Which of the following types of RAID, if configured with the same number and type of disks, would provide the best write performance?
(Evidence from logs shows multiple ongoing attempts to connect with a default account that was disabled. Which of the following best describes this type of attack?)
Which of the following would a database administrator monitor to gauge server health? (Choose two.)
A database administrator is conducting a stress test and providing feedback to a team that is developing an application that uses the Entity Framework. Which of the following explains the approach the administrator should use when conducting the stress test?
(A company’s database was hacked. A security officer conducted an audit and discovered that an attacker used a rainbow table to break into one of the user accounts to access the database. Which of the following is the best immediate response to this attack?)
Which of the following have data manipulation and procedural scripting power? (Choose two.)
(Analysts are writing complex queries across live tables for a database administrator. Which of the following is the best solution for the analysts to implement in order to improve user performance?)
Which of the following is the deployment phase in which a DBA ensures the most recent patches are applied to the new database?
A developer is designing a table that does not have repeated values. Which of the following indexes should the developer use to prevent duplicate values from being inserted?
Which of the following sets the age requirement for data that should be recovered after a major disaster?
Over the weekend, a company’s transaction database was moved to an upgraded server. All validations performed after the migration indicated that the database was functioning as expected. However, on Monday morning, multiple users reported that the corporate reporting application was not working.
Which of the following are the most likely causes? (Choose two.)
(A healthcare company relies on contact forms and surveys on its website to properly communicate with patients. To which of the following attacks is the company’s data most vulnerable?)
A database administrator is new to a company and wants to create a document that illustrates the interaction between tables. Which of the following should the administrator create?
A server administrator wants to analyze a database server's disk throughput. Which of the following should the administrator measure?
Which of the following services is responsible for assigning, managing, and reclaiming IP addresses on a TCP/IP-based network?
(Which of the following normal forms (NFs) is considered the most preferable for relational database design?)
Which of the following is the correct order of the steps in the database deployment process?
A)
1. Connect
2. Install
3. Configure
4. Confirm prerequisites
5. Validate
6. Test
7. Release
B)
1. Configure
2. Install
3. Connect
4. Test
5. Confirm prerequisites
6. Validate
7. Release
C)
1. Confirm prerequisites
2. Install
3. Configure
4. Connect
5. Test
6. Validate
7. Release
D)
1. Install
2. Configure
3. Confirm prerequisites
4. Connect
5. Test
6. Validate
7. Release
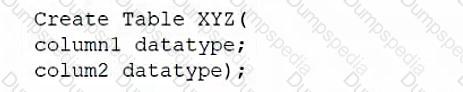
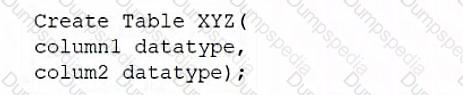
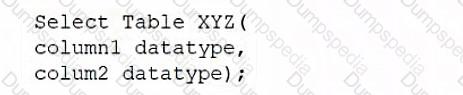
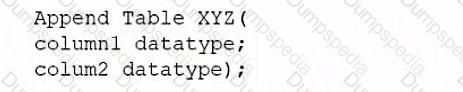
A database administrator would like to create a table named XYZ. Which of the following queries should the database administrator use to create the table?
A)
B)
C)
D)
Which of the following can be used to protect physical database appliances from damage in a server room? (Choose two.)
(Which of the following describes the method in which data is encrypted first with an encryption key and then wrapped by a managed root key?)
(Which of the following best describes the function of a wildcard in the WHERE clause?)
(Before installing a new database instance for an organization, a DBA needs to verify the amount of space, the hardware, and the network resources. Which of the following best describes this process?)
Which of the following are the best resources for monitoring potential server issues? (Choose two.)
(Which of the following is used to store product quantities in a table while ensuring the minimal amount of storage is consumed?)
Which of the following is used to write SQL queries in various programming languages?
An on-premises application server connects to a database in the cloud. Which of the following must be considered to ensure data integrity during transmission?