A technician is creating an MDM policy using hardening techniques that are unique to each user. Which of the following techniques is the technician using?
Which of the following is required to have a central log-in for a Windows computer?
Due to recent security issues, the finance department requires a shorter screensaver timeout. Which of the following should a technician use to accomplish this task?
Multiple users clicked a phishing link from a compromised email account. The security team isolates and removes the threat. Then, the management team provides security awareness training to the company. What step is this?
A user is seeing authentication errors in applications and certificate errors when browsing. A technician verifies the following:
• The gateway is reachable.
• The local server fileshares are accessible without issue.
Which of the following is the issue?
Which of the following concepts should a technician consider when discussing confidential work projects with individuals outside the company?
An end user is unable to access the intranet. A technician needs to confirm whether the Windows web server is online and functioning. Which of the following default remote access technologies would the technician most likely use to remotely connect to the server?
Which of the following methods involves requesting a user ' s approval via a push notification to verify the user ' s identity?
A technician wants to prevent electrical damage while disassembling a device. The technician turns off the device. Which of the following should the technician do next?
A Windows 11 Home device is receiving constant pop-ups about an urgent need to update antivirus software to remove a detected threat. The user has been clicking the " X " button in the window frame but it always reappears. The pop-up includes an " OK " button to install the update and remove the threat. Which of the following should the user do next?
A user ' s machine is infected with malware that the user ' s existing security software did not detect. Which of the following best explains the reason the infection was undetected?
A user wants to dispose of a failed hard drive in a way that ensures the data is unrecoverable. Which of the following is the best at-home method?
Which of the following describes an attack in which an attacker sets up a rogue AP that tricks users into connecting to the rogue AP instead of the legitimate network?
An administrator is investigating a zero-day vulnerability. If left unpatched, it could severely impact business. The patch requires downtime. What should the administrator do?
Which of the following methods would make data unrecoverable but allow the drive to be repurposed?
Recently, the number of users sharing smartphone passcodes has increased. The management team wants a technician to deploy a more secure screen lock method. Which of the following technologies should the technician use?
A user notices that their smartphone ' s data usage has increased significantly even when the device is not in use. The phone feels warm, and its battery drains quickly. Which of the following should the user do to address this issue?
A technician needs to map a shared drive from a command-line interface. Which of the following commands should the technician use?
Why would a network engineering team provide a help desk technician with IP addresses for a wired network segment?
Users access an internal application through a browser website. When a user is browsing the site, a message appears that states it is not safe. The message also displays an Advanced Options button to continue or close the site. During security training, all users were told to close any site that displays this message. Which of the following should the technician do to resolve the issue?
Which of the following provides information to employees, such as permitted activities when using the organization ' s resources?
A technician is using a credential manager to safeguard a large number of credentials. Which of the following is important for using this application?
A utility failure causes a workstation to immediately shut down. Which of the following would help prevent this from reoccurring?
An IT technician must install a new software application across Linux, macOS, and Windows systems within an organization. The installation files are stored on the intranet. Which of the following approaches should the technician take to ensure proper installation?
A user is unable to upload files to the corporate servers from their mobile phone when outside the office, but uploading files works without issue in the office. The user saw an error notification but dismissed it. Which of the following should a technician do to determine the root cause?
A customer wants to be able to work from home but does not want to be responsible for bringing company equipment back and forth. Which of the following would allow the user to remotely access and use a Windows PC at the main office? (Choose two.)
A technician is assigned to offboard a user. Which of the following are common tasks on an offboarding checklist? (Choose two.)
Technicians are failing to document user contact information, device asset tags, and a clear description of each issue in the ticketing system. Which of the following should a help desk management team implement for technicians to use on every call?
Which of the following malware types typically has very high computing resource usage?
A technician uses AI to draft a proposal about the benefits of new software. When reading the draft, the technician notices that the draft contains factually incorrect information. Which of the following best describes this scenario?
A user wants to use a USB to move a 4.57GB .pst file from one Windows computer to another. Which of the following filesystems should the USB be formatted with?
A technician needs to prevent accidental access to Wi-Fi networks available in a shared office space. The BYOD and company-owned devices already have Wi-Fi settings configured via MDM solutions. Which of the following settings should the technician change?
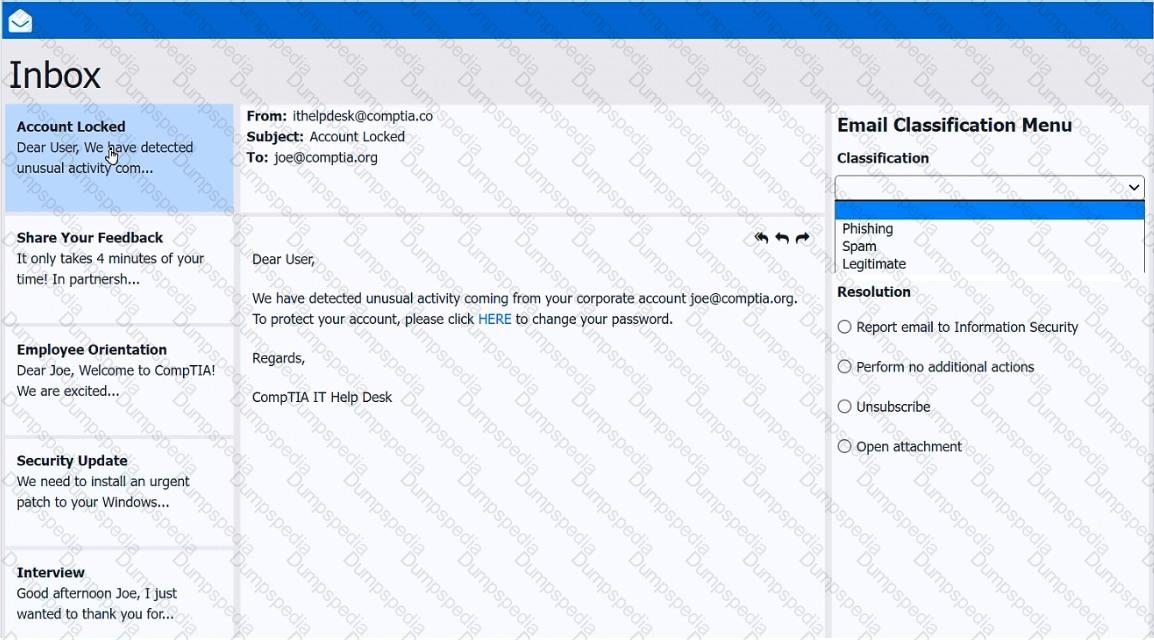
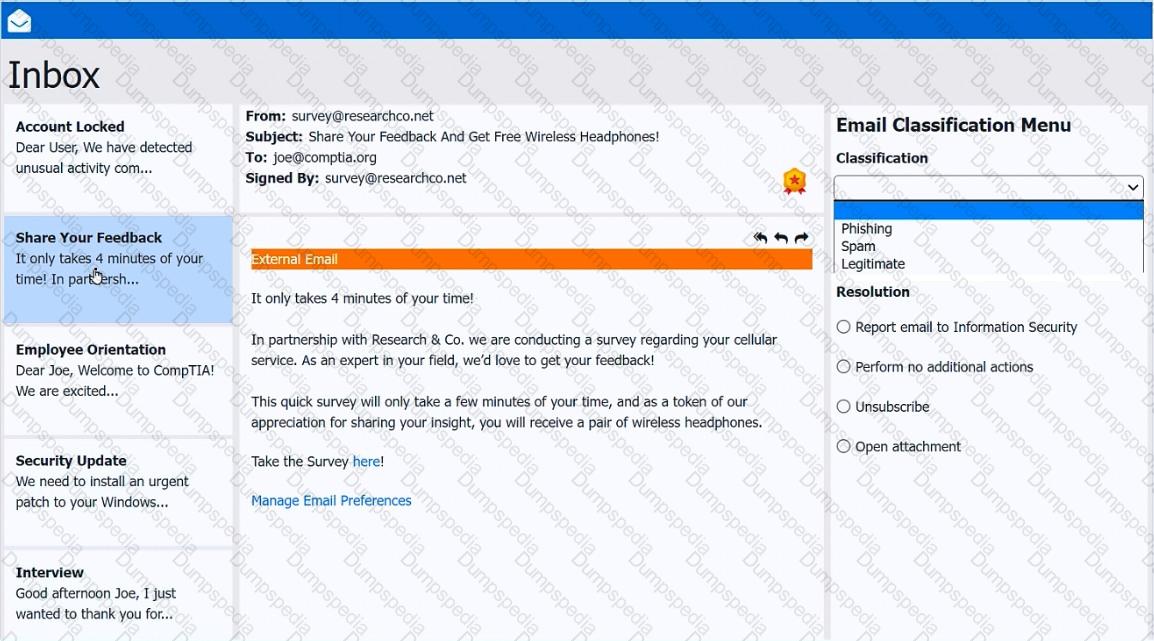
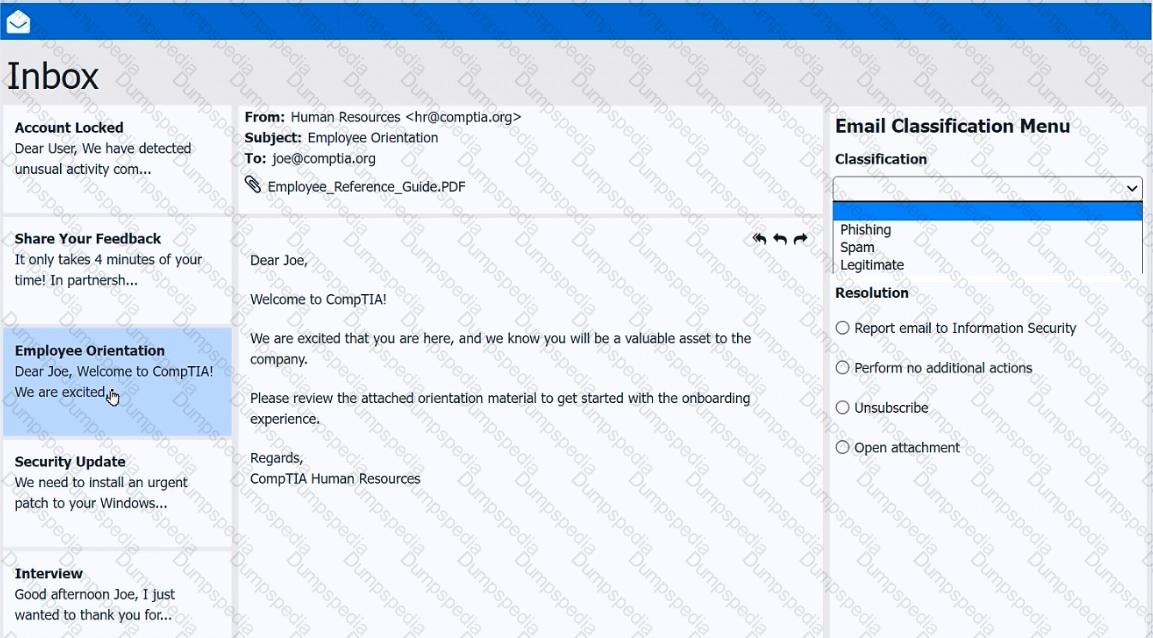
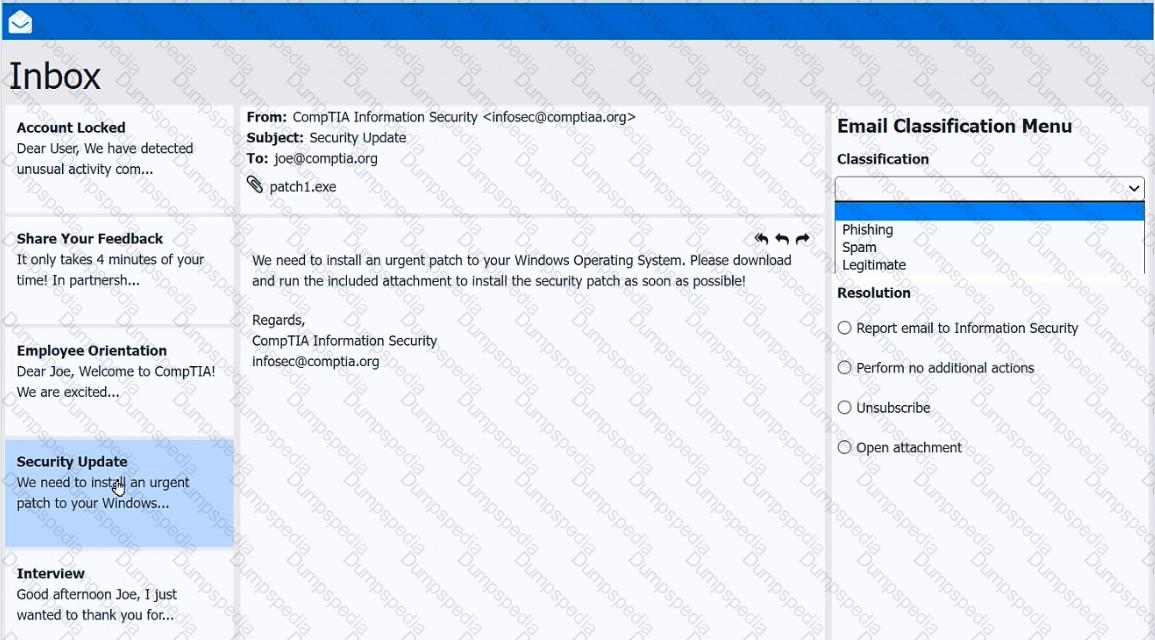
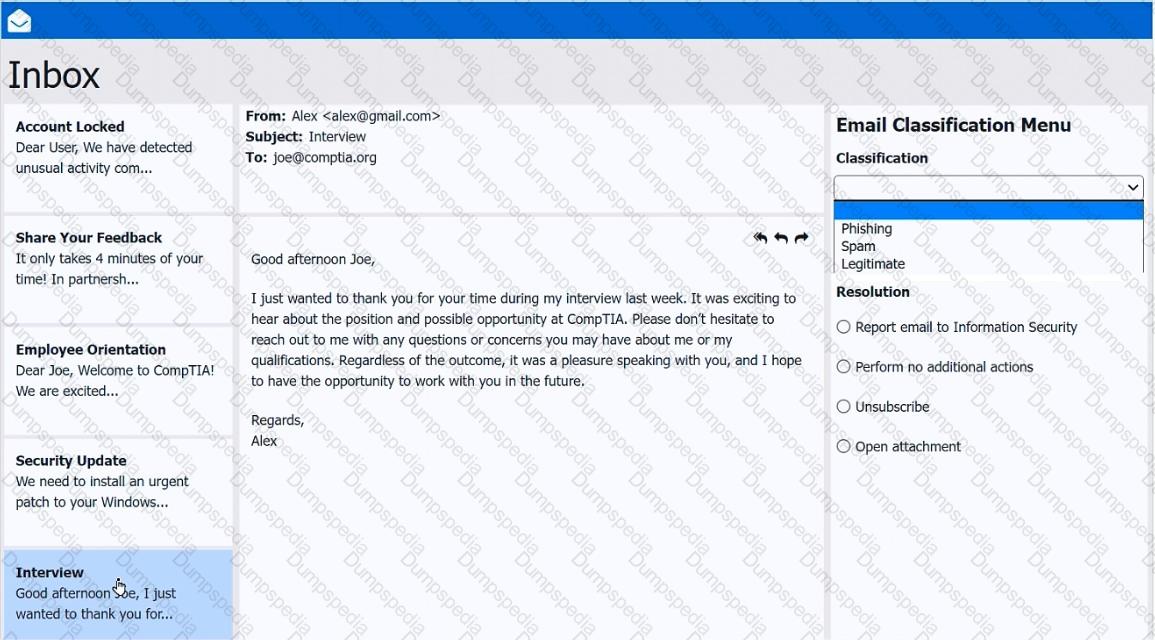
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A user is renaming a .txt file to a .xml file. After renaming the file, Windows Explorer shows the filename as Document….xml. However, the document properties show the type of file as Text Document (.txt). Which of the following controls enables the user to correctly change the file type?
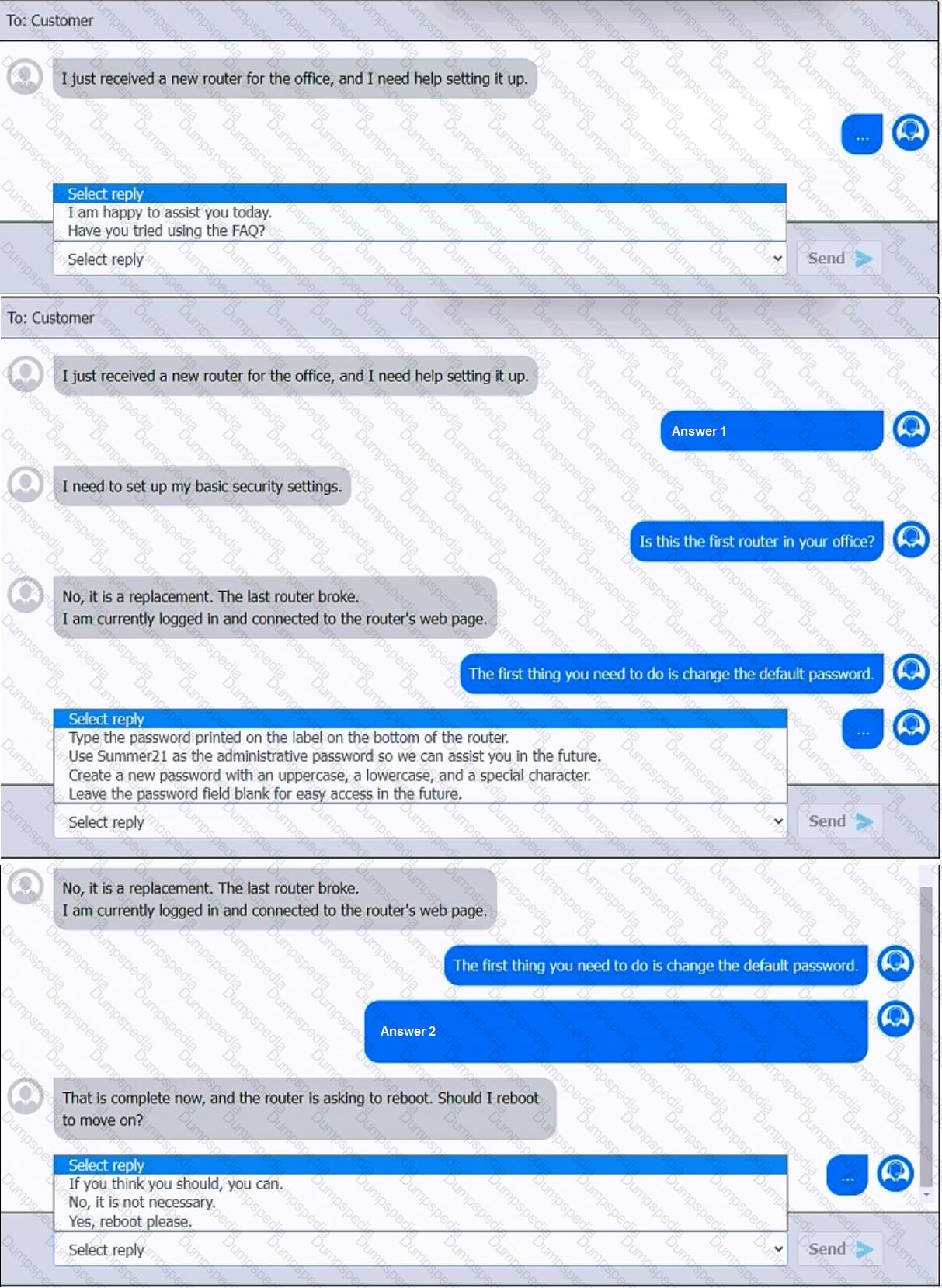
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
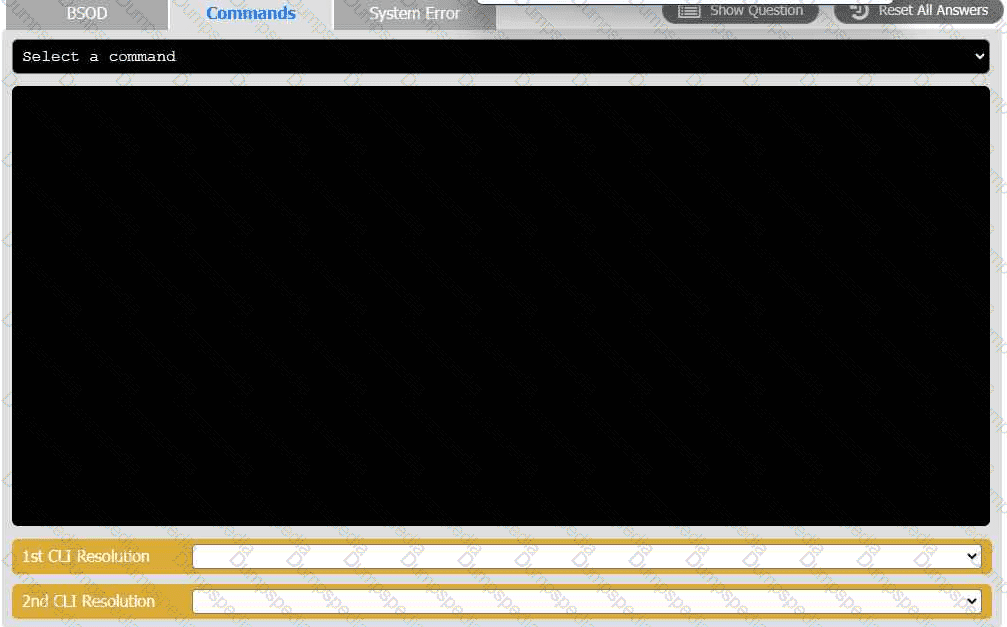
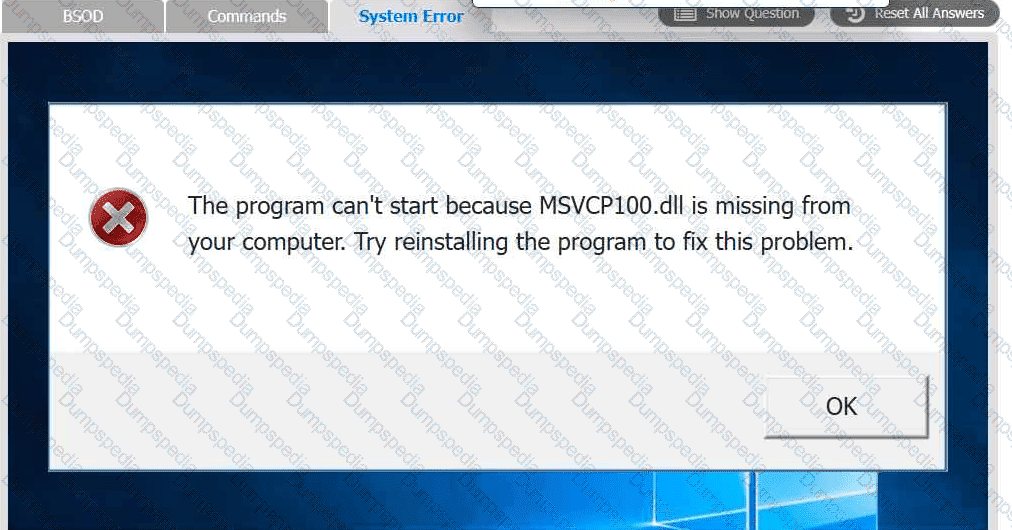
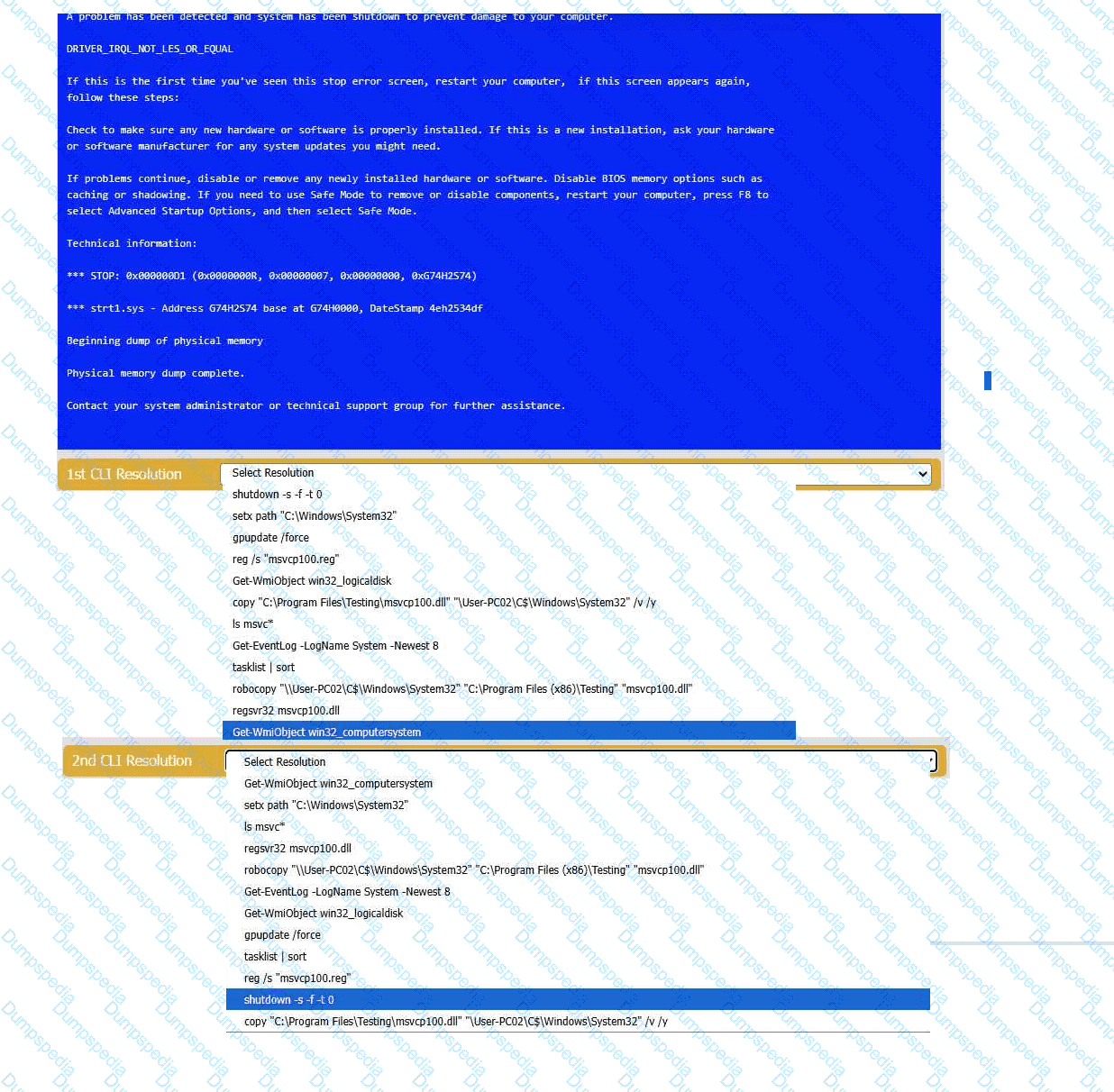
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
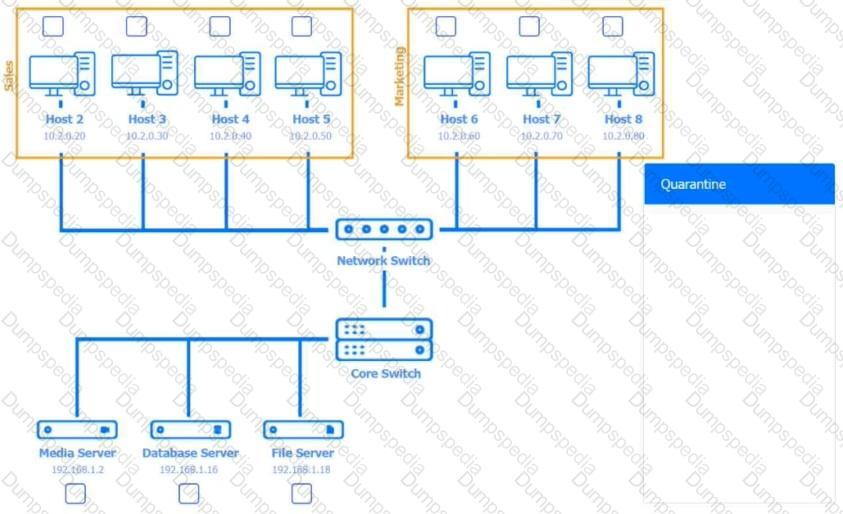
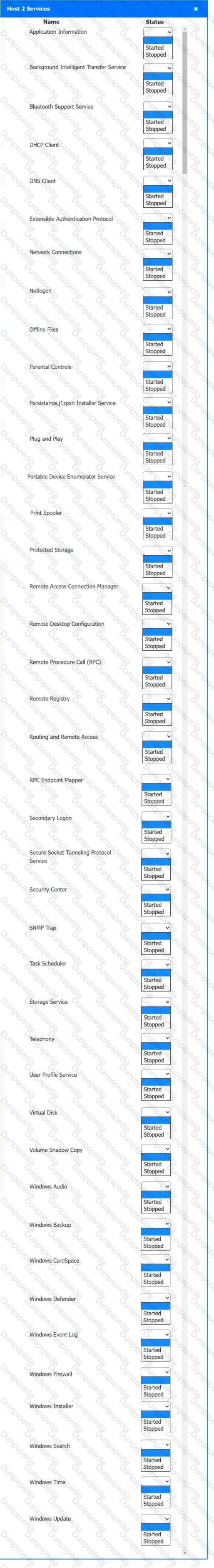
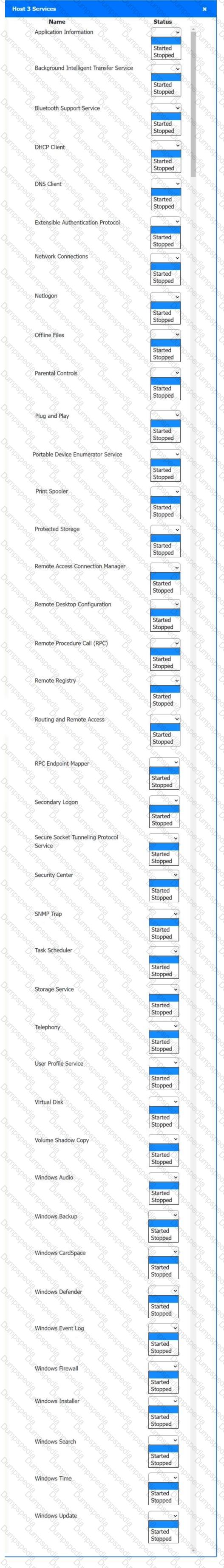
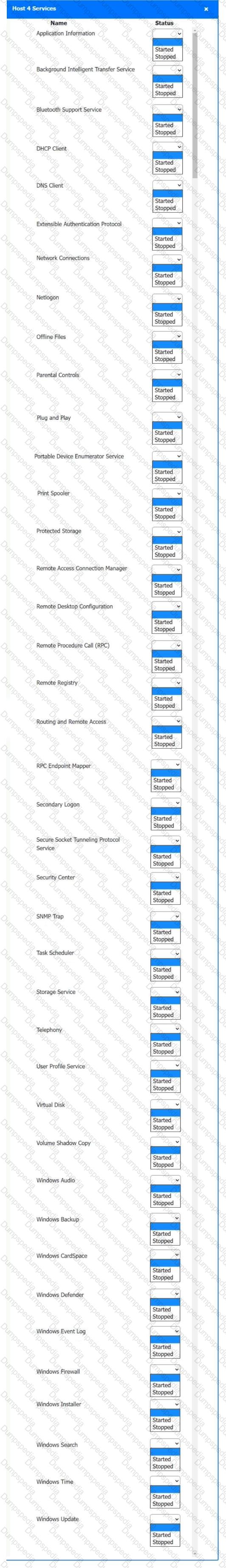
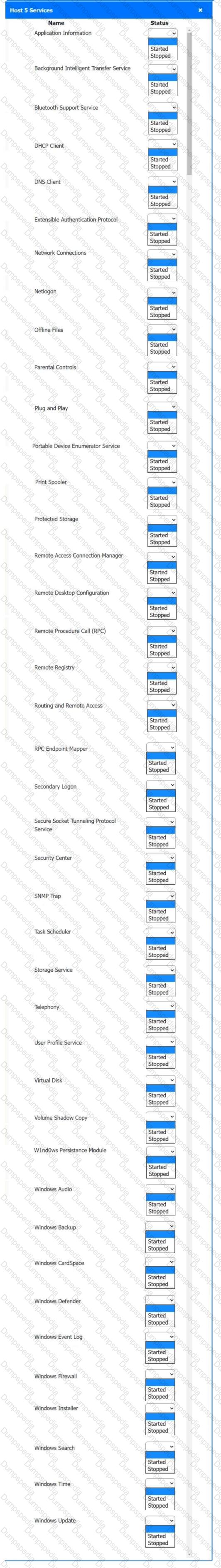
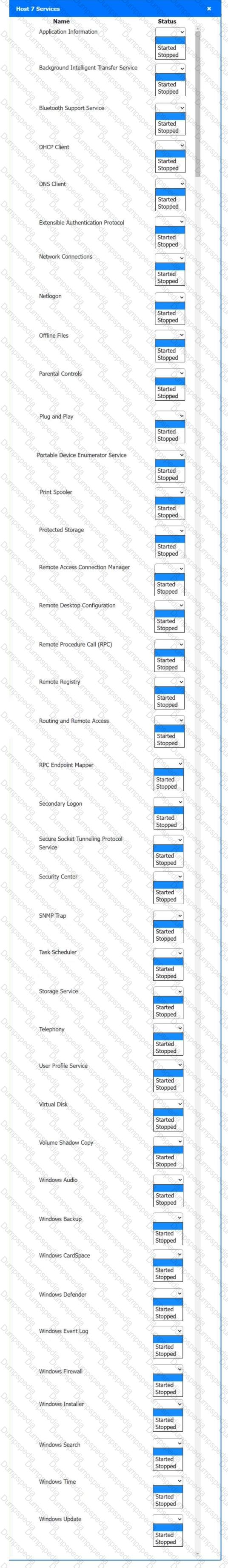
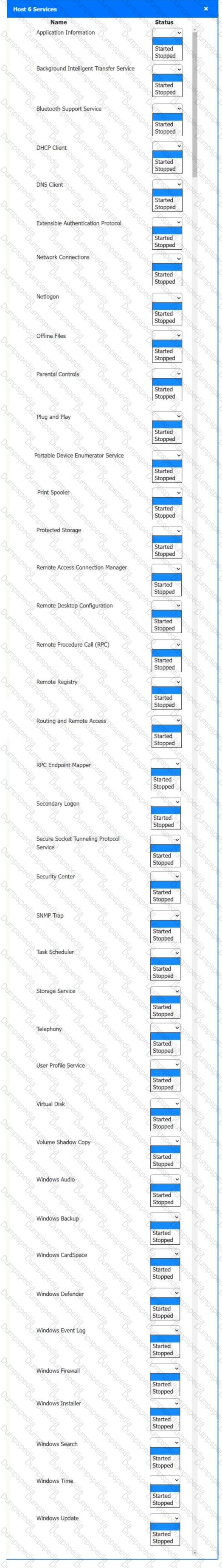
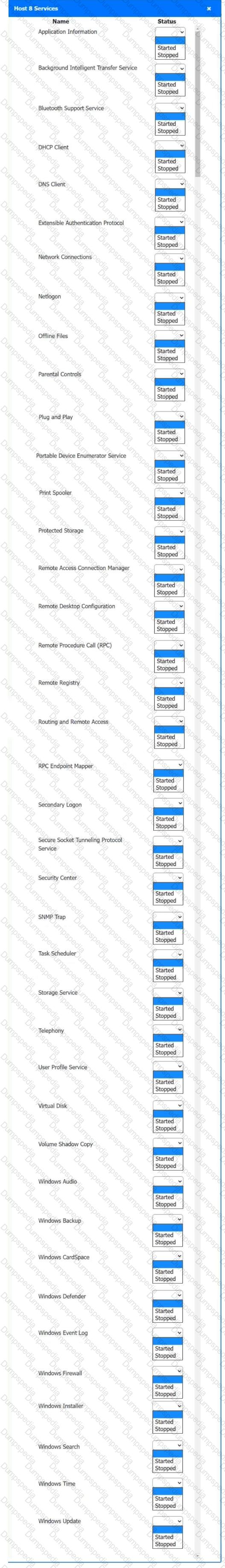
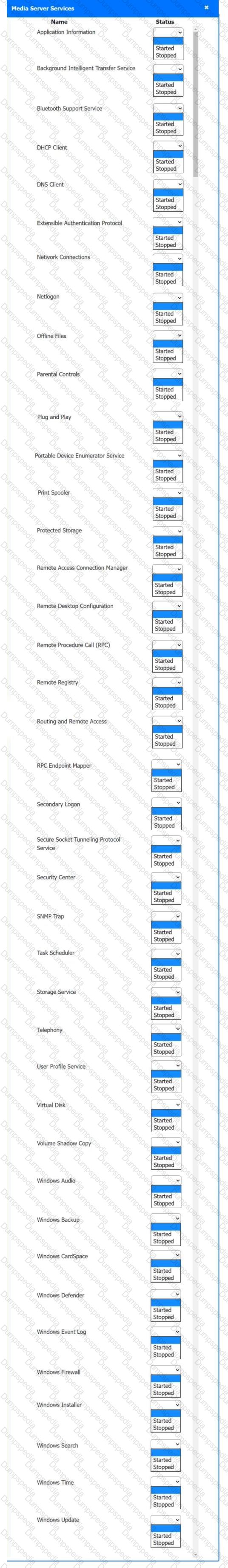
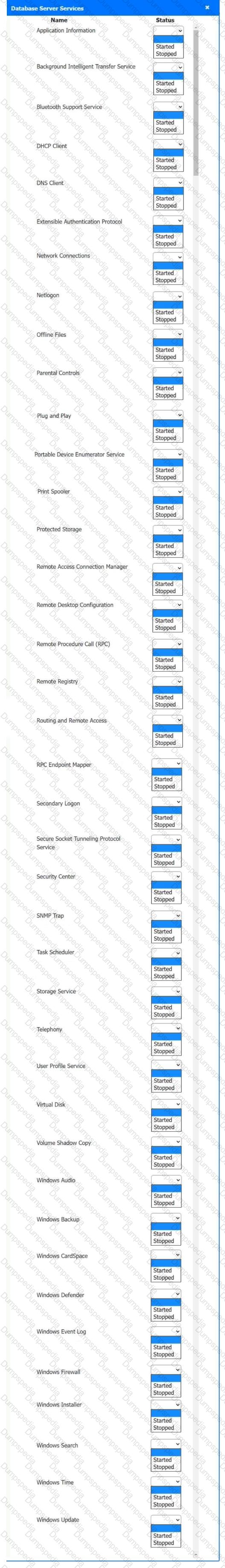
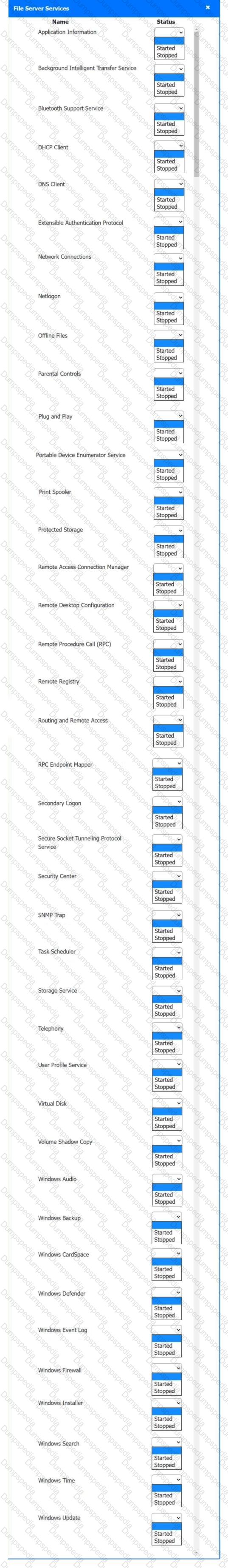
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
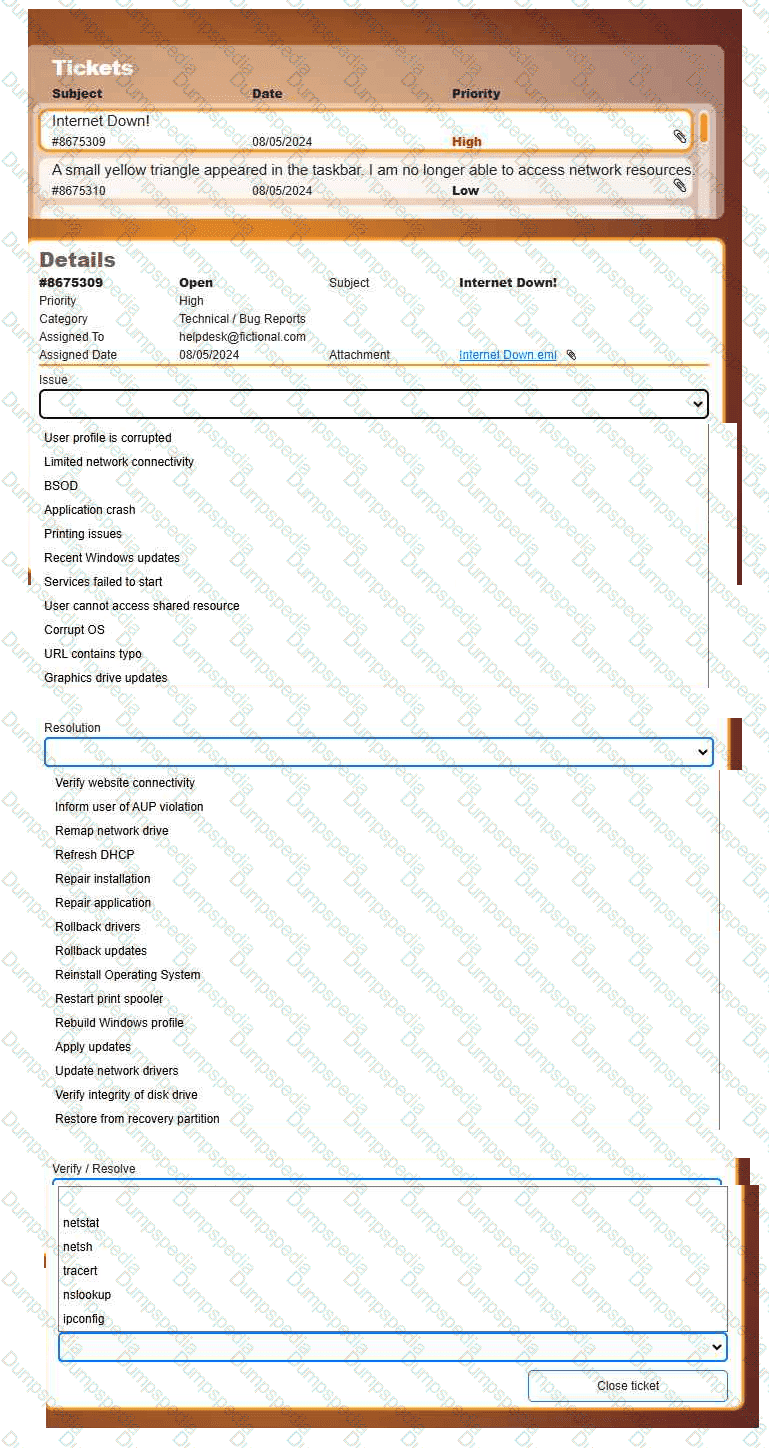
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
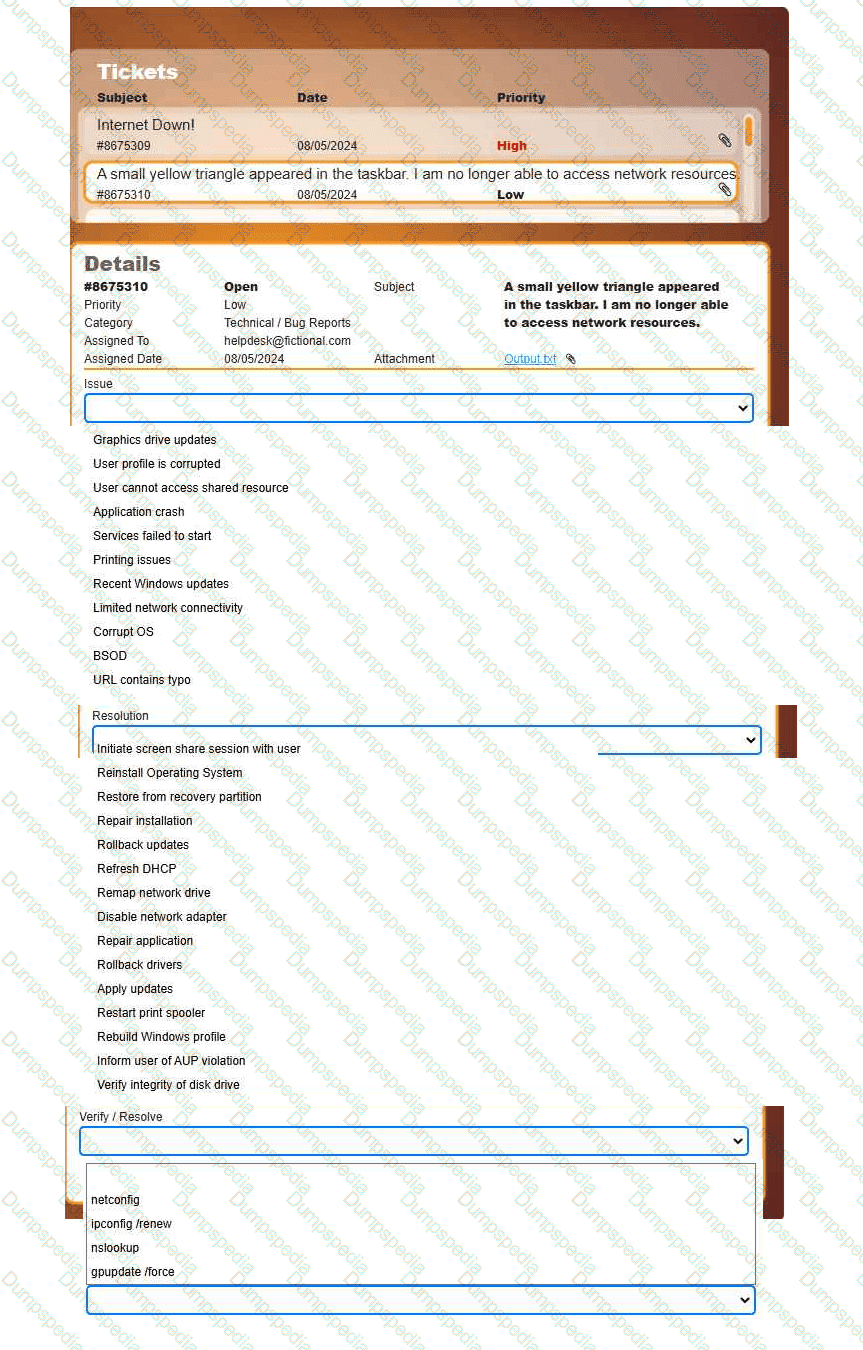
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
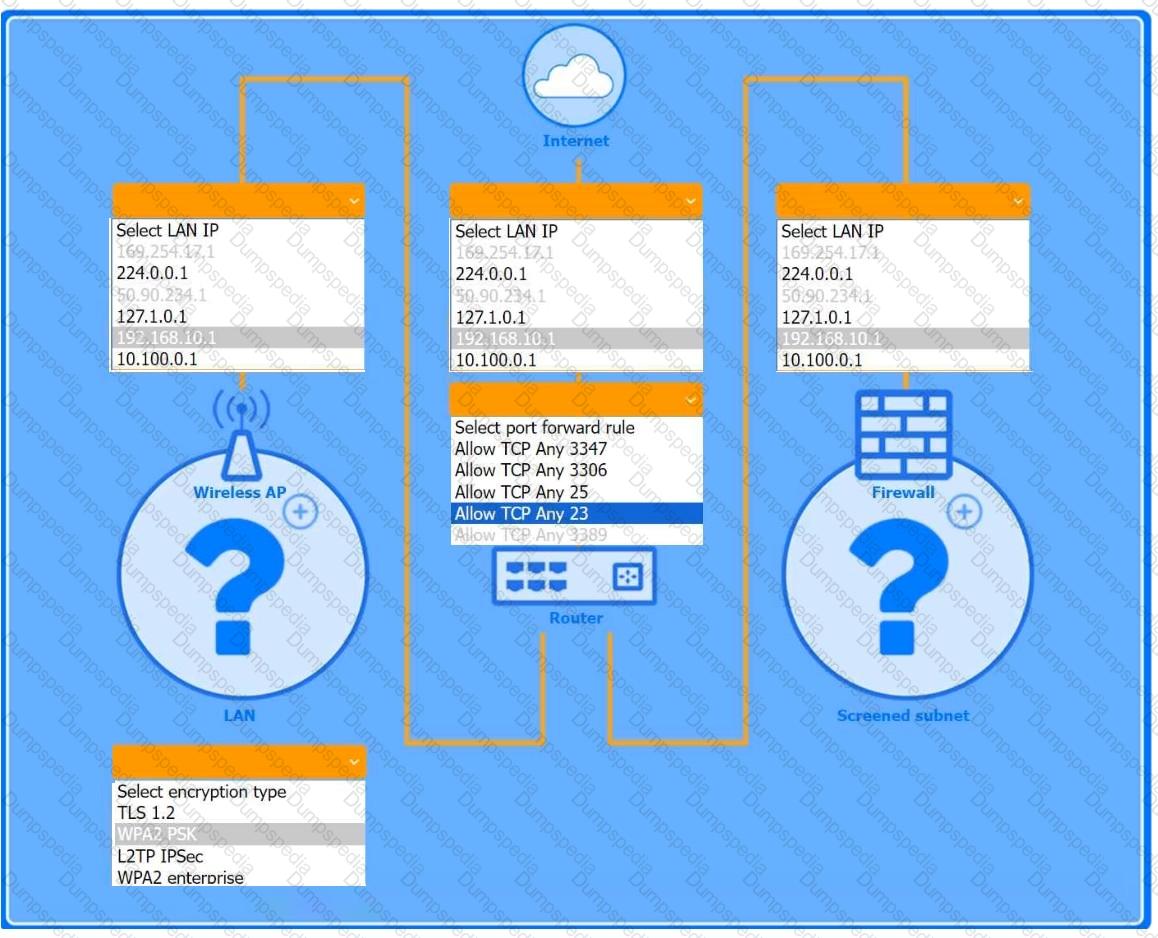
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
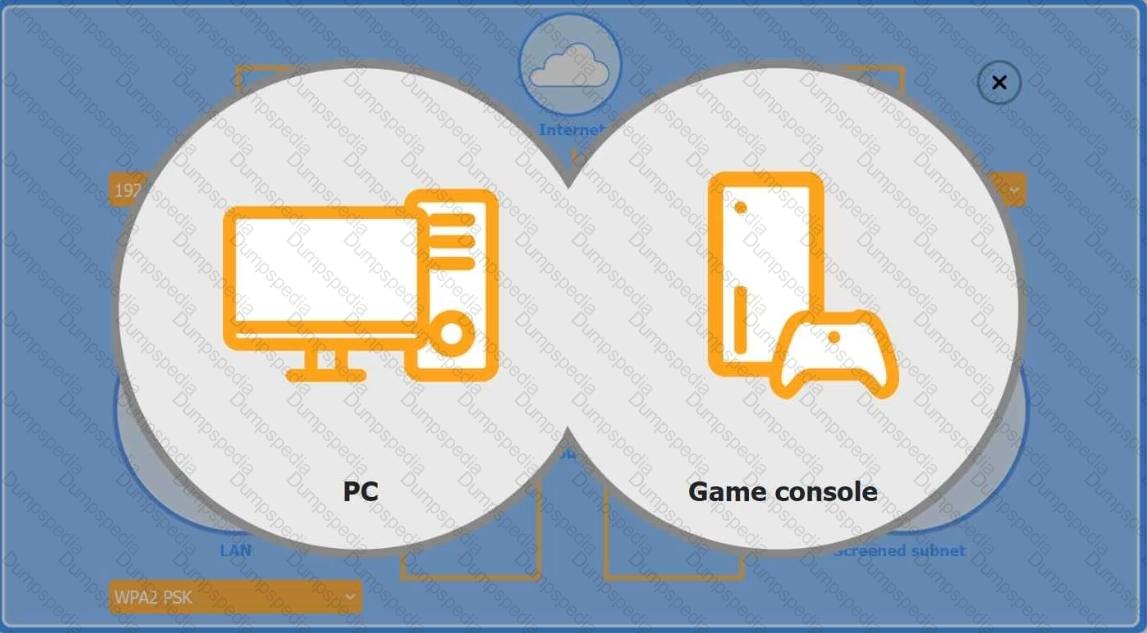
Firewall Screened Subnet
A small company is experiencing unauthorized access attempts to its Windows workstations. The company suspects that some default security settings may be too permissive. Which of the following actions should an IT technician take?