Which of the following commands should an administrator use to convert a KVM disk file to a different format?
An administrator receives reports that a web service is not responding. The administrator reviews the following outputs:
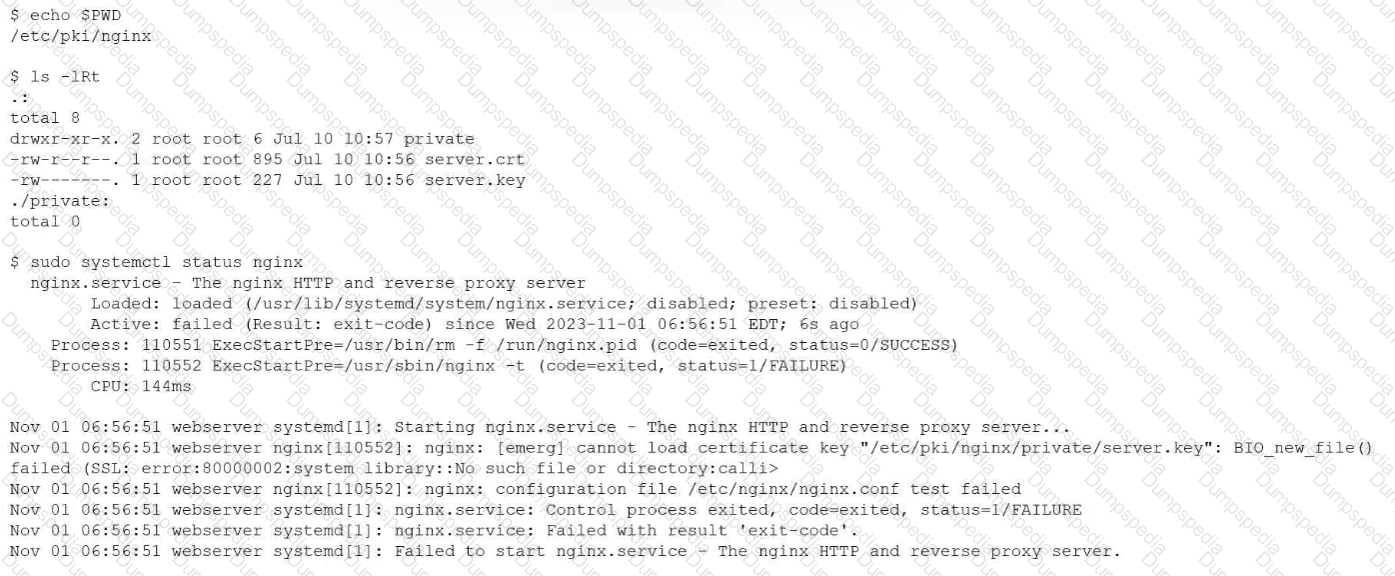
Which of the following is the reason the web service is not responding?
A Linux administrator needs to change the server name to comptia1. Which of the following commands should the administrator use?
An administrator added a new disk to expand the current storage. Which of the following commands should the administrator run first to add the new disk to the LVM?
A user reports Issues v/hen trying to connect to one ot the Linux servers. The server administrator reviews the following outputs:
Output 1:
Kernel panic not syncing: Fatal Machine check
Fid: 0, comm; swapper Tainted: G M ------------------ 4.18.0-553.8.1.cl8_10.x86_64 #1
Call Trace:
< #mc > [rrrrrrrrs:4er..i4i] ? panic+ox7n/oxi43
[] ? mcc_panic+0x21f/0x240
[] ? do_machine_check+0xal8/0xae0
[] ? intel idie+0xbi/0xi70
[] ? machino_check+0xlc/0x30
[] ? intel_idle+0xbl/0xl70
«EOE» [] ? hrtimer 8tart+0xlB/0x20
[] ? cpuidle_idle_cail+0xa7/0xl40
I| ? cpu_idle+0xbfc/0xll0
[] ? Start_secondary+0x202/0x245
Output 2:
[325926.243631] mce: [Error] : CPU 22: Machine Check Exception: 7 Bank 0: bd80000000000134
1325926.247004| nice: (Error): Machine check events logged
[325991.358038] race: [Error] : KIP 10: < ffffffff83584719* (copy user enhanced fast strir.q+0x9/0x20)
[325991.358038] mce: [Error] : tsc 31ea89256a735 ADDR 3cdl889000 MISC 8c
[325991.350033] mce: [Error] : PROCESSOR 0:50657 TIME 15945B1695 SOCKET 0 APTC 16 microcode rrrrtrrr
[325991.358038] mce: [Error] : Run the above through ' rr.ccloq —ascii*
[325991.358038] mce: [Error] : Machine check: Action required: unknown MCACOD
[325991.3511038] Kernel panic not syncing: Fatal machine check
Which of the following statements describes the cause and resolution for this issue?
A systems administrator needs to set the IP address of a new DNS server. Which of the following files should the administrator modify to complete this task?
Application owners are reporting that their application stops responding after several days of running, and they need to restart it. A Linux administrator obtains the following details from the dmesg command:
invoked oom-killer
Call Trace:
out_of_memory
oom_kill_process
The application owners mentioned that resources to the system have been increased, and the error takes longer to appear. Which of the following best describes the reason the process is being terminated by OOM?
An administrator receives a report that a user is unable to execute the runreports utility. The administrator logs in as the user, runs the following commands, and receives the following output:
$ runreports
runreports: command not found
$ ls -l /usr/local/bin
-rwxr-xr-x 1 root root 29 May 10 11:31 runreports
$ echo $PATH
/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/snap/bin
Which of the following best describes the issue and how to resolve it?
A systems administrator receives reports about connection issues to a secure web server. Given the following firewall and web server outputs:
Firewall output:
Status: active
To Action From
443/tcp DENY Anywhere
443/tcp (v6) DENY Anywhere (v6)
Web server output:
tcp LISTEN 0 4096 *:443 :
Which of the following commands best resolves this issue?
A systems administrator needs to restore a backup to the /usr/app/data directory. Which of the following commands should the administrator use for this task?
Which of the following commands should an administrator use to convert a KVM disk file to a different format?
Which of the following Ansible components contains a list of hosts and host groups?
To perform a live migration, which of the following must match on both host servers? (Choose two)
An administrator wants to search a file named myFile and look for all occurrences of strings containing at least five characters, where characters two and five are i, but character three is not b. Which of the following commands should the administrator execute to get the intended result?
The security manager at a company notifies a systems administrator of open vulnerabilities on the Linux system. The administrator receives the following information while logged in to the server:
$ date
Thu Jul 11 16:12:42 UTC 2024
$ getenforce
Enforcing
$ dnf history
ID | Command Line | Date and time | Action(s) | Altered
45 | update -y | 2023-07-09 | Update | 27
46 | install httpd | 2023-01-11 | Install | 9
47 | update -y | 2023-08-08 | Upgrade | 44
Which of the following is the most likely security concern?
Which of the following commands is used to verify whether a port is open on a remote host?
An administrator wants to start an Ubuntu terminal in a container. Which of the following will allow the administrator to complete the task?
Which of the following commands should an administrator use to see a full hardware inventory of a Linux system?
A Linux administrator receives reports that an application hosted in a system is not completing tasks in the allocated time. The administrator connects to the system and obtains the following details:
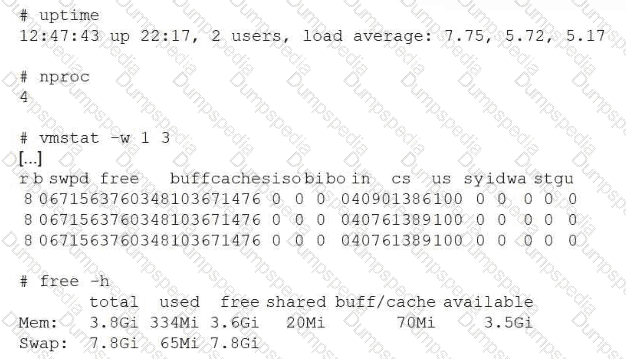
Which of the following actions can the administrator take to help speed up the jobs?
Which of the following Ansible components is used to define groups and individual hosts and can include variables specific to each host or group?
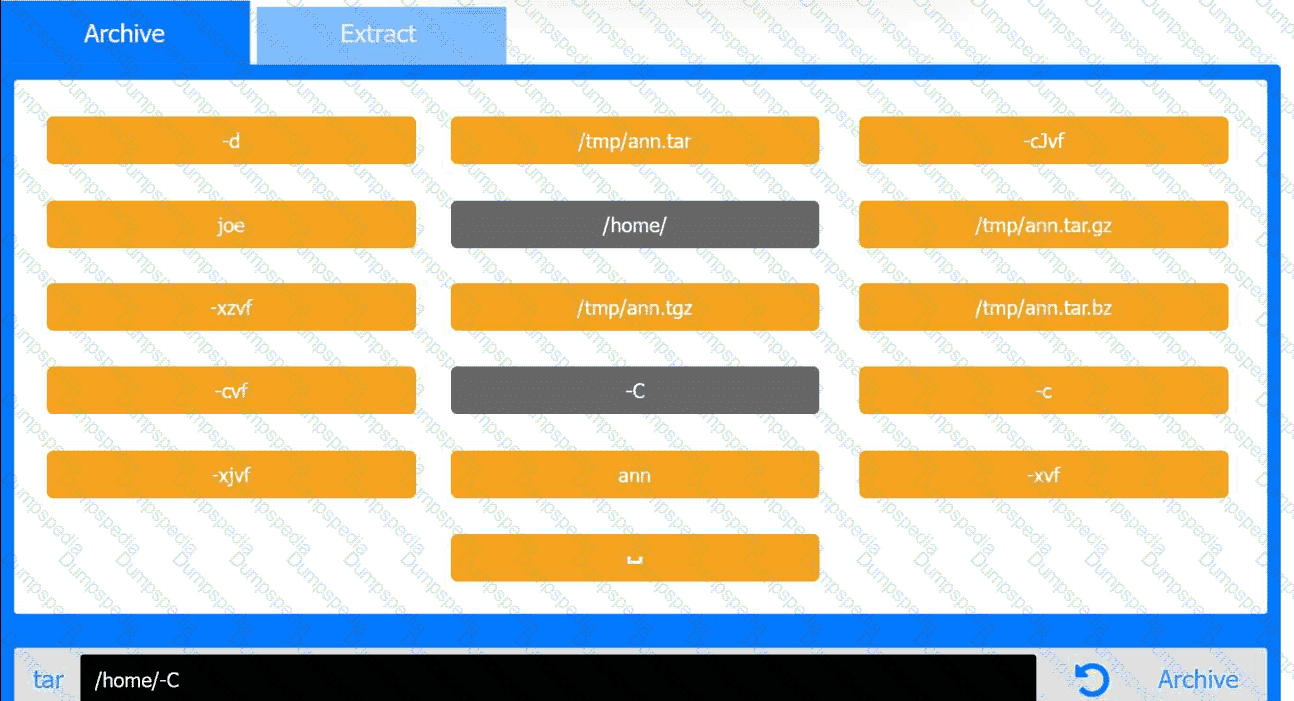
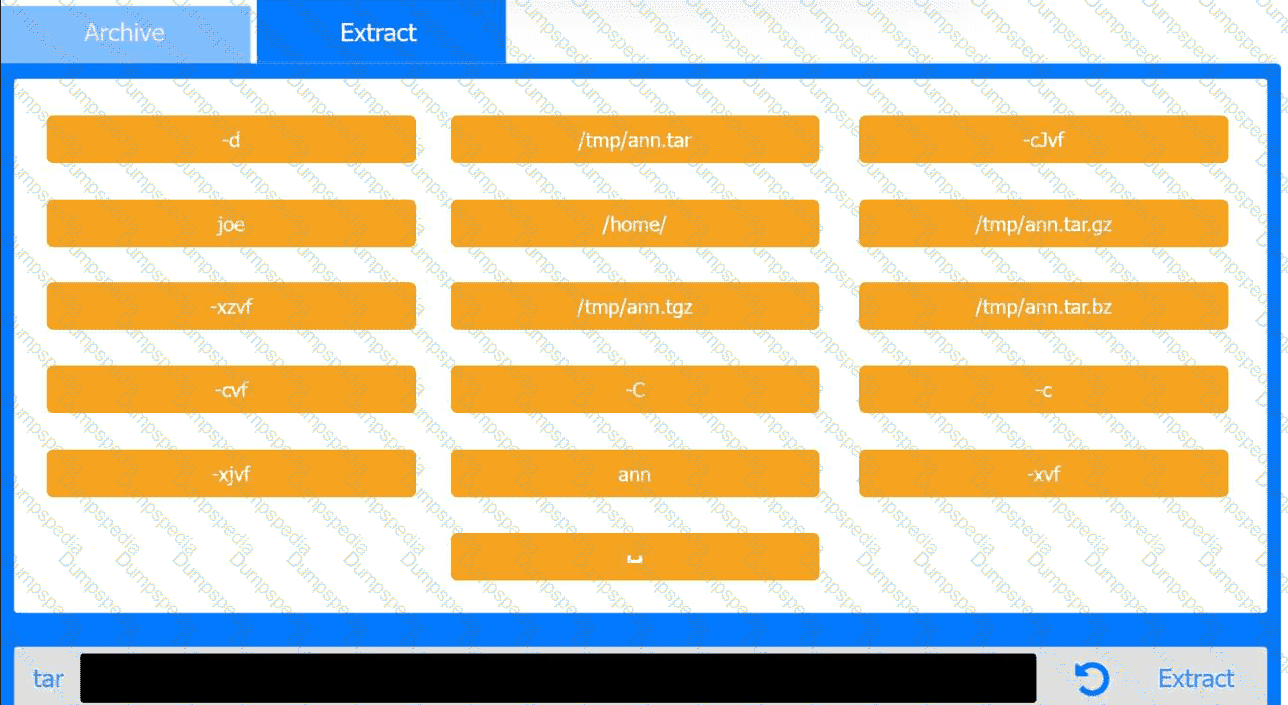
Joe, a user, has taken a position previously held by Ann. As a systems administrator, you
need to archive all the files from Ann ' s home directory and extract them into Joe ' s home
directory.
INSTRUCTIONS
Within each tab, click on an object to form the appropriate commands. Command objects may only be used once, but the spacebar _ object may be used multiple times. Not all objects will be used.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A systems administrator receives reports from users who are having issues while trying to modify newly created files in a shared directory. The administrator sees the following outputs:
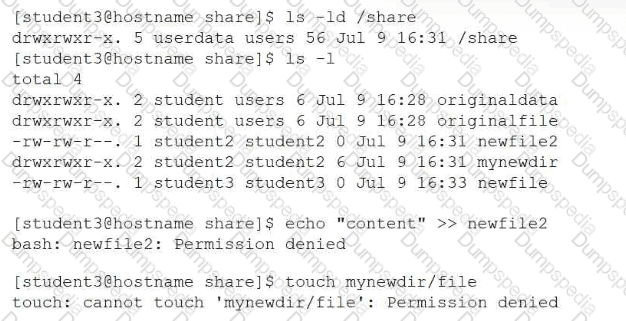
Which of the following provides the best resolution to this issue?
An administrator needs to remove the directory /home/user1/data and all of its contents. Which of the following commands should the administrator use?
A Linux administrator installed a new program inside $HOME/.local/bin and is trying to execute it without using an absolute path. Which of the following should the administrator use for this task?
A technician wants to temporarily use a Linux virtual machine as a router for the network segment 10.10.204.0/24. Which of the following commands should the technician issue? (Select three).
A Linux administrator observes low network throughput. The administrator gathers the following output:
$ ip link show eth0
eth0: < BROADCAST,MULTICAST,UP,RUNNING > mtu 9000 ...
$ ping -s 1472 -M do 192.168.10.2
PING 192.168.10.2(192.168.10.2) 1472(1500) bytes of data.
From 10.10.9.72 icmp_seq=1 frag needed and DF set
Which of the following is the cause of the low network throughput?
Which of the following commands can be used to display real-time running processes on a Linux system?
A Linux administrator receives reports about MySQL service availability issues. The administrator observes the following information:
uptime -p shows the system has been up for only 2 minutes
journalctl shows messages indicating:
mysqld invoked oom-killer
mysqld cpuset=/ mems_allowed=0
Which of the following explains why the server was offline?
A systems administrator is creating a backup copy of the /home/ directory. Which of the following commands allows the administrator to archive and compress the directory at the same time?
An administrator must secure an account for a user who is going on extended leave. Which of the following steps should the administrator take? (Choose two)
Following the completion of monthly server patching, a Linux administrator receives reports that a critical application is not functioning. Which of the following commands should help the administrator determine which packages were installed?
Which of the following is the first step when starting a new Python project on a Linux system?
Which of the following describes how a user ' s public key is used during SSH authentication?
Which of the following describes what Ansible is used for in the context of IT infrastructure?
A systems administrator is working on configuration changes and needs to replace a hostname in a specific file. Which of the following commands should the administrator use to complete this task?
A Linux administrator wants to make the enable_auth variable set to 1 and available to the environment of subsequently executed commands. Which of the following should the administrator use for this task?
Which of the following commands should a Linux administrator use to determine the version of a kernel module?
A Linux administrator is making changes to local files that are part of a Git repository. The administrator needs to retrieve changes from the remote Git repository. Which of the following commands should the administrator use to save the local modifications for later review?