A penetration tester is attempting to scan an internal corporate network from the internet without alerting the border sensor. Which is the most efficient technique should the tester consider using?
What results will the following command yield: 'NMAP -sS -O -p 123-153 192.168.100.3'?
After gaining access to the password hashes used to protect access to a web based application, knowledge of which cryptographic algorithms would be useful to gain access to the application?
Which of the following viruses tries to hide from anti-virus programs by actively altering and corrupting the chosen service call interruptions when they are being run?
What is the primary drawback to using advanced encryption standard (AES) algorithm with a 256 bit key to share sensitive data?
An IT security engineer notices that the company’s web server is currently being hacked. What should the engineer do next?
Which of the following defines the role of a root Certificate Authority (CA) in a Public Key Infrastructure (PKI)?
Which NMAP feature can a tester implement or adjust while scanning for open ports to avoid detection by the network’s IDS?
Which of the following levels of algorithms does Public Key Infrastructure (PKI) use?
When comparing the testing methodologies of Open Web Application Security Project (OWASP) and Open Source Security Testing Methodology Manual (OSSTMM) the main difference is
Which NMAP command combination would let a tester scan every TCP port from a class C network that is blocking ICMP with fingerprinting and service detection?
Diffie-Hellman (DH) groups determine the strength of the key used in the key exchange process. Which of the following is the correct bit size of the Diffie-Hellman (DH) group 5?
On a Linux device, which of the following commands will start the Nessus client in the background so that the Nessus server can be configured?
A hacker searches in Google for filetype:pcf to find Cisco VPN config files. Those files may contain connectivity passwords that can be decoded with which of the following?
A recently hired network security associate at a local bank was given the responsibility to perform daily scans of the internal network to look for unauthorized devices. The employee decides to write a script that will scan the network for unauthorized devices every morning at 5:00 am.
Which of the following programming languages would most likely be used?
Which of the following parameters enables NMAP's operating system detection feature?
A computer technician is using a new version of a word processing software package when it is discovered that a special sequence of characters causes the entire computer to crash. The technician researches the bug and discovers that no one else experienced the problem. What is the appropriate next step?
A certified ethical hacker (CEH) completed a penetration test of the main headquarters of a company almost two months ago, but has yet to get paid. The customer is suffering from financial problems, and the CEH is worried that the company will go out of business and end up not paying. What actions should the CEH take?
Which initial procedure should an ethical hacker perform after being brought into an organization?
A tester has been hired to do a web application security test. The tester notices that the site is dynamic and must make use of a back end database.
In order for the tester to see if SQL injection is possible, what is the first character that the tester should use to attempt breaking a valid SQL request?
What is a successful method for protecting a router from potential smurf attacks?
An ethical hacker for a large security research firm performs penetration tests, vulnerability tests, and risk assessments. A friend recently started a company and asks the hacker to perform a penetration test and vulnerability assessment of the new company as a favor. What should the hacker's next step be before starting work on this job?
A consultant has been hired by the V.P. of a large financial organization to assess the company's security posture. During the security testing, the consultant comes across child pornography on the V.P.'s computer. What is the consultant's obligation to the financial organization?
A certified ethical hacker (CEH) is approached by a friend who believes her husband is cheating. She offers to pay to break into her husband's email account in order to find proof so she can take him to court. What is the ethical response?
Which of the following tools would be the best choice for achieving compliance with PCI Requirement 11?
Which United States legislation mandates that the Chief Executive Officer (CEO) and the Chief Financial Officer (CFO) must sign statements verifying the completeness and accuracy of financial reports?
Which of the following ensures that updates to policies, procedures, and configurations are made in a controlled and documented fashion?
Which of the following guidelines or standards is associated with the credit card industry?
Which method can provide a better return on IT security investment and provide a thorough and comprehensive assessment of organizational security covering policy, procedure design, and implementation?
When does the Payment Card Industry Data Security Standard (PCI-DSS) require organizations to perform external and internal penetration testing?
How do employers protect assets with security policies pertaining to employee surveillance activities?
International Organization for Standardization (ISO) standard 27002 provides guidance for compliance by outlining
What is the correct PCAP filter to capture all TCP traffic going to or from host 192.168.0.125 on port 25?
When using Wireshark to acquire packet capture on a network, which device would enable the capture of all traffic on the wire?
At a Windows Server command prompt, which command could be used to list the running services?
While performing data validation of web content, a security technician is required to restrict malicious input. Which of the following processes is an efficient way of restricting malicious input?
A hacker was able to sniff packets on a company's wireless network. The following information was discovered:

Using the Exlcusive OR, what was the original message?
Which of the following types of firewall inspects only header information in network traffic?
Which of the following resources does NMAP need to be used as a basic vulnerability scanner covering several vectors like SMB, HTTP and FTP?
Which of the following techniques does a vulnerability scanner use in order to detect a vulnerability on a target service?
A company firewall engineer has configured a new DMZ to allow public systems to be located away from the internal network. The engineer has three security zones set:

The engineer wants to configure remote desktop access from a fixed IP on the remote network to a remote desktop server in the DMZ. Which rule would best fit this requirement?
A consultant is hired to do physical penetration testing at a large financial company. In the first day of his assessment, the consultant goes to the company`s building dressed like an electrician and waits in the lobby for an employee to pass through the main access gate, then the consultant follows the employee behind to get into the restricted area. Which type of attack did the consultant perform?
The network administrator for a company is setting up a website with e-commerce capabilities. Packet sniffing is a concern because credit card information will be sent electronically over the Internet. Customers visiting the site will need to encrypt the data with HTTPS. Which type of certificate is used to encrypt and decrypt the data?
WPA2 uses AES for wireless data encryption at which of the following encryption levels?
The precaution of prohibiting employees from bringing personal computing devices into a facility is what type of security control?
A pentester gains access to a Windows application server and needs to determine the settings of the built-in Windows firewall. Which command would be used?
When creating a security program, which approach would be used if senior management is supporting and enforcing the security policy?
What is the most secure way to mitigate the theft of corporate information from a laptop that was left in a hotel room?
What is the name of the international standard that establishes a baseline level of confidence in the security functionality of IT products by providing a set of requirements for evaluation?
Which of the following scanning tools is specifically designed to find potential exploits in Microsoft Windows products?
Which type of access control is used on a router or firewall to limit network activity?
A security consultant decides to use multiple layers of anti-virus defense, such as end user desktop anti-virus and E-mail gateway. This approach can be used to mitigate which kind of attack?
What is the main advantage that a network-based IDS/IPS system has over a host-based solution?
Which of the following conditions must be given to allow a tester to exploit a Cross-Site Request Forgery (CSRF) vulnerable web application?
Which results will be returned with the following Google search query?
site:target.com -site:Marketing.target.com accounting
Which of the following lists are valid data-gathering activities associated with a risk assessment?
When utilizing technical assessment methods to assess the security posture of a network, which of the following techniques would be most effective in determining whether end-user security training would be beneficial?
A bank stores and processes sensitive privacy information related to home loans. However, auditing has never been enabled on the system. What is the first step that the bank should take before enabling the audit feature?
The following is a sample of output from a penetration tester's machine targeting a machine with the IP address of 192.168.1.106:

What is most likely taking place?
What type of OS fingerprinting technique sends specially crafted packets to the remote OS and analyzes the received response?
A penetration tester is hired to do a risk assessment of a company's DMZ. The rules of engagement states that the penetration test be done from an external IP address with no prior knowledge of the internal IT systems. What kind of test is being performed?
Passive reconnaissance involves collecting information through which of the following?
What is one thing a tester can do to ensure that the software is trusted and is not changing or tampering with critical data on the back end of a system it is loaded on?
A penetration tester was hired to perform a penetration test for a bank. The tester began searching for IP ranges owned by the bank, performing lookups on the bank's DNS servers, reading news articles online about the bank, watching what times the bank employees come into work and leave from work, searching the bank's job postings (paying special attention to IT related jobs), and visiting the local dumpster for the bank's corporate office. What phase of the penetration test is the tester currently in?
The following is part of a log file taken from the machine on the network with the IP address of 192.168.1.106:

What type of activity has been logged?
John the Ripper is a technical assessment tool used to test the weakness of which of the following?
If the final set of security controls does not eliminate all risk in a system, what could be done next?
A Security Engineer at a medium-sized accounting firm has been tasked with discovering how much information can be obtained from the firm's public facing web servers. The engineer decides to start by using netcat to port 80.
The engineer receives this output:
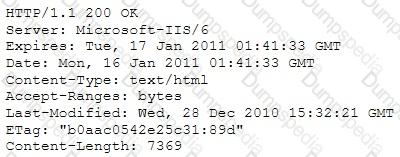
Which of the following is an example of what the engineer performed?
Seth is starting a penetration test from inside the network. He hasn't been given any information about the network. What type of test is he conducting?
Port scanning can be used as part of a technical assessment to determine network vulnerabilities. The TCP XMAS scan is used to identify listening ports on the targeted system.
If a scanned port is open, what happens?
Windows LAN Manager (LM) hashes are known to be weak.
Which of the following are known weaknesses of LM? (Choose three.)
Which of the following tools performs comprehensive tests against web servers, including dangerous files and CGIs?
Due to a slowdown of normal network operations, IT department decided to monitor internet traffic for all of the employees. From a legal stand point, what would be troublesome to take this kind of measure?
You have compromised a server on a network and successfully opened a shell. You aimed to identify all operating systems running on the network. However, as you attempt to fingerprint all machines in the network using the nmap syntax below, it is not going through.

What seems to be wrong?
Knowing the nature of backup tapes, which of the following is the MOST RECOMMENDED way of storing backup tapes?
Using Windows CMD, how would an attacker list all the shares to which the current user context has access?
Destination unreachable administratively prohibited messages can inform the hacker to what?
Which of the following is considered the best way to protect Personally Identifiable Information (PII) from Web application vulnerabilities?
The practical realities facing organizations today make risk response strategies essential. Which of the following is NOT one of the five basic responses to risk?
A software tester is randomly generating invalid inputs in an attempt to crash the program. Which of the following is a software testing technique used to determine if a software program properly handles a wide range of invalid input?
Susan has attached to her company's network. She has managed to synchronize her boss's sessions with that of the file server. She then intercepted his traffic destined for the server, changed it the way she wanted to and then placed it on the server in his home directory.
What kind of attack is Susan carrying on?
LM hash is a compromised password hashing function. Which of the following parameters describe LM Hash:?
I – The maximum password length is 14 characters.
II – There are no distinctions between uppercase and lowercase.
III – It’s a simple algorithm, so 10,000,000 hashes can be generated per second.
If there is an Intrusion Detection System (IDS) in intranet, which port scanning technique cannot be used?
You are trying to break into a highly classified top-secret mainframe computer with highest security system in place at Merclyn Barley Bank located in Los Angeles.
You know that conventional hacking doesn't work in this case, because organizations such as banks are generally tight and secure when it comes to protecting their systems.
In other words, you are trying to penetrate an otherwise impenetrable system.
How would you proceed?
What network security concept requires multiple layers of security controls to be placed throughout an IT infrastructure, which improves the security posture of an organization to defend against malicious attacks or potential vulnerabilities?
Which of the following is designed to identify malicious attempts to penetrate systems?
Sandra has been actively scanning the client network on which she is doing a vulnerability assessment test.
While conducting a port scan she notices open ports in the range of 135 to 139.
What protocol is most likely to be listening on those ports?
Bluetooth uses which digital modulation technique to exchange information between paired devices?
Which of the following can the administrator do to verify that a tape backup can be recovered in its entirety?
Which of the following is a hardware requirement that either an IDS/IPS system or a proxy server must have in order to properly function?
Which of the following programs is usually targeted at Microsoft Office products?
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the corporate network. What tool should the analyst use to perform a Blackjacking attack?
Which of the following is an application that requires a host application for replication?
Which statement is TRUE regarding network firewalls preventing Web Application attacks?