The Chief Security Officer (CSO) of an organization would like to have a network security assessment done by the security team. Which of the following is the FIRST step in the security testing methodology?
An organization is implementing an enterprise resource planning system using the traditional waterfall Software development Life Cycle (SDLC) model. When is the BEST time to perform a code review to identity security gaps?
What are the FIRST two steps an organization should conduct to classify its assets?
A manufacturer begins production of an item when a customer order is placed. This is an example of a(n):
An organizational policy requires that any data from organization-issued devices be securely destroyed before disposal. Which method provides the BEST assurance of data destruction?
A work center has 3 machines that are all run at the same time with a single worker. The work center has an efficiency of 75% and a utilization of 100%. What is the work center ' s capacity in standard hours for an 8-hour shift?
Bad actors with little expense can easily make calls. Which social engineer strategy is a telecommunications ONLY risk concept?
A manufacturer has a forecasted annual demand of 1,000,000 units for a new product. They have to choose 1 of 4 new pieces of equipment to produce this product. Assume that revenue will be $10 per unit for all 4 options.
Which machine will maximize their profit if the manufacturer anticipates market demand will be steady for 3 years and there is no residual value for any of the equipment choices?
MachineFixed CostVariable Cost per UnitAnnual Capacity
AS100.000$6 00800,000 units
B$200,000$5 501.000,000 units
C$250,000$5 001,200,000 units
D$1 000.000$4 501 400.000 units
A planner has chosen to increase the order point for a raw material. Which of the following costs is most likely to increase?
A contractor hacked into an unencrypted session on an organization ' s wireless network. Which authentication configuration is MOST likely to have enabled this?
An organization wants to establish an information security program and has assigned a security analyst to put it in place. What is the NEXT step?
As the organization requires user friendly access to a new web-based application, a software developer decides to implement Single Sign-On (SSO). The developer uses the de-facto standard for web-based applications and the implementation includes the use of a JavaScript Object Notation (JSON) web token. With this information, which is the BEST way for the software developer to establish SSO capability?
Which of the following is the MOST significant flaw when using Federated Identity Management (FIM)?
Plans are being made to move an organization’s software systems to the cloud in order to utilize the flexibility and scalability of the cloud. Some of these software systems process highly sensitive data. The organization must follow strict legal requirements regarding the location of the highly sensitive data processed by the software systems. Which cloud model will BEST fit the organization’s requirements?
If all other factors remain the same, when finished goods inventory investment is increased, service levels typically will:
An attacker was able to identify an organization’s wireless network, collect proprietary network resource information, and capture several user credentials. The attacker then used that information to conduct a more sophisticated and impactful attack against the organization. Which method did the attacker MOST likely use to gather the initial information?
Which of the following methods is most often used to manage inventory planning variability across the supply chain?
Which of the following tools is used to evaluate the impact that a production plan has on capacity?
A security consultant is working with an organization to help evaluate a proposal received from a new managed security service provider. There are questions about the confidentiality and effectiveness of the provider ' s system over a period of time. Which of the following System And Organization Controls (SOC) report types should the consultant request from the provider?
A bank recently informed a customer that their account has been overdrawn after their latest transaction. This transaction was not authorized by the customer. Upon further investigation, it was determined by the security team that a hacker was able to manipulate the customer ' s pre-authenticated session and force a wire transfer of funds to a foreign bank account. Which type of attack MOST likely occurred?
The question below is based on the following alternative schedules for a lot of 1,200.
A company works 8-hour, single-shift days. Setups are 4 hours for Operation 20 and 4 hours for Operation 40. Each operation has multiple machines available.
Which of the following statements is correct?
Internet Small Computer Systems Interface (iSCSI) protocol relies on Transmission Control Protocol/Internet Protocol (TCP/IP). Which can be used maliciously to interrupt the flow of data. Which Information Technology (IT) component would be impacted by such a disruption?
Exhibit:
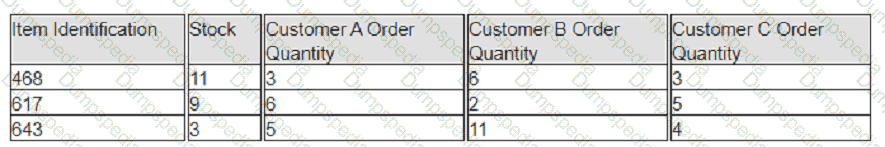
A company has prioritized customers A, B, and C, filling orders in that sequence. What are the impacts to customer service levels for customers B and C?
An organization is implementing improvements to secure the Software Development Life Cycle (SDLC). When should defensive three modeling occur?
Which of the following conditions is most likely to result in planned production that is greater than the total demand over the sales and operations planning (S & OP) horizon for a product family that is
made to stock?
Which of the following roles is the BEST choice for classifying sensitive data?
The demand for an item has increasing forecast error, whereas all other factors remain constant. Which of the following remains constant while maintaining the same customer service level?
Which of the following regarding authentication protocols is a PRIMARY consideration when designing an authentication and key management system?
During an investigation, a forensic analyst executed a task to allow for the authentication of all documents, data, and objects collected, if required. Which of the options below BEST describes this task?
Remote sensors have been deployed at a utility site to reduce overall response times for maintenance staff supporting critical infrastructure. Wireless communications are used to communicate with the remote sensors, as it is the most cost-effective method and minimizes risk to public health and safety. The utility organization has deployed a Host-Based Intrusion Prevention System (HIPS) to monitor and protect the sensors. Which statement BEST describes the risk that is mitigated by utilizing this security tool?
An organizations is developing a new software package for a financial institution. What is the FIRST step when modeling threats to this new software package?
An attacker wants to decrypt a message and has no knowledge of what may have been in the original message. The attacker chooses to use an attack that will exhaust the keyspace in order to decrypt the message. What type of cryptanalytic attack is the attacker using?
What priority control technique is most appropriate for a firm using a cellular production system?
A company that uses concurrent engineering is likely to experience which of the following outcomes in the first period of a product ' s life cycle?
What is the MAIN reason security is considered as part of the system design phase instead of deferring to later phases?
Which of the following Secure Shell (SSH) remote access practices is MOST suited for scripted functions?
A security practitioner notices that workforce members retain access to information systems after transferring to new roles within the organization, which could lead to unauthorized changes to the information systems.
This is a direct violation of which common security model?
Improvements in an Input/output control (I/O control) system will most likely lead to:
An organization intends to host an application on a multi-tenant Infrastructure as a Service (IaaS) platform. Which of the following measures are MOST important to ensure proper protection of sensitive information?
Which of the following are steps involved in the identity and access provisioning lifecycle?
A semiconductor manufacturer is writing a physical asset handling policy. Which of the following is MOST likely to be the rationale for the policy?
An support technician is contacted by an imposter claiming to be a supervisor and is asked specifically to perform a task that violates the organization’s security policies. What type of attack is this?
A company assembles kits of hand tools after receipt of the order from distributors and uses two-level master scheduling. The appropriate levels of detail for the forecasts that are input to master scheduling would be total number of kits and:
An organization has integrated its enterprise resource planning system into its centralized Identity and Access Management (IAM) system to automate provisioning of access. A security audit revealed that privileged access granted within the ERP system is not visible in the IAM system. Which of the following controls BEST mitigates this risk?
An organization co-locates three divisions and merges them into one network infrastructure. Prior to the merge, the network manager issued devices to employees for remote login. What security concept should be observed to provide security when a device joins the network or when a client makes an Application Programming Interface (API) call?
Which of the following BEST describes the purpose of black hat testing during an assessment?
Capacity requirements planning (CRP) is applicable primarily In companies operating In an environment where:
A forecasting method that responds slowly to changes in demand would be most appropriate when the historical demand pattern shows a:
The primary outcome of frequent replenishments in a distribution requirements planning (DRP) system is that:
A multinational organization acquires a subsidiary. The acquisition results in the need to integrate a large population of new users into the organization ' s corporate cloud. What is the MAIN benefit of the organization ' s Federated Identity Management (FIM) system to address the need?
A security engineer must address resource sharing between various applications without adding physical hardware to the environment. Which secure design principle is used to BEST segregate applications?
A department manager executes threat modeling at the beginning of a project and throughout its lifecycle. What type of threat modeling is being performed?
An organization has a legacy application used in production. Security updates are no longer provided, which makes the legacy application vulnerable. The legacy application stores Social Security numbers and credit card numbers. Which actions will BEST reduce the risk?
Which of the following mechanisms should a practitioner focus on for the MOST effective information security continuous monitoring?
In which cloud computing model is Identify And Access Management (IAM) the responsibility of a service provider?
What is the process when a security assessor compiles potential targets from the attacker’s perspective, such as data flows, and interactions with users?
During the sales and operations planning (S & OP) process, which of the following tasks is the primary responsibility of the functional representatives on the supply planning team?
What is an important countermeasure to consider when hardening network devices and servers to reduce the effectiveness of unauthorized network scanning?
An organization is having bandwidth utilization issues due to unauthorized devices on the network. Which action should be taken to solve the problem?
An organization’s computer incident responses team PRIMARY responds to which type of control?
In a Discretionary Access Control (DAC) model, how is access to resources managed?
Who is responsible for ensuring compliance when an organization uses a cloud provider to host its Virtual Machine (VM) instances?
Additional requirements that are outside the original design are being added to a project, increasing the timeline and cost of the project.
What BEST describes the requirement changes that are happening?
Following the setting of an organization’s risk appetite by senior management, a risk manager needs to prioritize all identified risks for treatment. Each risk has been scored based on its Annualized Loss Expectancy (ALE). Management has asked for an immediate risk mitigation plan focusing on top risks. Which is the MOST effective approach for the risk manager to quickly present a proposal to management?
Which is the MOST valid statement around the relationship of security and privacy?
Which of the following environments is most suitable for the use of kanban systems?
A security engineer is reviewing Incident Response (IR) roles and responsibilities. Several roles have static elevated privileges in case an incident occurs. Instead of static access, what is the BEST access method to manage elevated privileges?
An external audit is conducted on an organization ' s cloud Information Technology (IT) infrastructure. This organization has been using cloud IT services for several years, but its use is not regulated in any way by the organization and security audits have never been conducted in the past. Which task will be the MOST challenging to conduct an effective security audit?
A manufacturer has a primary assembly line supported by output from several subassembly lines. Which of the following scenarios would be the best argument for a multilevel master scheduling process?
A cybersecurity analyst is responsible for identifying potential security threats and vulnerabilities in the organization ' s software systems. Which action BEST demonstrates the understanding and application of threat modeling concepts and methodologies?
Which of the following is a core subset of The Open Group Architecture Framework (TOGAF) enterprise architecture model?
Which of the following incorporates design techniques promoted by Crime Prevention Through Environmental Design (CPTED)?
Which of the following circumstances would cause a move from acceptance sampling to 100% inspection?
If fixed costs are §200,000 and 20,000 units are produced, a unit ' s fixed cost is §10. This is an example of:
Which if the following is the FIRST control step in provisioning user rights and privileges?
Which software development methodology is an iterative customer-value-centric approach which helps teams deliver value to their customers faster and with fewer problems?
In the sales and operations planning (S & OP) process, the demand management function provides:
Which Open Systems Interconnection (OSI) layer is concerned with Denial-Of-Service (DoS) SYN flood attacks?
What is the PRIMARY benefit an organization obtains by adapting a cybersecurity framework to their cybersecurity program?
Which threat modeling methodology is focused on assessing risks from organizational assets?
According to best practice, at which step in the system lifecycle shall a security professional begin involvement?
An organization wants to implement Zero Trust (ZT). The Information Technology (IT) department is already using Multi-Factor Authentication (MFA) and Identity and Access Management (IAM). Which of the following would be the BEST solution for the organization to implement in order to have a ZT network?
Disaster Recovery Plan (DRP) training can be considered complete when the participants
A vendor has been awarded a contract to supply key business software. The vendor has declined all requests to have its security controls audited by customers. The organization insists the product must go live within 30 days. However, the security team is reluctant to allow the project to go live. What is the organization ' s BEST next step?
A company that has experienced steady growth for seasonal products in the last several years currently is reevaluating its production planning approach. The chase production plan initially requires 150 employees, then increases to 440 employees, and then decreases to 165 employees. Which of the following factors would be most relevant when evaluating the cost of this production planning approach?
An organization wants to ensure the security of communications across its environment. What is the BEST way to provide confidentiality of data from handheld wireless devices to the internal network?
During a threat modeling exercise using the Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege (STRIDE) framework, it was identified that a web server allocates a socket and forks each time it receives a request from a user without limiting the number of connections or requests.
Which of the following security objectives is MOST likely absent in the web server?
A low-cost provider strategy works best when which of the following conditions are met?
A potentially life-threatening vulnerability is found in vendor software that is used to manage critical systems. Which of the following is generally considered the BEST method to disclose the vulnerability from an ethical hacking perspective?
A web developer was recently asked to create an organization portal that allows users to retrieve contacts from a popular social media platform using Hypertext Transfer Protocol Secure (HTTPS). Which of the following is BEST suited for authorizing the resource owner to the social media platform?
A cloud-based web application requires the use of cryptographic keys to encrypt user-uploaded files at rest. Where is the safest place to store these cryptographic keys?
For a process that is outside its upper control limit (UCL), which of the following techniques would best be used to return the process under control?
In a lean environment, the batch-size decision for planning " A " items would be done by:
An organization suffered a loss to an asset at a frequency that was different than the initially estimated Annualized Rate of Occurrence (ARO). What is the appropriate course of action?
Which authentication method is used by an email server to verify that a sender’s Internet Protocol (IP) address is authorized to send messages by the sending domain?
A cybersecurity analyst is reviewing a recent incident in which the adversaries were able to move vertically within the network. Which attack phase MOST clearly represents this scenario?
The question below is based on the following standard and actual data of a production order
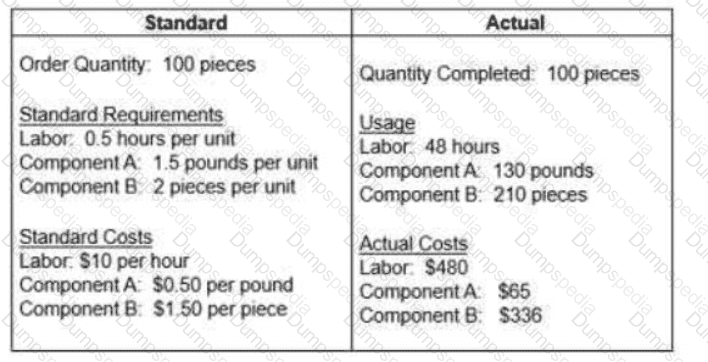
Which of the following statements about variances is true?
A company ' s primary performance objective Is flexibility. Which of the following measurements is most important?
An organization has hired a new auditor to review its critical systems infrastructure for vulnerabilities. Which of the following BEST describes the methodology the auditor will use?
Which of the following categories of web services testing describes correctness testing of web service security functionality?
Which of the following BEST describes how an Application Programming Interface (API) gateway fits into an application architecture?
An organization is designing a new Disaster Recovery (DR) site. What is the BEST option to harden security of the site?
A furniture manufacturer using material requirements planning (MRP) and lean manufacturing has changed the bills of material (BOMs) for all chests by making drawers into phantom assemblies. Which of the following outcomes would likely result from this change?
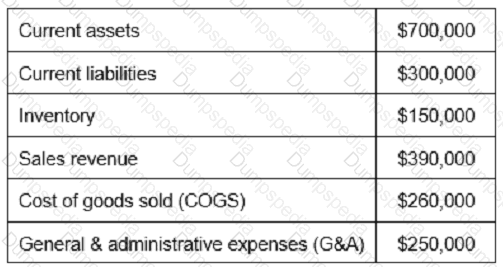
Based on the values reported in the table below, what is the inventory turnover?
An information security auditor is creating an audit program to assess endpoint security controls for portable storage media movement. Which type of control will MOST likely be part of the program?
Which of the following sampling techniques is BEST suited for comprehensive risk assessments?
A security analyst has been asked to build a data retention policy for a hospital. What is the FIRST action that needs to be performed in building this policy?
An appropriate performance measure for sales and operations planning (S & OP) would be the variance between:
Which role is MOST accountable for allocating security function resources in order to initiate the information security governance and risk management policy?
Which of the following MUST be checked during the validation of software verification capabilities?
Reducing distribution network inventory days of supply will have which of the following Impacts?
Payment Card Industry Data Security Standard (PCI DSS) allows for scanning a statistical sample of the environment without scanning the full environment. Scanning a statistical sample has many advantages and disadvantages.
Which of the following is the MOST accurate set of advantages and disadvantages?
A regular remote user executed an application that allowed the execution of commands with elevated permissions. It was allowed to create new users, start and stop services, and view critical log files. Which exploit type did the application use in this scenario?
Which of the following inventory management techniques is most responsive to changes in demand levels?
A third-party vendor is procured to conduct a non-financial audit. Which report evaluates the effectiveness of the controls?
Which of the following is the BEST way to identify the various types of software installed on an endpoint?
What is the MOST likely cause for a penetration tester having difficulties finding the stack to inject code?
An organization recently completed an acquisition of another entity and staff members are complaining about the excessive number of credentials they need to remember as each application requires separate logins. This is negatively affecting collaboration efficiency and increasing the risk of human errors. What will the organization consider implementing as part of the solution to improve the situation?
Which burden of proof has been applied when a workplace investigation has a 51 percent or greater certainty that allegations are true?
The primary consideration In maintenance, repair, and operating (MRO) supply systems typically is:
Which of the following represents the level of confidence that software is free from intentional an accidental vulnerabilities?
The master schedule is an Important tool in the sales and operations planning (S & OP) process because it:
Which of the following concepts MOST accurately refers to an organization ' s ability to fully understand the health of the data in its system at every stage of the lifecycle?
An organization recently created a new accounting department, and that department is critical in the event of a disaster for the operations to continue. Which steps should the organization take to create a Business Continuity Plan (BCP)?
Which of the following documents is the BEST reference to describe application functionality?
An organization has a requirement that all documents must be auditable and that the original is never modified once created. When designing the system, what security model MUST be implemented in order to meet this requirement?
An advantage of applying ABC classification to a firm ' s replenishment items is that:
Which of the following is the BEST type of fire extinguisher for a data center environment?
Which of the following items does the master scheduler have the authority to change in the master scheduling process?
What is most likely to be the effect of developing a current-state value stream map?
In the context of mobile device security, which of the following BEST describes why a walled garden should be implemented?
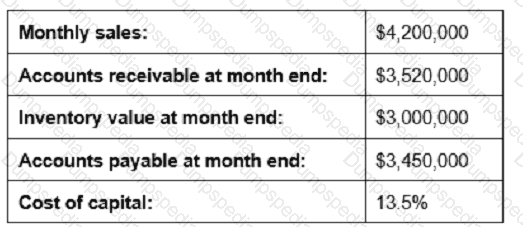
Given the information below, reducing which measure by 10% would contribute most to shortening the cash-to-cash cycle time?
An organization wishes to utilize a managed Domain Name System (DNS) provider to reduce the risk of users accessing known malicious sites when web browsing. The organization operates DNS forwarders that forward queries for all external domains to the DNS provider. Which of the following techniques could enable the organization to identify client systems that have attempted to access known malicious domains?
A stockout of dependent-demand item X occurred during the holiday season. To understand the root cause of the stockout, the planner should check if:
In Company XYZ, transaction-costing capability has been Integrated into the shop floor reporting system. A batch of 20 units was started in production. At the fourth operation, 20 units are reported as complete. At the fifth operation, 25 units are reported as complete. When all operations are complete, 20 units are checked into the stockroom. If the error at the fifth operation is undetected, which of the following conditions will be true?
An organization is attempting to address the security risk introduced by employees writing down door entry passcodes. Which of the following security measures BEST mitigates this risk?
Which of the following mechanisms are PRIMARILY designed to thwart side channel attacks?
A security practitioner has been asked to investigate the presence of customer Personally Identifiable Information (PII) on a social media website. Where does the practitioner begin?
Which of the following BEST effective when protecting against insider threats?
A newly hired Chief Information Security Officer (CISO) is now responsible to build a third-party assurance for their organization. When assessing a third-party, which of the following questions needs to be answered?
A traffic analysis on an organization ' s network identifies a significant degree of inefficient resource use as a result of broadcast traffic. The organization wants to reduce the scope of the broadcasts without impeding the flow of traffic. Which of the following devices is the BEST choice to implement to achieve this goal?
Which of the following is the GREATEST threat for a Border Gateway Protocol (BGP) deployment on the internet?
An organization has been struggling to improve their security posture after a recent breach. Where should the organization focus their efforts?
An infrastructure team is setting up a wireless network for employees at a new location of the organization that is located near a very busy city transport hub. Which should be the MOST important antenna consideration with regard to securing the wireless network for the infrastructure team?
A production manager completes a work order for an assembly item, and inventory records for the components are decreased. This is an example of:
Which of the following methods most likely Introduces a temporary variance between the inventory balance and the inventory record?
An organization is transitioning from a traditional server-centric infrastructure to a cloud-based Infrastructure. Shortly after the transition, a major breach occurs to the organization ' s databases. In an Infrastructure As A Service (IaaS) model, who would be held responsible for the breach?
An agency has the requirement to establish a direct data connection with another organization for the purpose of exchanging data between the agency and organization systems. There is a requirement for a formal agreement between the agency and organization. Which source of standards can the system owners use to define the roles and responsibilities along with details for the technical and security requirements?
A security professional is accessing an organization-issued laptop using biometrics to remotely log into a network resource. Which type of authentication method is described in this scenario?
The development team wants new commercial software to Integrate into the current systems. What steps can the security office take to ensure the software has no vulnerabilities?
To mitigate risk related to natural disasters, an organization has a separate location with systems and communications in place. Data must be restored on the remote systems before they are ready for use. What type of remote site is this?
An organization wants to control access at a high-traffic entrance using magnetic-stripe cards for identification. Which of the following is the BEST for the organization to utilize?