When a wireless client roams between two different wireless controllers, a network connectivity outage is experience for a period of time. Which configuration issue would cause this problem?
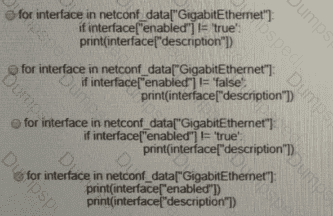
Refer to the exhibit. Which python code snippet prints the descriptions of disabled interface only?
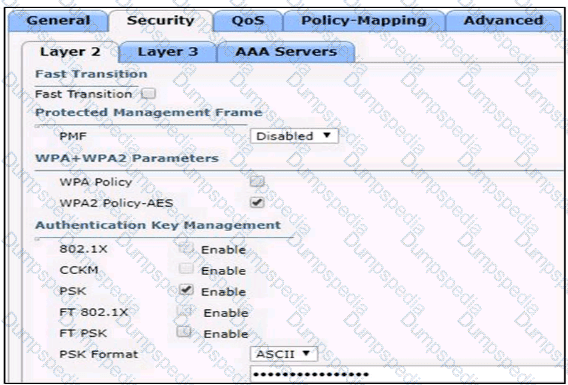
Based on the configuration in this WLAN security setting,Which method can a client use to authenticate to the network?
Which new security enhancement is introduced by deploying a next-generation firewall at the data center in addition to the Internet edge?
Which two methods are used to assign security group tags to the user in a Cisco Trust Sec architecture? (Choose two.)
Which HTTP status code is the correct response for a request with an incorrect password applied to a REST API session?
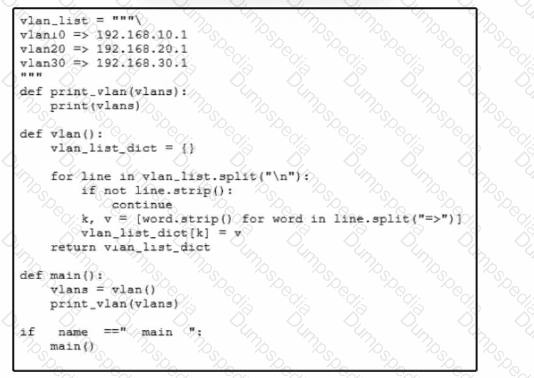
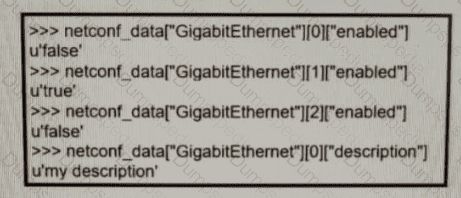
Refer to the exhibit A network engineer must use a Python script lo convert data received from a network device. Which type of data is printed to the console when the script runs?
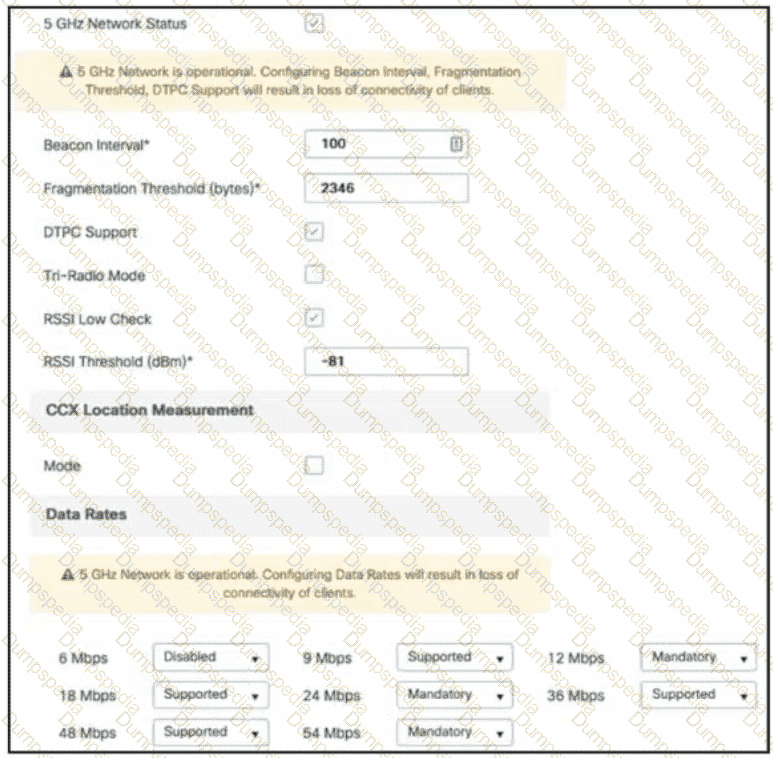
Refer to the exhibit. A customer reports that many wireless clients cannot reliably receive multicast audio. Which action resolves this issue?
An engineer configures a WLAN with fast transition enabled Some legacy clients fail to connect to this WLAN Which feature allows the legacy clients to connect while still allowing other clients to use fast transition based on then OLTIs?
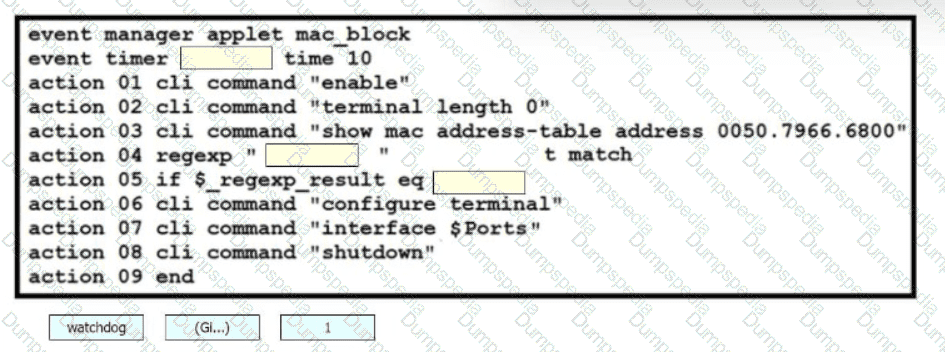
Drag and drop the snippets onto the blanks within the code to construct a script that blocks a MAC address.
Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
Which protocol is used by vmanage to push centralized policies to vsmart controllers?
Refer to the exhibit.

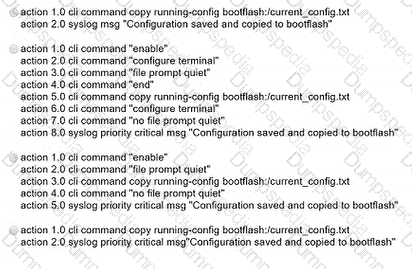
Which EEM script generates a critical-level syslog message and saves a copy of the running configuration to the bootflash when an administrator saves the running configuration to the startup configuration?