An administrator is setting up a cloud backup solution that requires the following features:
• Cost effective
• Granular recovery
• Multilocation
Which of the following backup types best meets these requirements?
A cloud infrastructure administrator updated the IP tables to block incoming connections and outgoing responses to 104.225.110.203. Which of the following vulnerability management steps is this an example of?
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
A company’s cybersecurity team receives the following alert that a production VM was deleted from the virtual network:
21 September 09:19:08 (GMT-5)
Resource with ID: PROD-WEB001 was deleted by User: Logging Service
The console to manage virtual network resources uses directory authentication. Only users in a particular directory group can interactively access the virtual network management console. The logging service account is not part of this group and requires some local administration privileges to aggregate logs from various resources. The cybersecurity team discovers the logging service account was previously given full directory administrator privileges and sees the following entry:
21 September 09:10:55 (GMT-5)
User with ID: Logging Service was added to the Group: VNet Console Administrators by actor: Logging Service.
The cybersecurity team removes the compromised service account from the directory group. Which of the following should the cybersecurity team do next to prevent repeat instances of this issue?
An organization wants to ensure its data is protected in the event of a natural disaster. To support this effort, the company has rented a colocation space in another part of the
country. Which of the following disaster recovery practices can be used to best protect the data?
A company requests that its cloud administrator provision virtual desktops for every user. Given the following information:
• One hundred users are at the company.
• A maximum of 30 users work at the same time.
• Users cannot be interrupted while working on the desktop.
Which of the following strategies will reduce costs the most?
A cloud engineer is extending on-premises services to a public cloud. The following design requirements must be considered in the overall solution:
" The ability to remotely connect systems from both environments
• No IP address conflicts or overlap
• Cost-effectiveness
Which of the following cloud network concepts best meets these requirements?
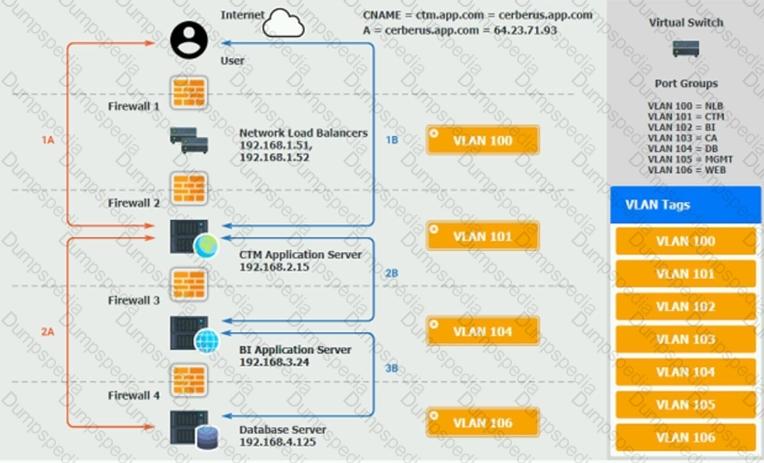
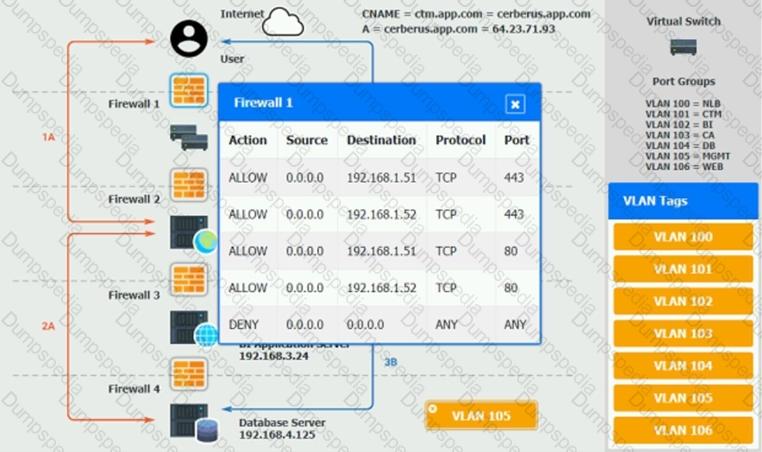
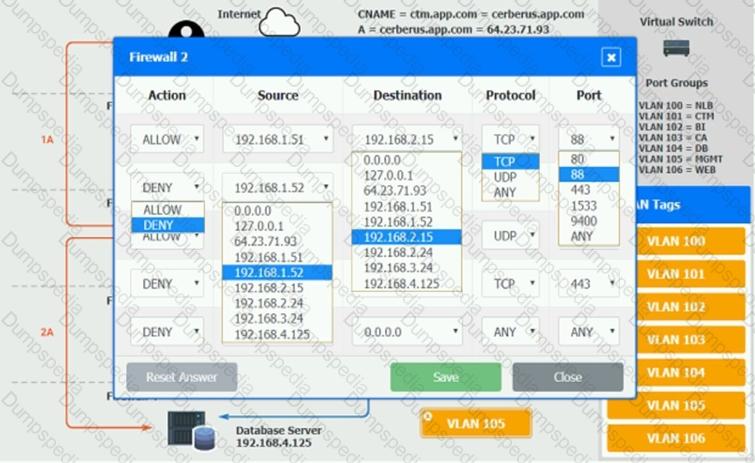
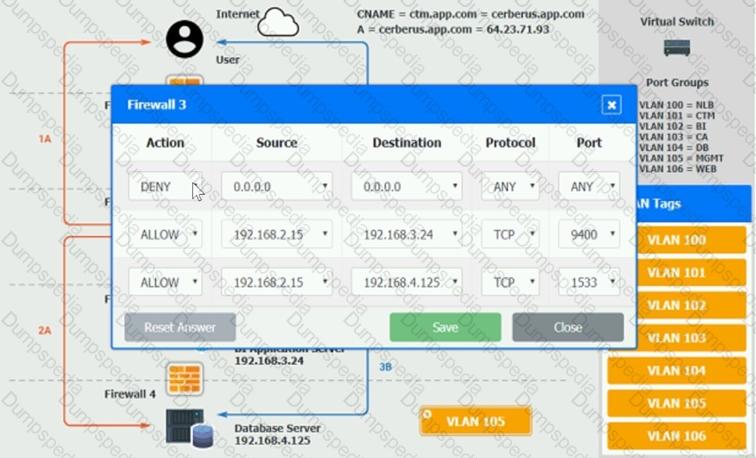
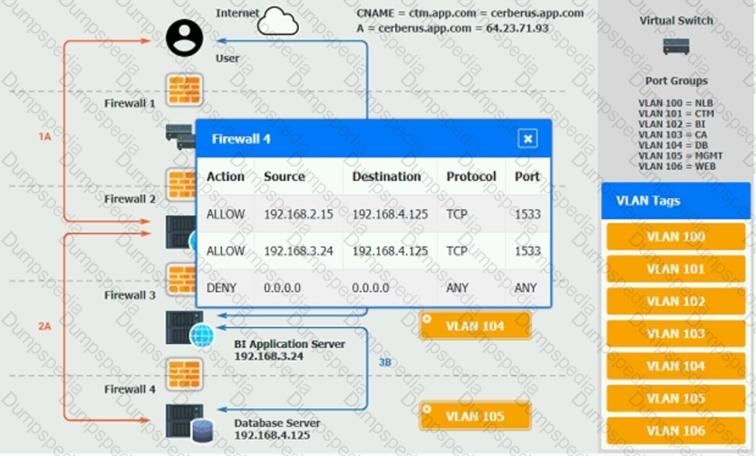
The QA team is testing a newly implemented clinical trial management (CTM) SaaS application that uses a business intelligence application for reporting. The UAT users were instructed to use HTTP and HTTPS.
Refer to the application dataflow:
1A – The end user accesses the application through a web browser to enter and view clinical data.
2A – The CTM application server reads/writes data to/from the database server.
1B – The end user accesses the application through a web browser to run reports on clinical data.
2B – The CTM application server makes a SOAP call on a non-privileged port to the BI application server.
3B – The BI application server gets the data from the database server and presents it to the CTM application server.
When UAT users try to access the application using https://ctm.app.com or http://ctm.app.com, they get a message stating: “Browser cannot display the webpage.” The QA team has raised a ticket to troubleshoot the issue.
INSTRUCTIONS
You are a cloud engineer who is tasked with reviewing the firewall rules as well as virtual network settings.
You should ensure the firewall rules are allowing only the traffic based on the dataflow.
You have already verified the external DNS resolution and NAT are working.
Verify and appropriately configure the VLAN assignments and ACLs. Drag and drop the appropriate VLANs to each tier from the VLAN Tags table. Click on each Firewall to change ACLs as needed.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A group of cloud administrators frequently uses the same deployment template to recreate a cloud-based development environment. The administrators are unable to go back and
review the history of changes they have made to the template. Which of the following cloud resource deployment concepts should the administrator start using?
A write-intensive workload is having frequent performance issues. The workload is running on pay-as-you-go VMs. These VMs use SSDs and have appropriate CPU and RAM sizes. The workload writes millions of small files and has a one-year retention requirement. Which of the following actions should be taken?
An IT manager needs to deploy a cloud solution that meets the following requirements:
. Users must use two authentication methods to access resources.
· Each user must have 10GB of storage space by default.
Which of the following combinations should the manager use to provision these requirements?
A cloud engineer is troubleshooting a connectivity issue. The application server with IP 192.168.1.10 in one subnet is not connecting to the MySQL database server with IP 192.168.2 20 in a different subnet. The cloud engineer reviews the following information:
Application Server Stateful Firewall
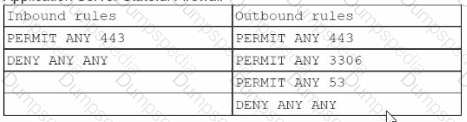
Which of the following should the cloud engineer address lo fix the communication issue?
A network administrator is budding a site-to-site VPN tunnel from the company's headquarters office 10 the company's public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarter office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show VPN traffic is reaching the development network from the office.
Which of the following is the next step the next network administrator should take to troubleshoot the VPN tunnel?
Which of the following compute resources is the most optimal for running a single scripted task on a schedule?
A company's engineering department is conducting a month-long test on the scalability of an in-house-developed software that requires a cluster of 100 or more servers. Which of
the following models is the best to use?
A cloud security analyst is looking for existing security vulnerabilities on software applications. Which of the following describes this vulnerability management phase?
An organization's web application experiences penodic bursts of traffic when a new video is launched. Users are reporting poor performance in the middle of the month. Which of the following scaling approaches should the organization use to scale based on forecasted traffic?
A cloud engineer needs to integrate a new payment processor with an existing e-commerce website. Which of the following technologies is the best fit for this integration?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
A manager wants information about which users signed in to a certain VM during the past month. Which of the following can the cloud administrator use to obtain this information?
Which of the following provides secure, private communication between cloud environments without provisioning additional hardware or appliances?
A web server hosted in a PaaS public cloud platform has been the target of DDoS attacks. A cloud engineer needs to protect the server from future volumetric DDoS attacks. Which of the following are the best actions for the engineer to take? (Select two.)
A cloud engineer needs to determine a scaling approach for a payroll-processing solution that runs on a biweekly basis. Given the complexity of the process, the deployment to each
new VM takes about 25 minutes to get ready. Which of the following would be the best strategy?
Which of the following communication methods between on-premises and cloud environments would ensure minimal-to-low latency and overhead?
A log-parsing application requires significant processing power to ingest the logs streaming from web servers. The engineering team presents the cloud architect with four proposals
using the same underlying hardware. Which of the following should the cloud architect select in order to minimize the impact of an instance failure while keeping the cost as low as
possible?
An organization is concerned that its IT help desk is receiving too many calls about password resets for various internal and external applications. The organization implements a single sign-on (SSO) solution. Which of the following technologies should the cloud architect at the organization recommend implementing?
A cross-site request forgery vulnerability exploited a web application that was hosted in a public laaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again. Which of the following should the security engineer do to make the WAF control effective?
A cloud engineer is running a latency-sensitive workload that must be resilient and highly available across multiple regions. Which of the following concepts best addresses these
requirements?
A cloud solution needs to be replaced without interruptions. The replacement process can be completed in phases, but the cost should be kept as low as possible. Which of the
following is the best strategy to implement?
Which of the following is used to deliver code quickly and efficiently across the development, test, and production environments?
A cloud administrator deploys new VMs in a cluster and discovers they are getting IP addresses in the range of 169.254.0.0/16. Which of the following is the most likely cause?
An administrator needs to adhere to the following requirements when moving a customer's data to the cloud:
• The new service must be geographically dispersed.
• The customer should have local access to data
• Legacy applications should be accessible.
Which of the following cloud deployment models is most suitable?
A company recently set up a CDN for its photography and image-sharing website. Which of the following is the most likely reason for the company's action?
A cloud engineer is collecting web server application logs to troubleshoot intermittent issues. However, the logs are piling up and causing storage issues. Which of the following log
mechanisms should the cloud engineer implement to address this issue?
Which of the following industry standards mentions that credit card data must not be exchanged or stored in cleartext?
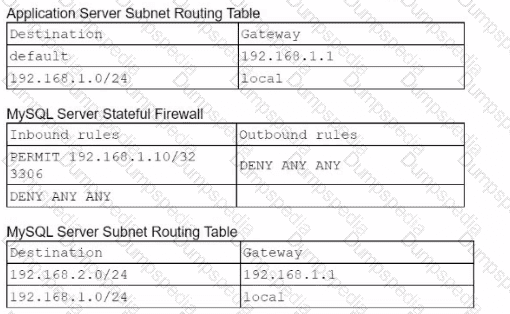
A developer is testing code that will be used to deploy a web farm in a public cloud. The main code block is a function to create a load balancer and a loop to create 1.000 web servers, as shown below:
The developer runs the code against the company's cloud account and observes that the load balancer is successfully created, but only 100 web servers have been created. Which of the following should the developer do to fix this issue?
A cloud solutions architect needs to design a solution that will collect a report and upload it to an object storage service every time a virtual machine is gracefully or non-gracefully
stopped. Which of the following will best satisfy this requirement?
A company has one cloud-based web server that is prone to downtime during maintenance. Which ot the following should the cloud engineer add to ensure high availability?
Which of the following would allow a cloud engineer to flatten a deeply nested JSON log to improve readability for analysts?
A company has developed an online trading platform. The engineering team selected event-based scaling for the platform's underlying resources. The platform resources scale up
with every 2,000 subscribed users. The engineering team finds out that although compute utilization is low, scaling is still occurring. Which of the following statements best explains
why this is the case?
A cloud engineer must find the root cause of a recent performance issue. Logs and metrics have been collected and are available. Which of the following is the best way to determine the source of the issue?
An administrator used a script that worked in the past to create and tag five virtual machines. All of the virtual machines have been created: however, the administrator sees the following results:
{ tags: [ ] }
Which of the following is the most likely reason for this result?
Which of the following is used to detect signals and measure physical properties, such as the temperature of the human body?
Which of the following vulnerability management concepts is best defined as the process of discovering vulnerabilities?
A healthcare organization must follow strict compliance requirements to ensure that Pll is not leaked. The cloud administrator needs to ensure the cloud email system can support this requirement Which of the following should the organization enable?
A cloud engineer must update the company’s code repository, which is running on a VM, to the latest version. The engineer downloads and runs the latest update, which appears to be successful. Which of the following steps should the engineer take next?
A company has been using a CRM application that was developed in-house and is hosted on local servers. Due to internal changes, the company wants to migrate the application to the cloud without having to manage the infrastructure. Which of the following services should the company consider?
A company is developing a new web application that requires a relational database management system with minimal operational overhead. Which of the following should the company choose?
Which of the following reduces the chance of introducing a misconfiguration into cloud deployment templates?
A cloud developer receives a security vulnerability scan report and needs to analyze and record the true positives. Which of the following vulnerability management steps is this an example of?
A newly configured VM fails to run application updates despite having internet access. The updates download automatically from a third-party network. Given the following output:
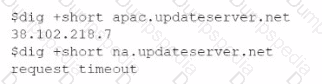
Which of the following troubleshooting steps would be best to take?
A software engineer needs to transfer data over the internet using programmatic access while also being able to query the data. Which of the following will best help the engineer to complete this task?
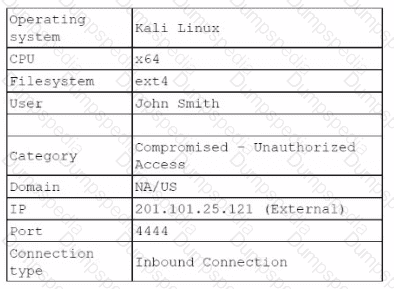
A systems administrator notices a surge of network traffic is coming from the monitoring server. The administrator discovers that large amounts of data are being downloaded to an external source. While investigating, the administrator reviews the following logs:
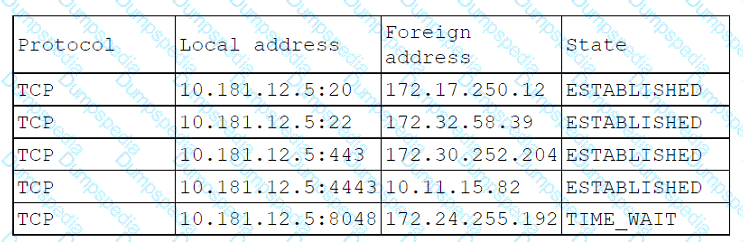
Which of the following ports has been compromised?
Which of the following service options would provide the best availability for critical applications in the event of a disaster?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
A company wants to combine solutions in a central and scalable environment to achieve the following goals:
• Control
• Visibility
• Automation
• Cost efficiency
Which of the following best describes what the company should implement?
A cloud developer is creating a static website that customers will be accessing globally. Which of the following services will help reduce latency?
A cloud engineer wants containers to run the latest version of a container base image to reduce the number of vulnerabilities. The applications in use requite Python 3.10 and ate not compatible with any other version. The containers' images are created every time a new version is released from the source image. Given the container Dockerfile below:

Which of the following actions will achieve the objectives with the least effort?
A cloud engineer is reviewing the following Dockerfile to deploy a Python web application:
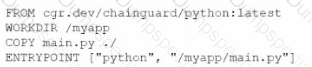
Which of the following changes should the engineer make lo the file to improve container security?
Which of the following network protocols is generally used in a NAS environment?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
Which of the following cloud-native architecture designs is the most easily maintained, decentralized, and decoupled?
Which of the following models will best reduce the cost of running short-term, non-critical workloads?
A company receives files daily from a bank. The company requires that the files must be copied from the cloud storage resource to another cloud storage resource for further
processing. Which of the following methods requires the least amount of effort to achieve the task?
Which of the following integration systems would best reduce unnecessary network traffic by allowing data to travel bidirectionally and facilitating real-time results for developers who need to display critical information within applications?
A cloud developer resigned from an organization and gave a two-week notice. Within the first week since the developer resigned, a security analyst identifies large volumes of file downloads to the developer’s laptop from the source code repository. Which of the following security controls is the best way to mitigate the organization’s risk of data loss?
A security analyst reviews the daily logs and notices the following suspicious activity:
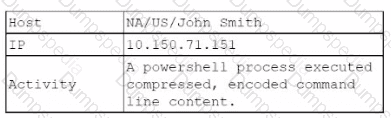
The analyst investigates the firewall logs and identities the following:
Which of the following steps should the security analyst take next to resolve this issue? (Select two).
A video surveillance system records road incidents and stores the videos locally before uploading them to the cloud and deleting them from local storage. Which of the following
best describes the nature of the local storage?
A company wants to optimize cloud resources and lower the overhead caused by managing multiple operating systems. Which of the following compute resources would be best to help to achieve this goal?
A customer relationship management application, which is hosted in a public cloud laaS network, is vulnerable to a remote command execution vulnerability. Which of the following is
the best solution for the security engineer to implement to prevent the application from being exploited by basic attacks?
A cloud engineer wants to deploy a new application to the cloud and is writing the following script:
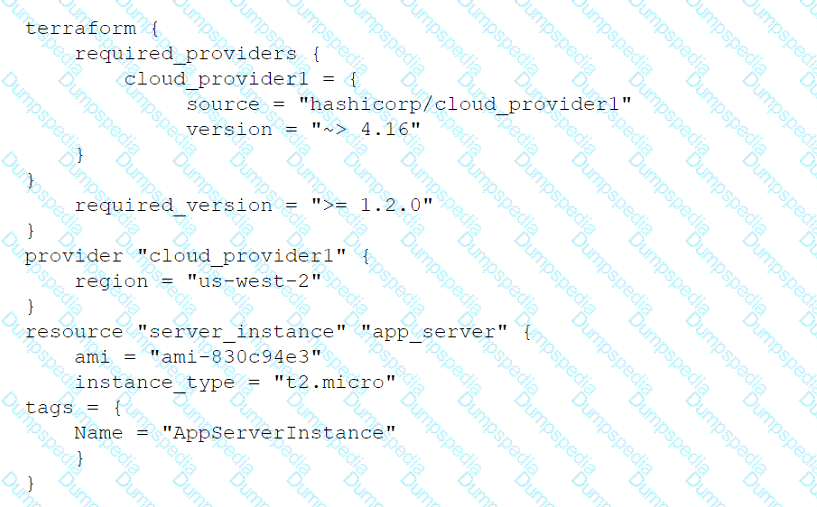
Which of the following actions will this script perform?
A cloud administrator recently created three servers in the cloud. The goal was to create ACLs so the servers could not communicate with each other. The servers were configured
with the following IP addresses:
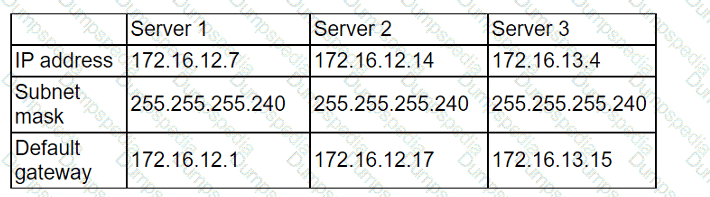
After implementing the ACLs, the administrator confirmed that some servers are still able to reach the other servers. Which of the following should the administrator change to
prevent the servers from being on the same network?