When the license of Huawei USG6000 product expires, the RBL function will be unavailable, and users can only use the local black and white list to filter junk mail.
155955cc-666171a2-20fac832-0c042c0435
Malicious code usually uses RootKit technology in order to hide itself. RootKit modifies the kernel of the system by loading a special driver.
To hide itself and the role of designated files.
Which of the following is the default port number of Portal authentication service?
The main attack prevention technologies of Huawei USG6000 products include: source detection, fingerprint learning and associated defense.
Which three aspects should be considered in the design of cloud platform security solutions? (multiple choice)
For the basic mode of HTTP Flood source authentication, which of the following options are correct? (multiple choice)
SQl injection attacks generally have the following steps:
①Elevate the right
②Get the data in the database
③Determine whether there are loopholes in the webpage
④ Determine the database type
For the ordering of these steps, which of the following options is correct?
If the processing strategy for SMTP virus files is set to alert, which of the following options is correct?
Which of the following features does Huawei NIP intrusion prevention equipment support? (multiple choice)
When using the two-way SSL function to decrypt HTTPS packets, the value of the reverse proxy level represents the number of times the packet can be decrypted.
The administrator has defined two key words that need to be recognized on the firewall: the weight of the keyword x is 2, and the weight of the key y is 3: defined
The alarm interval value from the content is 5, and the blocking threshold value is 10. If the device detects that there is a secondary key space x in the webpage created by the user, the two keywords are
Y; Regarding the weight value and monthly household visits to Heshun Street, is the following statement correct?
Cloud sandbox refers to deploying the sandbox in the cloud and providing remote detection services for tenants. The process includes:
1. Report suspicious files
2. Retrospective attack
3. Firewall linkage defense
4. Prosecution in the cloud sandbox
For the ordering of the process, which of the following options is correct?
For SYIN Flood attacks, TCP source authentication and TCP proxy can be used for defense. Which of the following descriptions is correct?
Huawei USG6000 products can scan and process certain file transfer protocols for viruses, but which of the following protocols is not included?
Regarding the 3 abnormal situations of the file type recognition result, which of the following option descriptions is wrong?
Regarding the anti-spam local black and white list, which of the following statements is wrong?
Server Fault information collection tool Server Collector, which of the following does collected information items not include?
Tianyu Nei answered the role of safety filtering technology, which of the following is still correct? (multiple choice)
The process of a browser carrying a cookie to request resources from a server is shown in the following figure. Which of the following steps contains SessionID information in the message?

In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
For the description of the principles of HTTP Flood and HTTPS Flood blow defense, which of the following options are correct? (multiple choice)
Configure the following commands on the Huawei firewall:
[USG] interface G0/0/1
[USG] ip urpf loose allow-defult-route acl 3000
Which of the following options are correct? (multiple choice)
The core technology of content security lies in anomaly detection, and the concept of defense lies in continuous monitoring and analysis.
Anti-DDoS defense system includes: management center, detection center and cleaning center.
Regarding the Anti-DDoS cloud cleaning solution; which of the following statements is wrong?
Which of the following options describes the IntelliSense engine IAE incorrectly?
Among the following options, which attack is a malformed packet attack based on the TCR protocol?
The anti-virus feature configured on the Huawei USG6000 product does not take effect. Which of the following are the possible reasons? (multiple choice)
Regarding the processing process of file overwhelming, which of the following statements is correct?
Content filtering is a security mechanism for filtering the content of files or applications through Huawei USCG00 products. Focus on the flow through deep recognition
Contains content, the device can block or alert traffic containing specific keywords.
With regard to APT attacks, the attacker often lurks for a long time and launches a formal attack on the enterprise at the key point of the incident.
Generally, APT attacks can be summarized into four stages:
1. Collecting Information & Intrusion
2. Long-term lurking & mining
3. Data breach
4. Remote control and penetration
Regarding the order of these four stages, which of the following options is correct?
Regarding the description of file reputation technology in anti-virus engines, which of the following options is correct?
Which of the following options are the possible reasons why a certain signature is not included after the IPS policy configuration is completed? (multiple choice)
Network attacks are mainly divided into two categories: single-packet attacks and streaming attacks. Single-packet attacks include scanning and snooping attacks, malformed packet attacks, and special reports.
Wen attack.
Buffer overflows, Trojan horses, and backdoor attacks are all attacks at the application layer.
Huawei's USG000 product can identify the true type of common files and over-check the content. Even if the file is hidden in a compressed file, or change the extension
The name of the exhibition can't escape the fiery eyes of the firewall.
Which of the following is the correct configuration idea for the anti-virus strategy?
1. Load the feature library
2. Configure security policy and reference AV Profile
3. Apply and activate the license
4. Configure AV Profile
5. Submit
The user needs of a university are as follows:
1. The environment is large, and the total number of two-way traffic can reach 800M. Huawei USG6000 series firewall is deployed at its network node.
2. The intranet is divided into student area, server area, etc., users are most concerned about the security of the server area to avoid attacks from various threats.
3. At the same time, some pornographic websites in the student area are prohibited.
The external network has been configured as an untrust zone and the internal network has been configured as a trust zone on the firewall. How to configure the firewall to meet the above requirements?
155955cc-666171a2-20fac832-0c042c0415
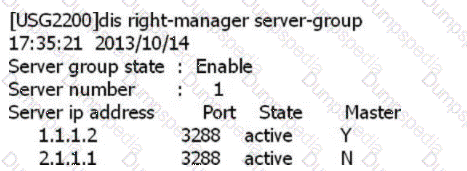
SACG query right-manager information as follows, which options are correct? (Select 2 answers)
USG6000V software logic architecture is divided into three planes: management plane, control plane and
The following is a hardware SACG increase firewall configuration, which statement below is true?

Which of the following options does not belong to the basic DDoS attack prevention configuration process?
Which of the following options is not a cyber security threat caused by weak personal security awareness?
Huawei WAF products are mainly composed of front-end execution, back-end central systems and databases. Among them, the database mainly stores the front-end detection rules and black
Whitelist and other configuration files.
A True
B. False
In Huawei USG6000 products, IAE provides an integrated solution, all content security detection functions are integrated in a well-designed
In the high-performance engine. Which of the following is not the content security detection function supported by this product?
Which of the following options does not belong to the security risk of the application layer of the TCP/IP protocol stack?
In the big data intelligent security analysis platform, it is necessary to collect data from data sources, and then complete a series of actions such as data processing, detection and analysis, etc.
do. Which of the following options does not belong to the action that needs to be completed in the data processing part?
155955cc-666171a2-20fac832-0c042c0422
In the Policy Center strategy configuration, how many violations rating of definition are there?
Huawei NIP6000 products have zero-setting network parameters and plug-and-play functions, because the interfaces and interface pairs only work on layer 2 without
Set the IP address.
A True
B. False