The network environment is becoming more and more complex, and network security incidents occur frequently. While accelerating the construction of informatization, enterprises must not only resist external attacks, but also prevent internal management personnel from being involved in data leakage and operation and maintenance accidents due to operational errors and other issues. Which of the following options might reduce operational risk?
The following description of asymmetric encryption algorithms, which item is wrong?
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.

How frequently should antivirus signature databases be updated to ensure the effectiveness of an antivirus program or software?
Which of the following statements are correct about SYN flood attack defense technologies on Huawei firewalls?
HTTPS introduces the TLS layer based on HTTP to provide identity authentication, encryption, and integrity check for data transmission.
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
For which of the following parameters can the packet filtering firewall filter?
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
Which type of NAT translates both addresses and port numbers and uses the public IP address of the outbound interface as the post-NAT address?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
DES is a stream encryption algorithm, because the cipher capacity is only 56 bits, so it is not enough to deal with the weakness of insufficient security, and later 3DES was proposed.
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules?
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
Under normal circumstances, the Emai1 protocols we often talk about include ____, POP3, and SMTP.[fill in the blank]*
According to the level protection requirements, which of the following behaviors belong to the scope of information security operation and maintenance management? ( )*
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
Which of the following is not the matching mode of the firewall security protection whitelist rules?
Which type of NAT applies to the scenario where there are a small number of Internet access users and the number of public IP addresses is the same as the number of concurrent Internet access users?
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
The following description of the construction of a digital certificate, which item is wrong
What are the correct entries in the following description of firewall security zones?
The trigger modes of the built-in Portal authentication in the firewall include pre-authentication and ____ authentication[fill in the blank]*
When the Layer 2 switch receives a unicast frame and the MAC address table entry of the switch is empty, the switch discards the unicast frame.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
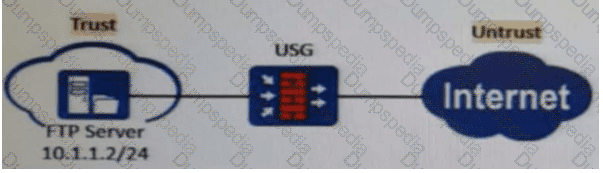
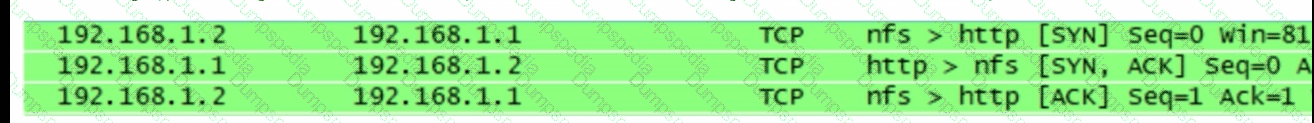
As shown in the figure, packet obtaining software is used to obtain some packets on a terminal. Which of the following statements is correct about the obtained packet information?
Which of the following statements is correct about security zones on a Huawei firewall?