Which of the following is the part of a disaster recovery (DR) plan that identifies the critical systems that should be recovered first after an incident?
Which of the following is the step that a troubleshooter should take immediately after implementing a solution?
Which of the following is the correct order of components in a bottom-up approach for the three-tier hierarchical model?
Which of the following is the next step to take after successfully testing a root cause theory?
A customer recently moved into a new office and notices that some wall plates are not working and are not properly labeled Which of the following tools would be best to identify the proper wiring in the IDF?
A network technician is troubleshooting a connectivity issue on a server. Which of the following commands is the most effective for checking whether the server is receiving network traffic?
Which of the following best describes the purpose of a UPS and PDU in a network installation?
Which of the following facilities is the best example of a warm site in the event of information system disruption?
Which of the following kinds of targeted attacks uses multiple computers or bots to request the same resource repeatedly?
Which of the following protocols uses the Dijkstra ' s Link State Algorithm to establish routes inside its routing table?
A network administrator must implement a feature that supports redundancy and scaling on the switches at the distribution layer of the network. Which of the following is the best option?
A VoIP phone is plugged in to a port but cannot receive calls. Which of the following needs to be done on the port to address the issue?
Which of the following could provide a lightweight and private connection to a remote box?
Which of the following VPN types provides secure remote access to the network resources through a web portal?
A network administrator deploys new network hardware. While configuring the network monitoring server, the server could authenticate but could not determine the specific status of the hardware. Which of the following would the administrator most likely do to resolve the issue?
Which of the following is created to illustrate the effectiveness of wireless networking coverage in a building?
Which of the following connector types would most likely be used to connect to an external antenna?
A network engineer queries a hostname using dig, and a valid IP address is returned. However, when the engineer queries that same IP address using dig, no hostname is returned. Which of the following DNS records is missing?
Users report latency with a SaaS application. Which of the following should a technician adjust to fix the issue?
A company reports that their facsimile machine no longer has a dial tone when trying to send a fax. The phone cable is damaged on one end. Which of the following types of connectors should a technician replace?
Which of the following is most likely responsible for the security and handling of personal data in Europe?
A network engineer configures an application server so that it automatically adjusts resource allocation as demand changes. This server will host a new application and demand is not predictable. Which of the following concepts does this scenario demonstrate?
Which of the following is the most closely associated with segmenting compute resources within a single cloud account?
While deploying a new fleet of computers on a DHCP network, a network administrator notices that new computers cannot connect to the internet. Which of the following is most likely the problem?
A user recently moved a workstation to a different part of the office. The user is able to access the internet and print but is unable to access server resources. Which of the following is the most likely cause of the issue?
An IT department asks a newly hired employee to use a personal laptop until the company can provide one. Which of the following policies is most applicable to this situation?
A network administrator needs to deploy a subnet using an IP address range that can support at least 260 devices with the fewest wasted addresses. Which of the following subnets should the administrator use?
A network administrator is deploying a new switch and wants to make sure that the default priority value was set for a spanning tree. Which of the following values would the network administrator expect to see?
Which of the following protocols has a default administrative distance value of 90?
Which of the following is the greatest advantage of maintaining a cold DR site compared to other DR sites?
Which of the following internal routing protocols is best characterized as having fast convergence and being loop-free?
Which of the following must be implemented to securely connect a company ' s headquarters with a branch location?
A user reports having intermittent connectivity issues to the company network. The network configuration for the user reveals the following:
IP address: 192.168.1.10
Subnet mask: 255.255.255.0
Default gateway: 192.168.1.254
The network switch shows the following ARP table:
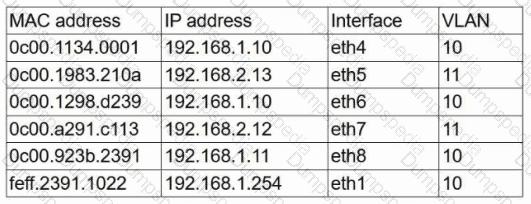
Which of the following is the most likely cause of the user ' s connection issues?
Which of the following cable types allows the use of QSFP ports without requiring transceivers?
Which of the following connectors allows a singular QSFP transceiver to have several physical connections?
After extremely high temperatures cause a power outage, the servers automatically shut down, even though the UPSs for the servers still have hours of battery life. Which of the following should a technician recommend?
A network administrator installs wireless access points (APs) inside an industrial warehouse. A wireless survey shows a large amount of electromagnetic interference. Which of the following cable types should the administrator use to connect the APs to the switch?
A network administrator is planning to implement device monitoring to enhance network visibility. The security that the solution provides authentication and encryption. Which of the following meets these requirements?
Which of the following layers of the OSI model is responsible for end-to-end encryption?
After running a Cat 8 cable using passthrough plugs, an electrician notices that connected cables are experiencing a lot of cross talk. Which of the following troubleshooting steps should the electrician take first?
A network engineer connects a business to a new ISP. A simple ping test to 8.8.8.8 is successful. However, users complain of extreme slowness to any website and periods of no connectivity. Which of the following is the most likely cause?
A technician is implementing a new SD-WAN device with a default configuration. The technician receives a URL via email and connects the new device to the internet to complete the installation. Which of the following is this an example of?
Which of the following allows a user to connect to an isolated device on a stand-alone network?
Which of the following steps of the troubleshooting methodology would most likely involve comparing current throughput tests to a baseline?
A network administrator receives a ticket from a user. The user reports that they cannot access any websites and that they have already checked everything on their computer. Which of the following is the first action the administrator should take?
A network engineer discovers network traffic that is sending confidential information to an unauthorized and unknown destination. Which of the following best describes the cause of this network traffic?
Several users in an organization report connectivity issues and lag during a video meeting. The network administrator performs a tcpdump and observes increased retransmissions for other non-video applications on the network. Which of the following symptoms describes the users ' reported issues?
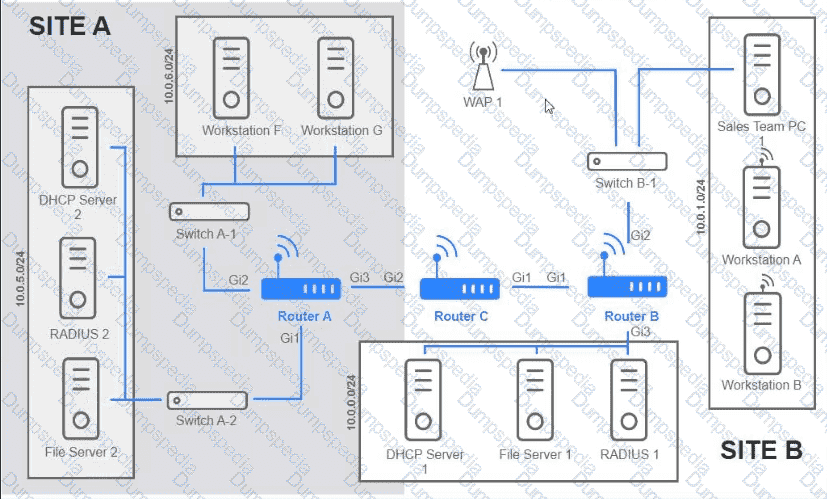
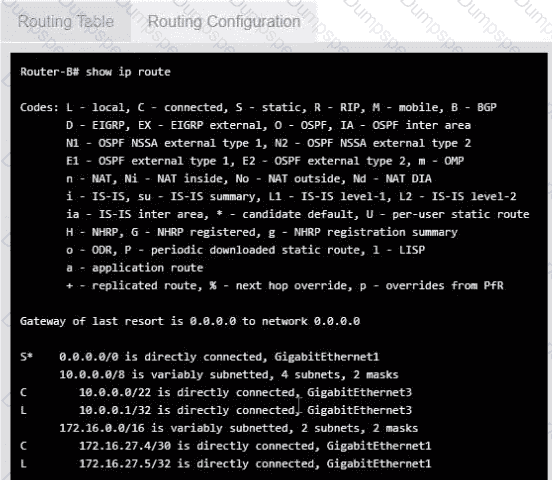
Users are unable to access files on their department share located on flle_server 2. The network administrator has been tasked with validating routing between networks hosting workstation A and file server 2.
INSTRUCTIONS
Click on each router to review output, identity any Issues, and configure the appropriate solution
If at any time you would like to bring back the initial state of trie simulation, please click the reset All button;
A company is expanding to another floor in the same building. The network engineer configures a new switch with the same VLANs as the existing stack. When the network engineer connects the new switch to the existing stack, all users lose connectivity. Which of the following is the MOST likely reason?
A network manager connects two switches together and uses two connecting links. Which of the following configurations will prevent Layer 2 loops?
A network engineer is installing new PoE wireless APs. The first five APs deploy successfully, but the sixth one fails to start. Which of the following should the engineer investigate first?
Which of the following involves an attacker traversing from one part of a network to another part that should be inaccessible?
A network administrator prepares a VLAN for a new office while planning for minimal IP address waste. The new office will have approximately 800 workstations. Which of the following network schemes meets the requirements?
A critical infrastructure switch is identified as end-of-support. Which of the following is the best next step to ensure security?
Which of the following standards enables the use of an enterprise authentication for network access control?
While troubleshooting a VoIP handset connection, a technician ' s laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
A network engineer is configuring network ports in a public office. To increase security, the engineer wants the ports to allow network connections only after authentication. Which of the following security features should the engineer use?
Which of the following steps in the troubleshooting methodology comes after using a top-to-top buttom examination of the OSI model to determine cause?
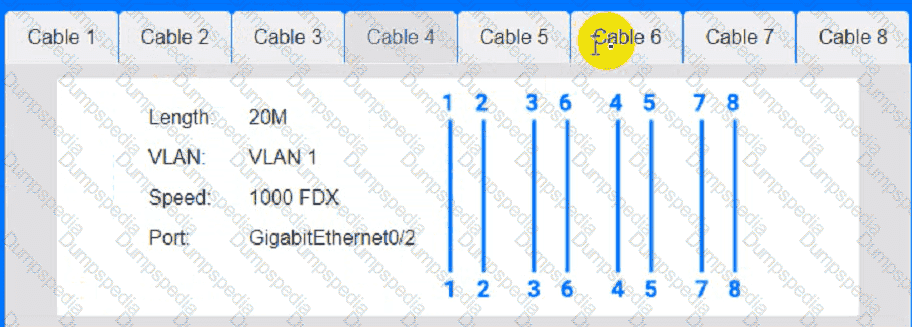
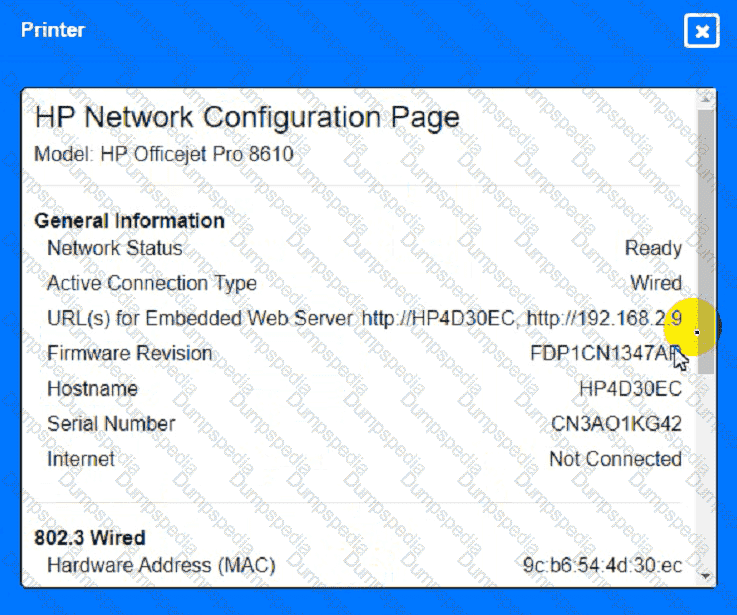
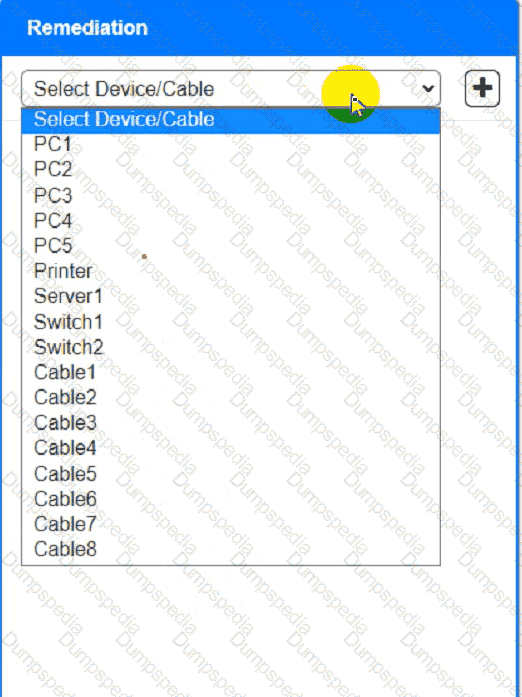
A network technician needs to resolve some issues with a customer ' s SOHO network.
The customer reports that some of the devices are not connecting to the network, while others appear to work as intended.
INSTRUCTIONS
Troubleshoot all the network components and review the cable test results by Clicking on each device and cable.
Diagnose the appropriate component(s) by identifying any components with a problem and recommend a solution to correct each problem.
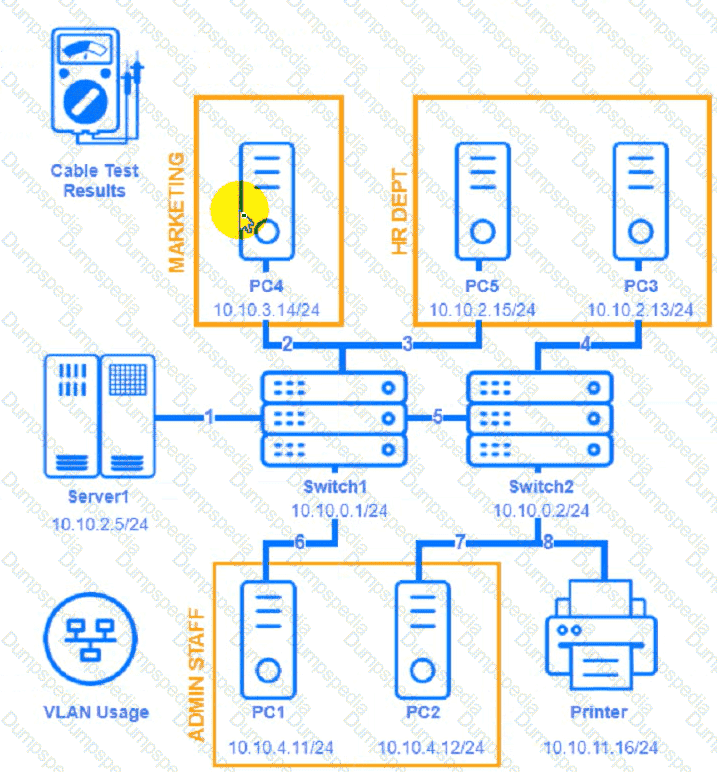

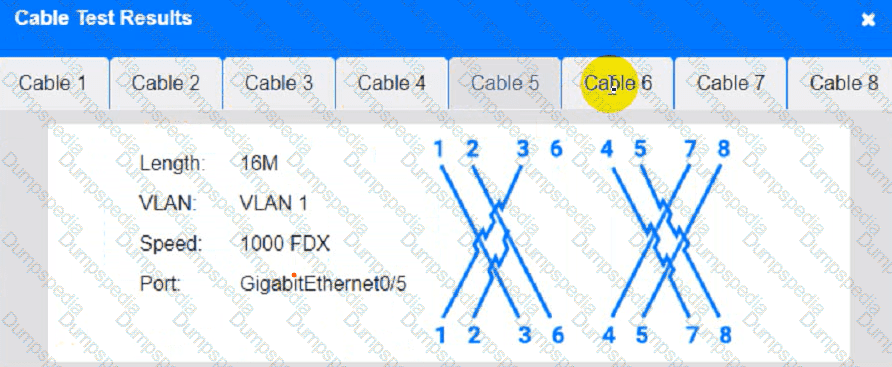
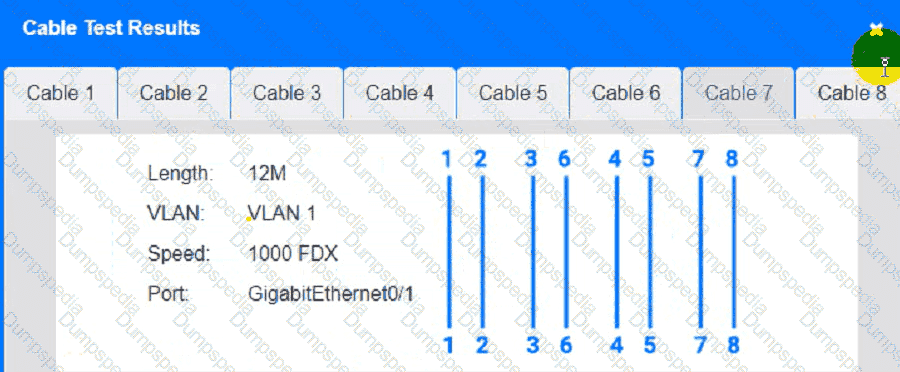
Cable Test Results:
Cable 1:
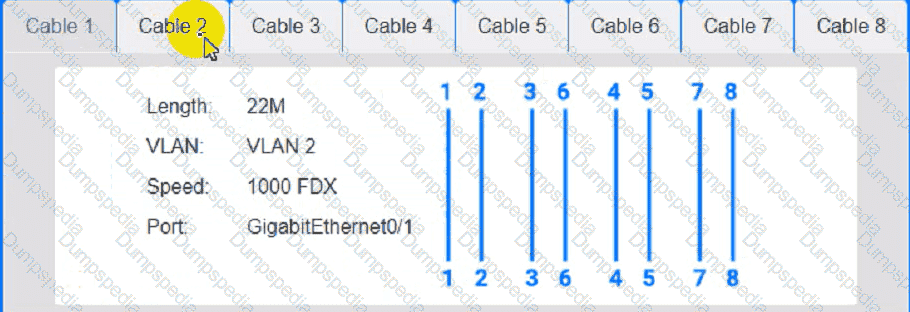
Cable 2:
Cable 3:
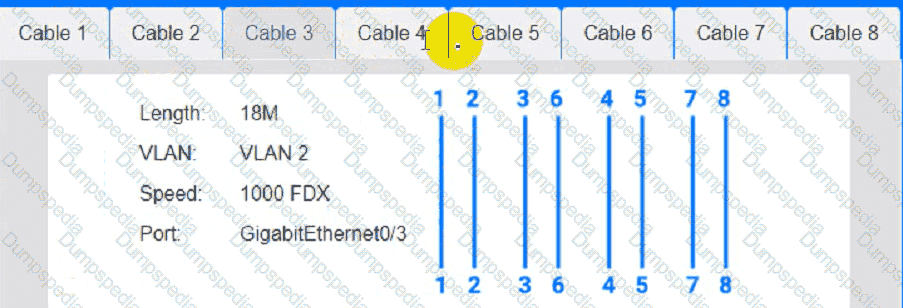
Cable 4:
A data center interconnect using a VXLAN was recently implemented. A network engineer observes slow performance and fragmentation on the interconnect. Which of the following technologies will resolve the issue?
Users at an organization report that the wireless network is not working in some areas of the building. Users report that other wireless network SSIDs are visible when searching for the network, but the organization ' s network is not displayed. Which of the following is the most likely cause?
Which of the following can be implemented to add an additional layer of security between a corporate network and network management interfaces?
Which of the following best describes the amount of time between a disruptive event and the point that affected resources need to be back to fully functional status?
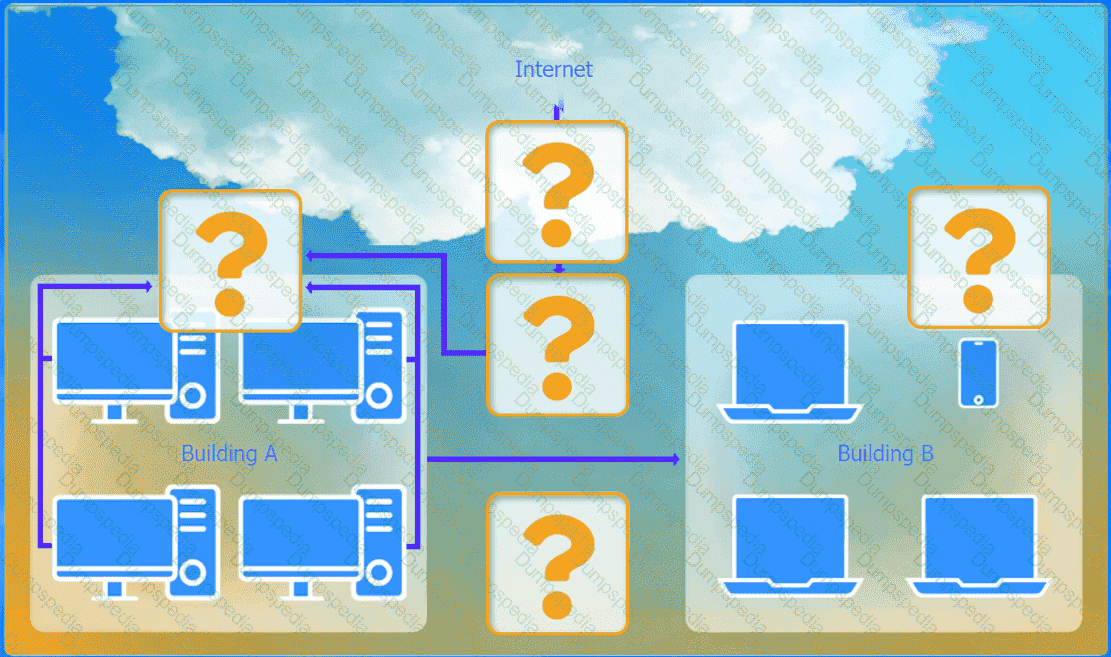
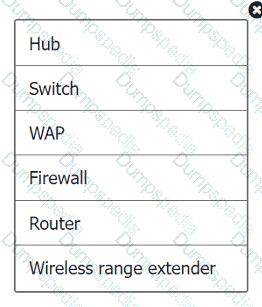
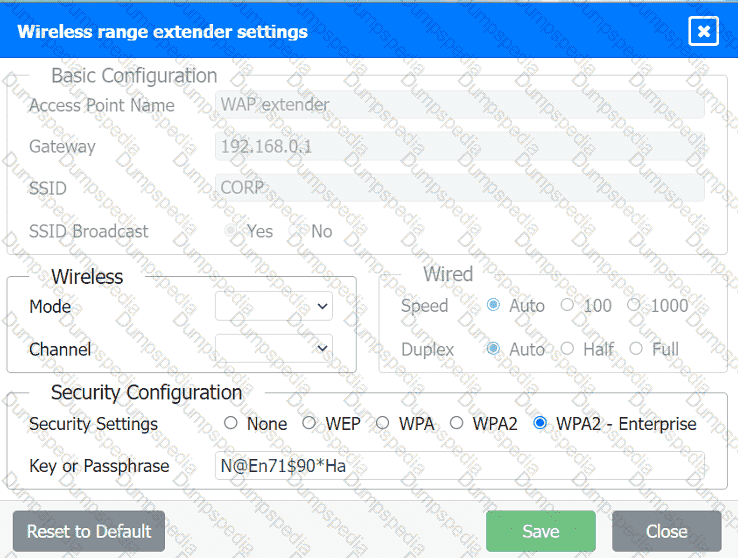
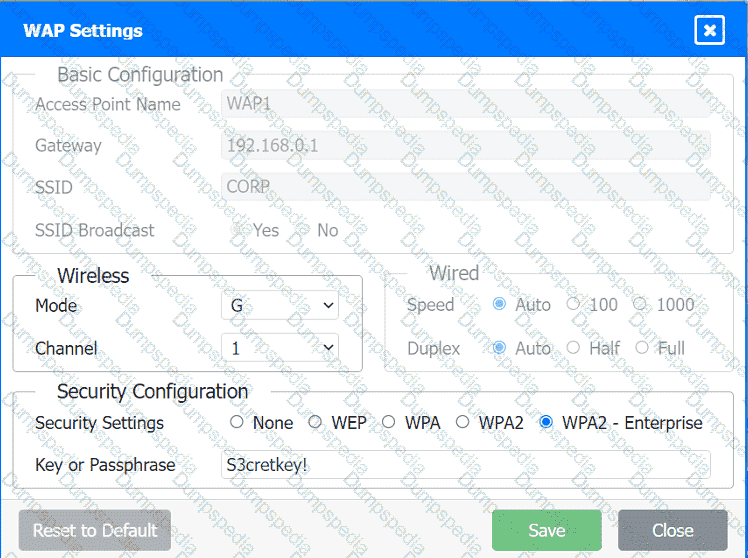
A network administrator has been tasked with configuring a network for a new corporate office. The office consists of two buildings, separated by 50 feet with no physical connectivity. The configuration must meet the following requirements:
. Devices in both buildings should be
able to access the Internet.
. Security insists that all Internet traffic
be inspected before entering the
network.
. Desktops should not see traffic
destined for other devices.
INSTRUCTIONS
Select the appropriate network device for each location. If applicable, click on the magnifying glass next to any device which may require configuration updates and make any necessary changes.
Not all devices will be used, but all locations should be filled.
If at any time you would like to bring back the initial state of the simulation, please
click the Reset All button.
A network administrator configured a router interface as 10.0.0.95 255.255.255.240. The administrator discovers that the router is not routing packets to a web server with IP 10.0.0.81/28. Which of the following is the best explanation?
Which of the following is used to describe the average duration of an outage for a specific service?
An organization recently connected a new computer to the LAN. The user is unable to ping the default gateway. The technician examines the configuration and sees a self-assigned IP address. Which of the following is the most likely cause?
A technician needs to quickly set up a network with five wireless devices. Which of the following network types should the technician configure to accomplish this task?
A network technician installs a new 19.7ft (6m), Cat 6, UTP cable for the connection between a server and a switch. Communication to the server is degraded, and the NIC statistics show dropped packets and CRC errors. Which of the following cables would the technician most likely use instead to reduce the errors?
A newtwork administrator needs to create an SVI on a Layer 3-capable device to separate voice and data traffic. Which of the following best explains this use case?
Which of the following allows a standard user to log in to multiple resources with one account?
Which of the following connector types is most commonly associated with Wi-Fi antennas?
A network architect of a stock exchange broker is implementing a disaster recovery (DR), high-availability plan. Which of the following approaches would be the best fit?
Which of the following is the best networking appliance for interconnecting multiple logical networks and forwarding data packets between them while minimizing latency?
Which of the following requires network devices to be managed using a different set of IP addresses?
Which of the following VPN configurations forces a remote user to access internet resources through the corporate network?
A network administrator wants to update a geofencing policy to limit remote access to the corporate network based on country location. Which of the following would the administrator most likely leverage?
After installing a new 6E wireless router in a small office, a technician notices that some wireless devices are not able to achieve the rated speeds.
Which of the following should the technician check to troubleshoot the issue? (Select two)
A network technician sets up a computer on the accounting department floor for a user from the marketing department. The user reports that they cannot access the marketing department’s shared drives but can access the internet. Which of the following is the most likely cause of this issue?
Which of the following network ports is used when a client accesses an SFTP server?
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses, one for a computer and one for a phone connected to the network. Which of the following classful IPv4 address ranges will be best-suited for the network?
A network technician is terminating a cable to a fiber patch panel in the MDF. Which of the following connector types is most likely in use?
A Chief Executive Officer (CEO) of a company purchases a new phone that will be used while traveling to different countries. The CEO needs to be able to place outgoing calls and receive incoming calls on the phone using a SIM card. Which of the following cellular technologies does the CEO ' s phone need?
A company implements a video streaming solution that will play on all computers that have joined a particular group, but router ACLs are blocking the traffic. Which of the following is the most appropriate IP address that will be allowed in the ACL?
A network engineer needs to prioritize traffic over a link with the goal of more effectively utilizing the connection. Which of the following should the engineer implement?
Which of the following ports is used to transfer data between mail exchange servers?
A network administrator is setting up a firewall to protect the organization’s network from external threats. Which of the following should the administrator consider first when configuring the firewall?
A network engineer needs to add a boundary network to isolate and separate the internal network from the public-facing internet. Which of the following security defense solutions would best accomplish this task?
A network administrator is extending a network beyond the primary equipment location. Which of the following is where the administrator should install additional network switches?
A user connects to a corporate VPN via a web browser and is able to use TLS to access the internal financial system to input a time card. Which of the following best describes how the VPN is being used?
An ISP provided a company with a pre-configured modem and five public static IP addresses. Which of the following does the company ' s firewall require to access the internet? (Select TWO).
A network engineer is designing an internal network that needs to support both IPv4 and IPv6 routing. Which of the following routing protocols is capable of supporting both IPv4 and IPv6?
A laptop user gets an error when trying to access the company’s intranet site. A technician runs ipconfig /all with the following results:
Autoconfiguration IPv4 Address: 169.254.0.5 (Preferred)
Subnet Mask: 255.255.0.0
Default Gateway:
DHCP Server:
Which of the following is most likely causing the issue?
A company ' s marketing team created a new application and would like to create a DNS record for newapplication.comptia.org that always resolves to the same address as www.comptia.org. Which of the following records should the administrator use?
A user reports issues accessing a file server on a LAN with the IP address 192.168.50.140 at a large facility with incomplete infrastructure documentation. The following are the results of the ping command:
ping -c 10 192.168.50.140
Packets: Sent = 10, Received = 5, Lost = 5 (50% loss)
Round-trip times: Minimum = 3ms, Maximum = 144ms, Average = 42ms
Which of the following should a technician do next to continue troubleshooting the issue at the switch with minimal impact?
A wireless technician wants to implement a technology that will allow user devices to automatically navigate to the best available frequency standard. Which of the following technologies should the technician use?
Which of the following best describes a group of devices that is used to lure unsuspecting attackers and to study the attackers ' activities?
Which of the following network access methods is used to securely access resources, such as a corporate cloud or network, as if they were directly connected?
A network administrator is connecting two Layer 2 switches in a network. These switches must transfer data in multiple networks. Which of the following would fulfill this requirement?
A user tries to visit www.abc.com, but the website that displays is www.cba.com. Which of the following should be done in order to reach the correct website?
A network administrator needs to ensure all network ports use a security method that only permits authenticated devices. The solution must meet the following requirements:
• Reduced chance of spoofing
• Centrally managed solution
• Auditable logs
Which of the following technologies provides this functionality?
Which of the following steps of the troubleshooting methodology should a technician take to confirm a theory?
Following a fire in a data center, the cabling was replaced. Soon after, an administrator notices network issues. Which of the following are the most likely causes of the network issues? (Select two).
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses (one for a computer and one for a phone). Which of the following classful IPv4 address ranges will be best-suited for the network?
In an environment with one router, which of the following will allow a network engineer to communicate between VLANs without purchasing additional hardware?
A company ' s network is experiencing high levels of suspicious network traffic. The security team finds that the traffic is coming from an unknown, foreign IP address. Which of the following is the most cost-efficient way to mitigate this threat?
Developers want to create a mobile application that requires a runtime environment, developer tools, and databases. The developers will not be responsible for security patches and updates. Which of the following models meets these requirements?
A junior network administrator gets a text message from a number posing as the domain registrar of the firm. The administrator is tricked into providing global administrator credentials. Which of the following attacks is taking place?
A technician is deploying new networking hardware for company branch offices. The bridge priority must be properly set. Which of the following should the technician configure?
A network administrator manages multiple computers and notices that three computers are no longer communicating with the network. Which of the following commands best identifies whether other devices are restricting packet traffic?
A company discovers on video surveillance recordings that an unauthorized person installed a rogue access point in its secure facility. Which of the following allowed the unauthorized person to do this?
In the troubleshooting methodology, which of the following actions comes after verifying that the initial problem has been resolved?
A network administrator recently upgraded a wireless infrastructure with new APs. Users report that when stationary, the wireless connection drops and reconnects every 20 to 30 seconds. While reviewing logs, the administrator notices the APs are changing channels.
Which of the following is the most likely reason for the service interruptions?
Which of the following allows the fastest recovery during a catastrophe event?
A network administrator is conducting an assessment and finds network devices that do not meet standards. Which of the following configurations is considered a set of rules that devices should adhere to?
A user called the help desk after business hours to complain that files on a device are inaccessible and the wallpaper was changed. The network administrator thinks that this issue is an isolated incident, but the security analyst thinks the issue might be a ransomware attack. Which of the following troubleshooting steps should be taken first?
Which of the following does a router prioritize first in the route selection process?
A company is implementing a wireless solution in a high-density environment. Which of the following 802.11 standards is used when a company is concerned about device saturation and converage?
A company upgrades its wireless infrastructure with a 1Gbps backbone, new APs, and new tablets for all employees. However, the IT department notes that speeds are not improved from the previous tablets. Given the following network information, which of the following is the most likely cause of the performance issues?
A technician needs to set up a wireless connection that utilizes MIMO on non-overlapping channels. Which of the following would be the best choice?
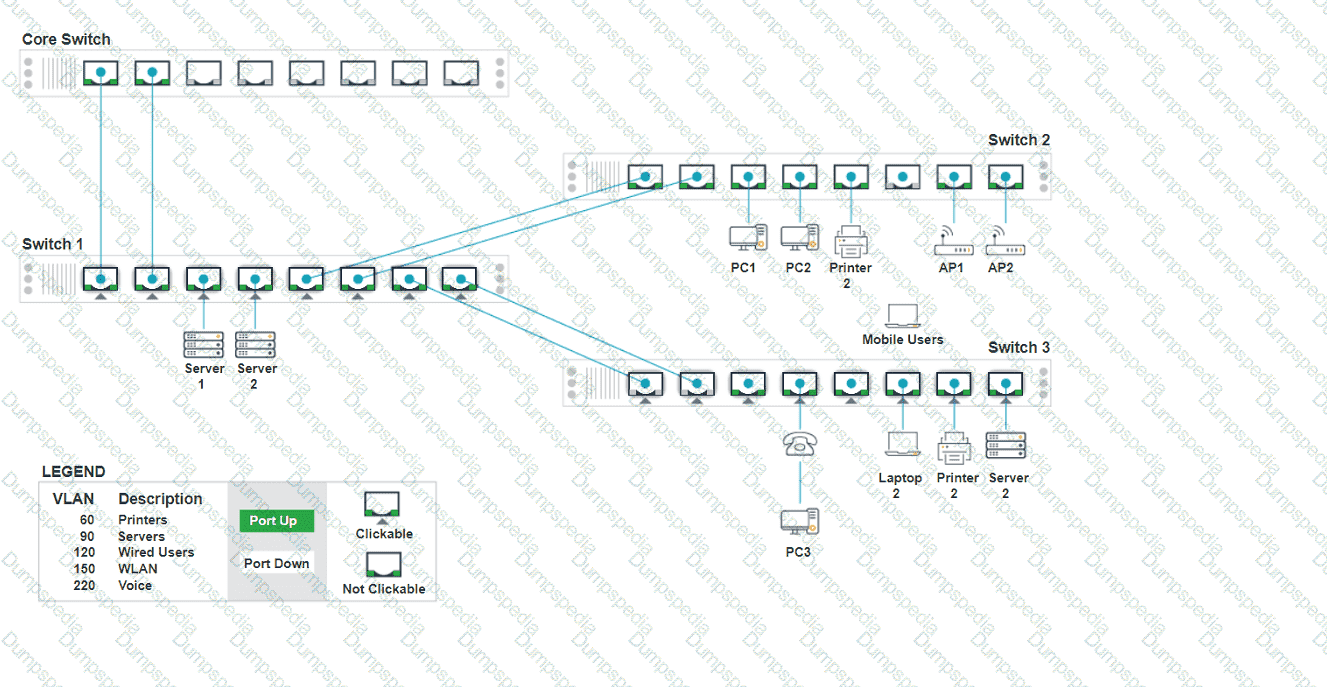
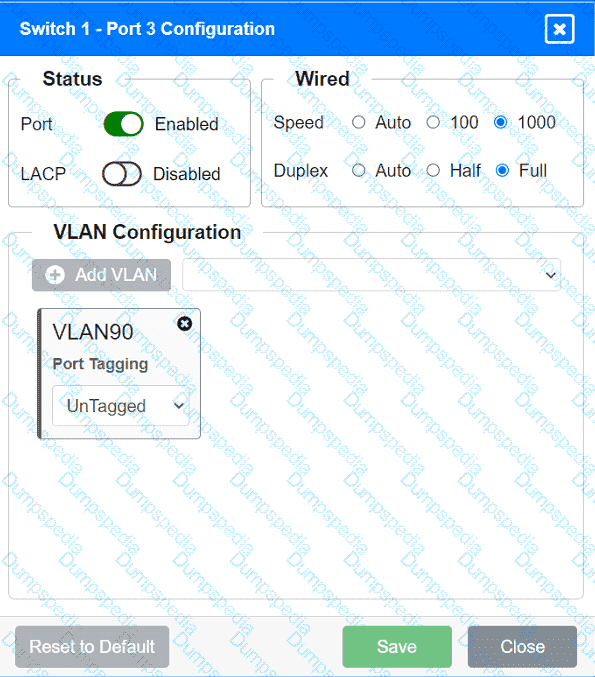
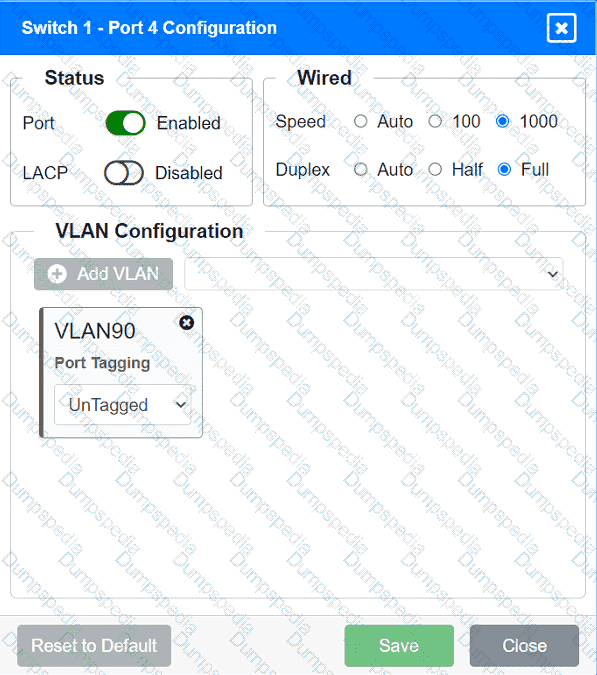
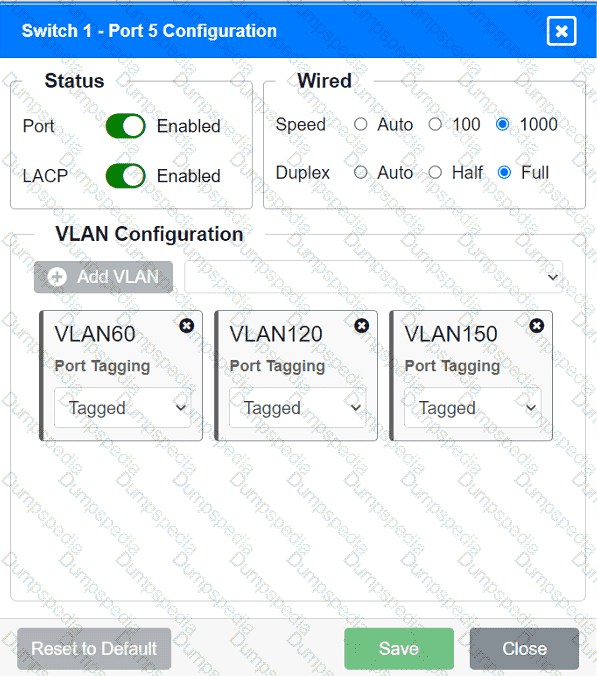
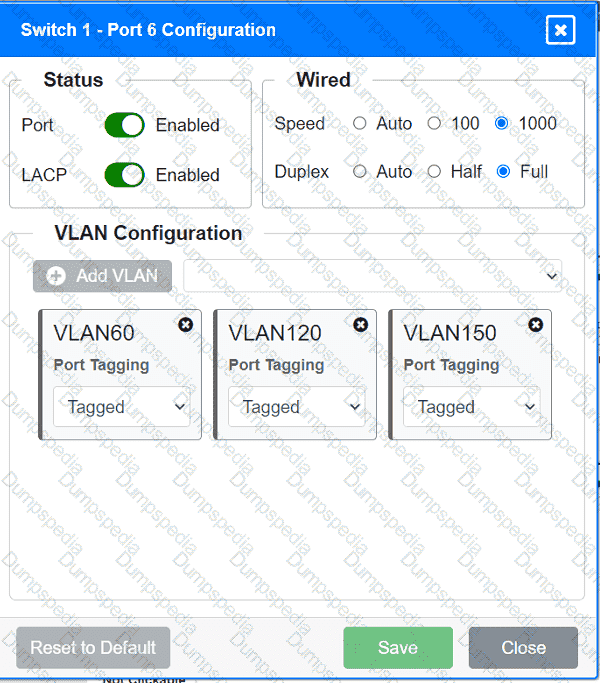
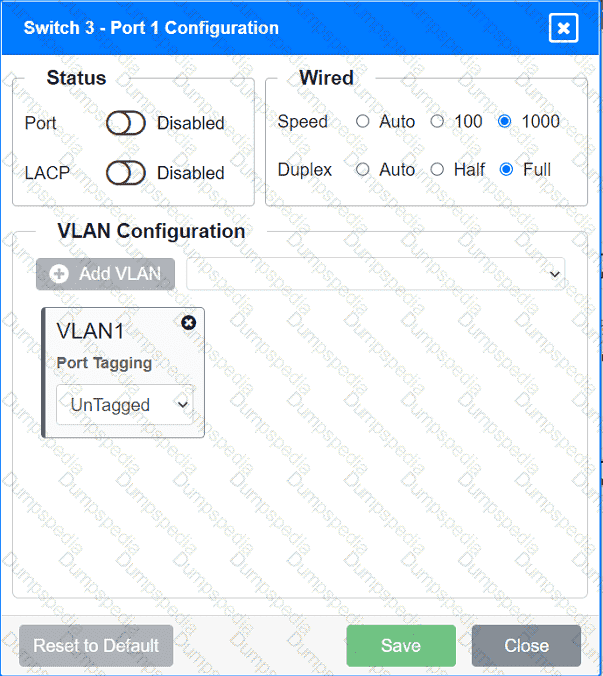
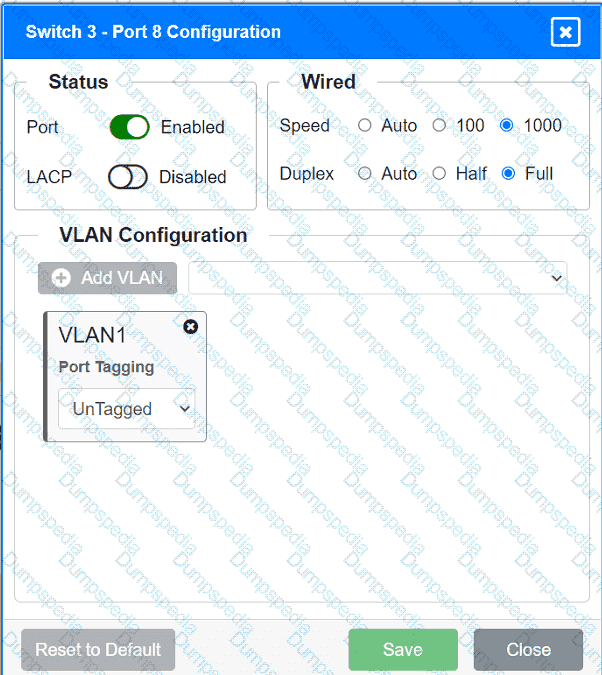
A network technician replaced an access layer switch and needs to reconfigure it to allow the connected devices to connect to the correct networks.
INSTRUCTIONS
Click on the appropriate port(s) on Switch 1 and Switch 3 to verify or reconfigure the
correct settings:
· Ensure each device accesses only its
correctly associated network.
· Disable all unused switchports.
. Require fault-tolerant connections
between the switches.
. Only make necessary changes to
complete the above requirements.
A network administrator is configuring a new switch and wants to ensure that only assigned devices can connect to the switch. Which of the following should the administrator do?
Which of the following troubleshooting steps would provide a change advisory board with the information needed to make a decision?
An investment bank is seeking a DR backup solution. Which of the following provides the most cost-effective backup site?
A network administrator upgraded the wireless access points and wants to implement a configuration that will give users higher speed and less channel overlap based on device compatibility. Which of the following will accomplish this goal?
An employee has a new laptop and reports slow performance when using the wireless network. Switch firmware was updated the previous night. A network administrator logs in to the switch and sees the following statistics on the switch interface for that employee:
98469 packets input, 1681937 bytes, 0 no buffer
Received 1548 broadcasts (25285 multicasts)
65335 runts, 0 giants, 0 throttles
11546 input errors, 5 CRC, 0 frame, 0 overrun, 0 ignored
0 input packets with dribble condition detected
22781 packets output, 858040 bytes, 0 underruns
0 output errors, 89920 collisions, 0 interface resets
0 babbles, 0 late collision, 0 deferred
0 lost carrier, 0 no carrier
0 output buffer failures, 0 output buffers swapped out
Which of the following is most likely the cause of the issue?
A network technician is attempting to harden a commercial switch that was recently purchased. Which of the following hardening techniques best mitigates the use of publicly available information?
Which of the following allows a user to authenticate to multiple resources without requiring additional passwords?
An attacker gained access to the hosts file on an endpoint and modified it. Now, a user is redirected from the company’s home page to a fraudulent website. Which of the following most likely happened?
A network administrator upgrades the wireless access points and wants to implement a configuration that gives users higher speed and less channel overlap based on device compatibility. Which of the following accomplishes this goal?
After a company installed a new IPS, the network is experiencing speed degradation. A network administrator is troubleshooting the issue and runs a speed test. The results from the different network locations are as follows:
LocationSpeed DownSpeed Up
Wireless laptop4.8 Mbps47.1 Mbps
Wired desktop5.2 Mbps49.3 Mbps
Firewall48.8 Mbps49.5 Mbps
Which of the following is the most likely issue?
An organization wants better network visibility. The organization ' s requirements include:
Multivendor/OS-monitoring capabilities
Real-time collection
Data correlation
Which of the following meets these requirements?
A network technician is troubleshooting network latency and has determined the issue to be occuring two network switches( Switch10 and Switch11). Symptoms reported included poor video performance and slow file copying. Given the following informtion:
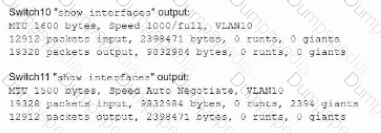
Which of the following should the technician most likely do to resolve the issue?
A company is migrating a data center from on premises to the cloud. Which of the following tools will help maintain consistency, reliability, and efficiency of provisioning and management?
A network engineer is completing a new VoIP installation, but the phones cannot find the TFTP server to download the configuration files. Which of the following DHCP features would help the phone reach the TFTP server?
Which of the following panels would be best to facilitate a central termination point for all network cables on the floor of a company building?
Which of the following attacks forces a switch to send all traffic out of all ports?
A user ' s desk has a workstation and an IP phone. The user is unable to browse the internet on the workstation, but the phone works. Which of the following configurations is required?
A network consultant needs to decide between running an ethernet uplink or using the built-in 5GHz-to-point functionality on a WAP. Which of the following documents provides the best information to assist the consultant with this decision?
Which of the following OSI model layers can utilize a connectionless protocol for data transmission?
Which of the following ports should a network administrator enable for encrypted login to a network switch?
After a security incident, a technician reveals that company data was stolen. During the investigation, it is discovered that a host disguised itself as a switch. Which of the following best describes the attack that occurred?
A network administrator is reviewing a production web server and observes the following output from the netstat command:
Which of the following actions should the network administrator take to harden the security of the web server?
A systems administrator is investigating why users cannot reach a Linux web server with a browser but can ping the server IP. The server is online, the web server process is running, and the link to the switch is up. Which of the following commands should the administrator run on the server first?
A network engineer receives a vendor alert regarding a vulnerability in a router CPU. Which of the following should the engineer do to resolve the issue?
Which of the following types of connectors allows the transmission of network data through a coaxial cable?
Which of the following is the most cost-effective way for a network administrator to establish a persistent, secure connection between two facilities?
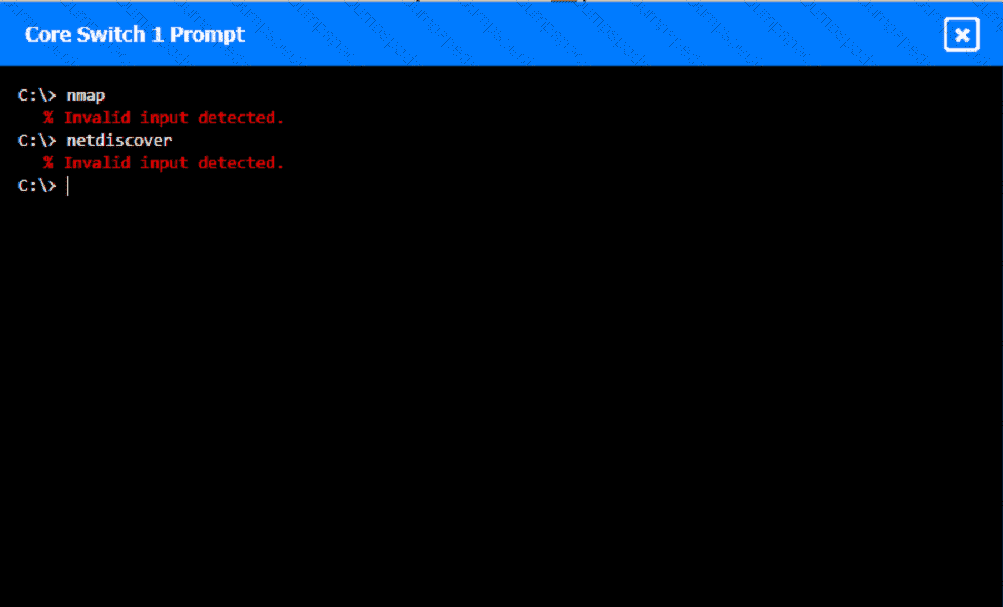
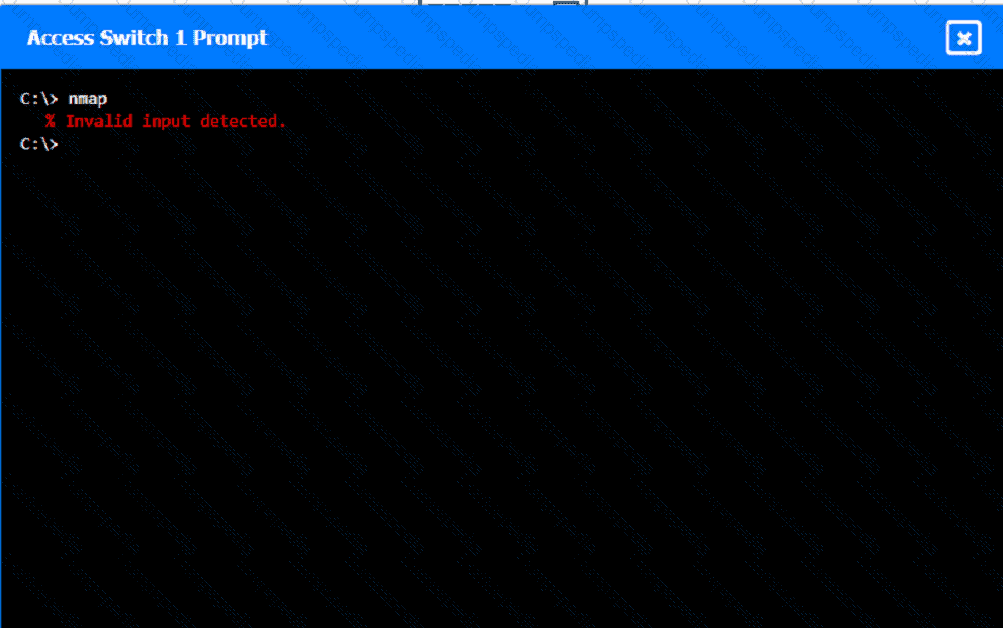
A network technician was recently onboarded to a company. A manager has
tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
A company recently experienced outages of one of its critical, customer-facing applications. The root cause was an overutilized network router, but the Chief Technology Officer is concerned that the support staff was unaware of the issue until notified by customers. Which of the following is the best way to address this issue in the future?
A network technician is working on a PC with a faulty NIC. The host is connected to a switch with secured ports. After testing the connection cables and using a known-good NIC, the host is still unable to connect to the network. Which of the following is causing the connection issue?
Which of the following steps of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified?