?
What are two differences in how tampered and untampered disk images affect a security incident? (Choose two.)
Drag and drop the access control models from the left onto the correct descriptions on the right.
Refer to the exhibit.
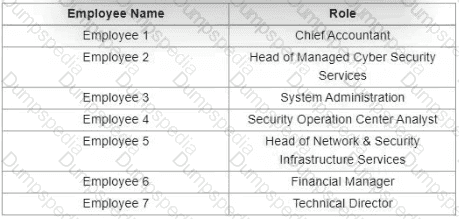
Which stakeholders must be involved when a company workstation is compromised?
Which type of attack involves sending input commands to a web server to access data?
A software development company develops high-end technology for the customer that will go through the HIPAA audit program. The technology will be hosted in the cloud, and the healthcare, employee names, and contact information will be stored on two separate logically isolated private cloud services. The patents and inventions will be hosted on a separate encrypted database. A compliance team is asked to analyze the cloud infrastructure and architecture to identify the protected data. Which two types of protected data should be identified? (Choose two.)
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?