The following figure shows the inter-AS MPLS VPN Option B solution. If ASBR-PE1 and ASBR-PE2 only transmit VPNv4 routes, you can run the following command on ASBR-PE1:
[ASBR-PE1-bgp-af-vpnv4] undo peer 10.0.34.4 enable
Which of the following statements about SR-MPLS characteristics are correct? (Select all that apply)
On a VXLAN-based virtualized campus network, BGP EVPN can be used as the control plane protocol. Which of the following EVPN route types are not used in the virtualized campus network scenario?
Which of the following statements about prefix segments and adjacency segments are correct?
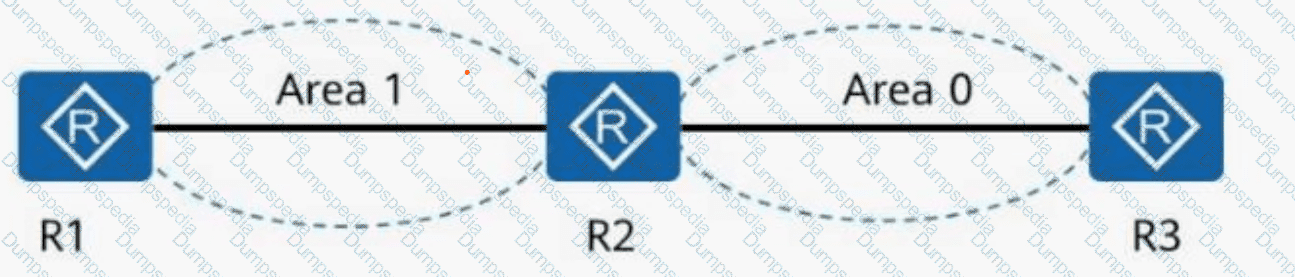
What can be determined from the following IS-IS peer output?
Peer information for ISIS(1):
Peer System ID: ee8c.a0c2.baf3
Interface: GE0/0/0
State: Up
HoldTime: 7s
Type: L1
PRI: 64
MT IDs supported: 0(UP), 2(UP)
Local MT IDs: 0, 2
Area Address(es): 49.0022
Peer IP Address(es): 10.1.34.1
Peer IPv6 Address(es): FE80::2E0:FCFF:FE98:2576
Which of the following statements is incorrect about adding devices on a virtualized network deployed using iMaster NCE-Campus?
As shown in the figure, what is known about the default routes on R4?
Routing Table on R4:
< R4 > display ip routing-table protocol isis
Destination/Mask Proto Pre Cost Flags NextHop Interface
0.0.0.0/0 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
172.16.1.2/32 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
172.16.1.3/32 ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
BGP EVPN can be used as the VXLAN control plane protocol to completely prevent traffic flooding, such as broadcast ARP packets, on the VXLAN network.
Which of the following statements about SR-MPLS Policy candidate paths are correct?
HTTP is an application layer protocol for distributed, collaborative, and hypermedia information systems.
If SRv6 needs to be deployed on a bearer WAN, which of the following technologies are required? (Select all that apply)
An Ethernet Segment Identifier (ESI) is 10 bytes long and unique on the entire network.
During the migration test, which of the following indicates that the test is completed?
Telemetry is a technology that remotely collects data from physical or virtual devices at high speed, and has a layered protocol stack. Which of the following layers is not included in the telemetry protocol stack?
An LSR (Label Switching Router) supports various label retention modes. Which of the following statements regarding the liberal mode are correct?
Before connecting an SSH client to an SSH server in public key authentication mode, a client needs to create a key pair. Which of the following commands is used to create a DSS key pair on the client using Git Bash?
Which of the following statements are correct about the authentication protocols used in Portal authentication?
In the firewall hot standby scenario, when VGMP works in load balancing mode, which of the following functions must be enabled on the firewalls to prevent the return traffic from being discarded because it does not match any session entry in the case of inconsistent forward and return paths?
Collecting information before a cutover helps you determine whether services are normal before and after the cutover.
In SRv6, each time a packet passes through an SRv6 endpoint node, the Segments Left field value decrements by 1, and the IPv6 DA changes.
In the following figure, all routers are running OSPF. Given this, which of the following statements is correct?
You write the following Python code to invoke a RESTful API to obtain the token ID of iMaster NCE. Which of the following statements are correct?
import requests
response = requests.get( " https://139.9.213.72 " )
print(response.json())
Error returned:
requests.exceptions.SSLError: HTTPSConnectionPool(host= ' 139.9.213.72 ' , port=18002): Max retries exceeded with url: /controller/v2/tokens (Caused by SSLError(CertificateError( ' hostname ' 139.9.213.72 ' doesn ' t match ' devzone.huawei.com ' )))
Options:
A network administrator runs the display telemetry destination command on a device to check information about a destination group that sampled data is sent to. The command output is as follows. Which of the following statements is incorrect?
[~CE-telemetry-sensor-group-Sensor1]display telemetry destination
Dest-name Dest-addr Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20000 RESOLVED - GRPC
SSH connections are usually established based on TCP/IP connections. In specific cases, SSH connections can be established based on UDP connections.
In 6PE networking, the shared explicit null label function can be enabled on routers to reduce the number of required MPLS labels. With this function, a router assigns a label with the value (enter only digits) to all 6PE routes.
A network administrator runs the display telemetry subscription command on a device to check telemetry subscription information. The command output is as follows. Which of the following statements is incorrect?
[~CE] display telemetry subscription
Sub name : Sub1
Sensor group:
Sensor-name Sample-interval(ms) State
Sensor1 1000 RESOLVED
Destination group:
Dest-name Dest-IP Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20030 RESOLVED - GRPC
Sub state : PASSIVE
Total subscription number is : 1
Which of the following statements regarding OSPF neighbor relationship faults is incorrect?
The display current-configuration command displays the running configurations in memory.
In the Huawei CloudCampus Solution, which of the following devices can go online through the registration query center?
The RR (Route Reflector) is critical to the Huawei SD-WAN Solution, and its deployment mode varies based on the scenario. In which of the following modes can an RR be deployed?
Which of the following number sequences can be matched by the regular expression 100.s?
On a small- or medium-sized campus network deployed based on the Huawei CloudCampus Solution, an AR functioning as the egress gateway supports web-based network management, registration center query, and DHCP Option 148-based deployment, but does not support CLI-based deployment.
Among NETCONF operations, the < config > operation may contain an operation attribute, which is used to specify an operation type for configuration data. Which of the following operation attributes is incorrect?
Flavors can be used to enhance SRv6 instructions to meet more diversified service requirements. Which of the following are flavors? (Select all that apply)
On traditional campus networks, network admission control (NAC), VLAN, and ACL technologies are used to control users ' network access rights. This results in heavy network O & M workload. Which of the following improvements does the free mobility solution of iMaster NCE-Campus make to traditional campus networks in terms of policy management and control?
At the NETCONF content layer, the < config > operation may contain an operation attribute, which is used to specify an operation type for configuration data. Which of the following operation attributes are supported?
In Huawei Open Programmability System (OPS), /ifm/interfaces/interface is the URL used to identify a device ' s managed object.
As shown in the figure, PE1 establishes an EVPN peer relationship with each of PE2 and PE3. When the network is initialized, CE1 sends an ARP request packet.
Which of the following statements are correct about how a PE processes the packet?
Refer to the following command output on the router R1. Which of the following statements is incorrect?
< R1 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:23 UTC-08:00
Description: ! 0.0.3.3
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.1/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.1.1 (LoopBack0), destination 10.0.3.3
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
Current system time: 15:21:37-08:00
300 seconds input rate 0 bits/sec, 0 packets/sec
300 seconds output rate 0 bits/sec, 0 packets/sec
13 seconds input rate 0 bits/sec, 0 packets/sec
13 seconds output rate 448 bits/sec, 0 packets/sec
9 packets output, 824 bytes
0 output error
Input bandwidth utilization : -
Output bandwidth utilization : -
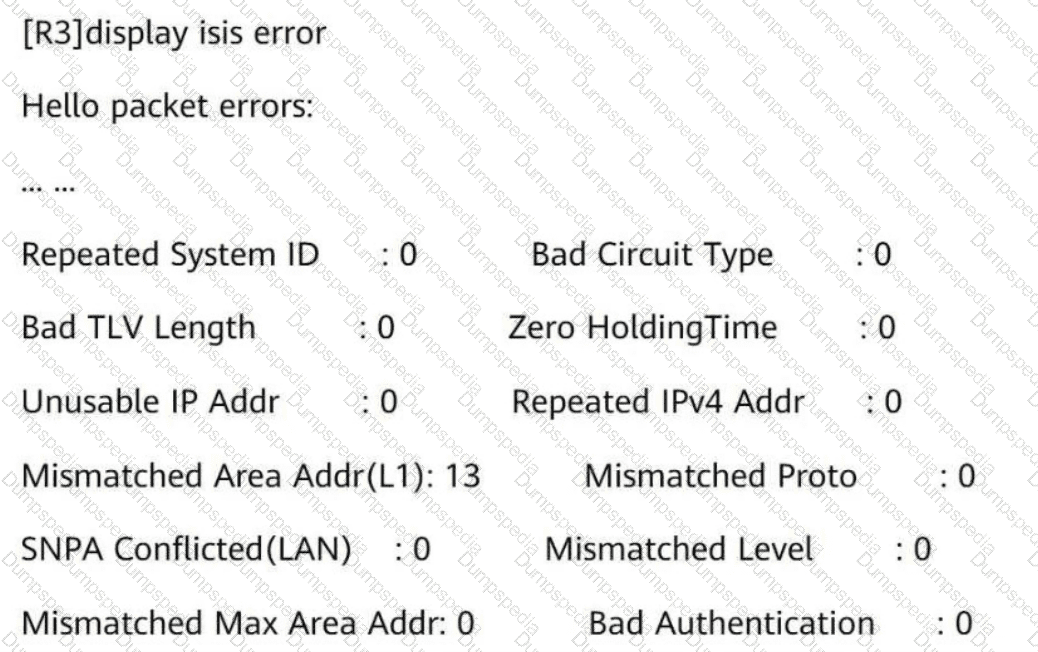
The IS-IS Level-1 neighbor relationship is not established between R3 and R4. Referring to the following information, what is the possible cause?
The naming of SRv6 instructions complies with certain rules. You can quickly determine the function of an instruction based on the instruction name. Which of the following statements about the keywords in SRv6 instruction names are correct?
MPLS implements data forwarding based on two different planes. Which of the following statements regarding the forwarding mechanism are correct?
The free mobility function is deployed on the iMaster NCE-Campus on a campus network. Which of the following information should an administrator pay attention to?
SR-MPLS is enabled on all routers. The label information encapsulated by R1 into a data packet is shown in the figure.
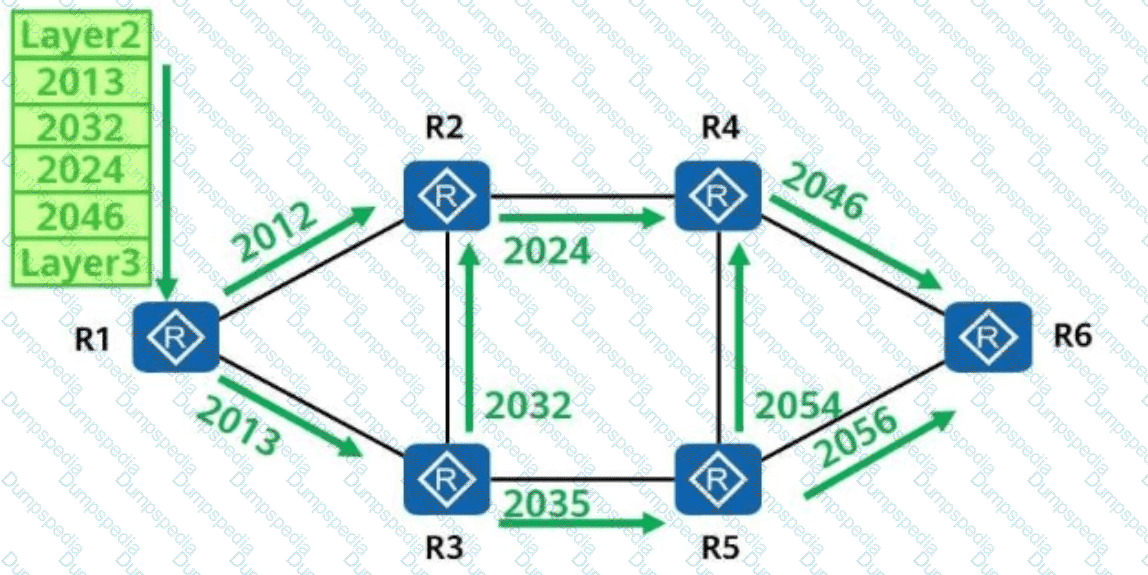
Which of the following is the forwarding path of the data packet?
Huawei Open Programmability System (OPS) uses standard HTTP methods to access managed objects and manage network devices.
Which of the following HTTP methods is used to configure the value of a network device’s managed object?
Telemetry data must be encoded in GPB binary format. This format reduces the number of bytes in telemetry messages and improves the transmission efficiency compared with messages encoded in JSON format.
IPsec SAs can be established in either manual mode or IKE auto-negotiation mode. Which of the following statements about the two modes is incorrect?
In the firewall hot standby scenario, which of the following status information can be backed up between the active and standby firewalls?
Exhibit:
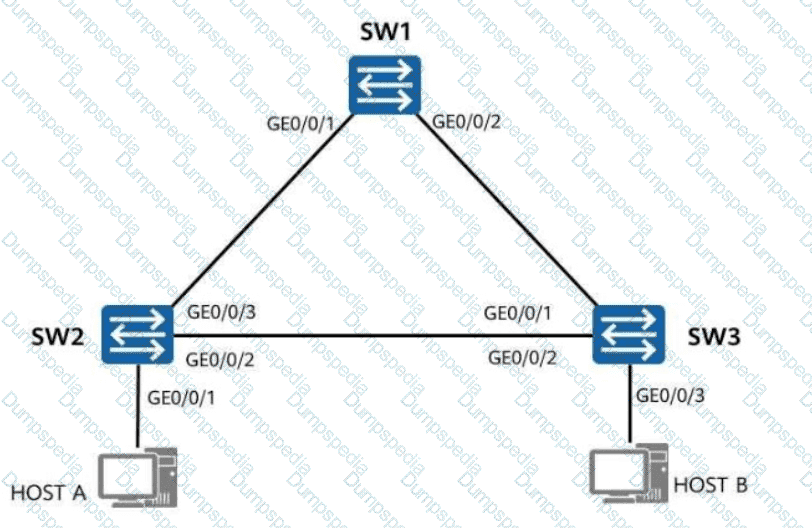
A loop occurs because Spanning Tree Protocol (STP) is not enabled on the network. Which of the following symptoms may occur?
During WLAN planning and design, channels 1, 6, and 11 are recommended on the 2.4 GHz frequency band, and channels 1, 5, 9, and 13 are recommended in high-density scenarios. On the 5 GHz frequency band, it is recommended that high-frequency and low-frequency channels of adjacent APs be staggered to prevent overlapping.
Which of the following statements about configuring user access authentication is incorrect?
To obtain the token ID of iMaster NCE, you need to send an HTTP request using the following Python code to invoke an iMaster NCE RESTful API:
Which of the following statements is incorrect?
The on-premise mode is recommended for controller deployment on small and midsize campus networks.
To prevent hackers from attacking user devices or networks using MAC addresses, you can configure MAC addresses of untrusted users as blackhole MAC addresses to filter out such invalid MAC addresses. When receiving a packet whose source or destination MAC address is a blackhole MAC address on a device, the device discards the packet.
Which of the following number sequences can be matched by the regular expression 100.$?
Which of the following fields is added to BGP4+ Update packets to advertise IPv6 routes?
On a campus network, iMaster NCE-Campus is used to deploy two VNs (Virtual Networks): R & D VN and Marketing VN. Users in these two VNs belong to two separate security groups.
The campus network requires R & D personnel and sales personnel to communicate with each other. To meet this requirement, which of the following tasks does a network administrator need to perform?
MPLS is located between the data link layer and network layer in the TCP/IP protocol stack and can provide services for all network layer protocols.
In the firewall hot standby scenario, in which of the following conditions will the local device proactively send VGMP packets?
OSPFv2 is an IGP running on IPv4 networks, whereas OSPFv3 is an IGP running on IPv6 networks. OSPFv2 and OSPFv3 have similar LSA types, but their LSA functions are slightly different. Which of the following is not an OSPFv3 LSA type?
In DU label advertisement mode, if the liberal label retention mode is used, the device reserves labels received from all the LDP peers regardless of whether the LDP peer is the optimal next hop for reaching the destination network.
In the small and midsize campus network design based on the Huawei CloudCampus Solution, when over 100 branches need to communicate with each other, which of the following interconnection networking models is recommended?
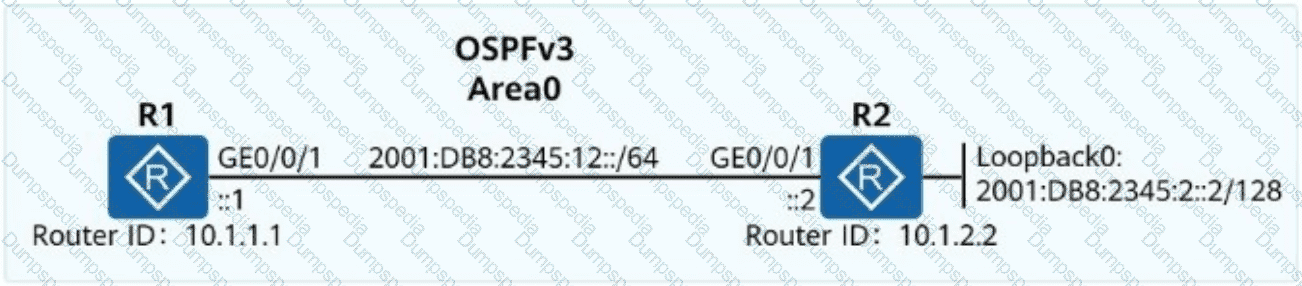
An engineer uses two routers to perform IPv6 tests and wants to use OSPFv3 for IPv6 network connectivity. Which of the following OSPFv3 configurations for R1 are correct?
Free mobility implements policy management and permission control based on users ' VLAN IDs and IP addresses.
Which of the following user logout modes are supported by 802.1X authentication?
iMaster NCE-CampusInsight uses SNMP technology to collect metrics and logs of network devices and detects network exceptions based on real service traffic.
After a wireless user passes Portal authentication, which of the following parameters cannot be used for authorizing the user?
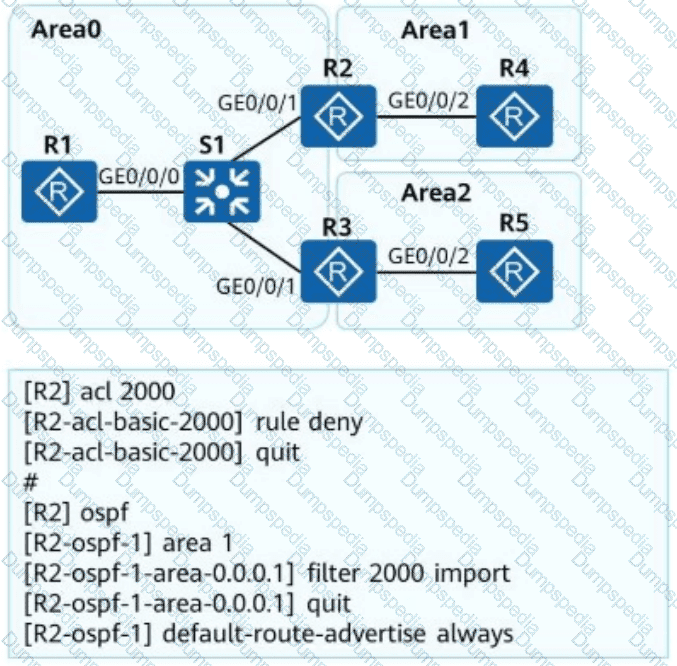
OSPF is deployed on a campus network to implement network interconnection. An engineer configures R2 as shown in the figure. Which of the following statements is incorrect about LSAs on the OSPF network?
Which of the following inter-AS MPLS L3VPN solutions does not require MPLS to run between ASBRs?
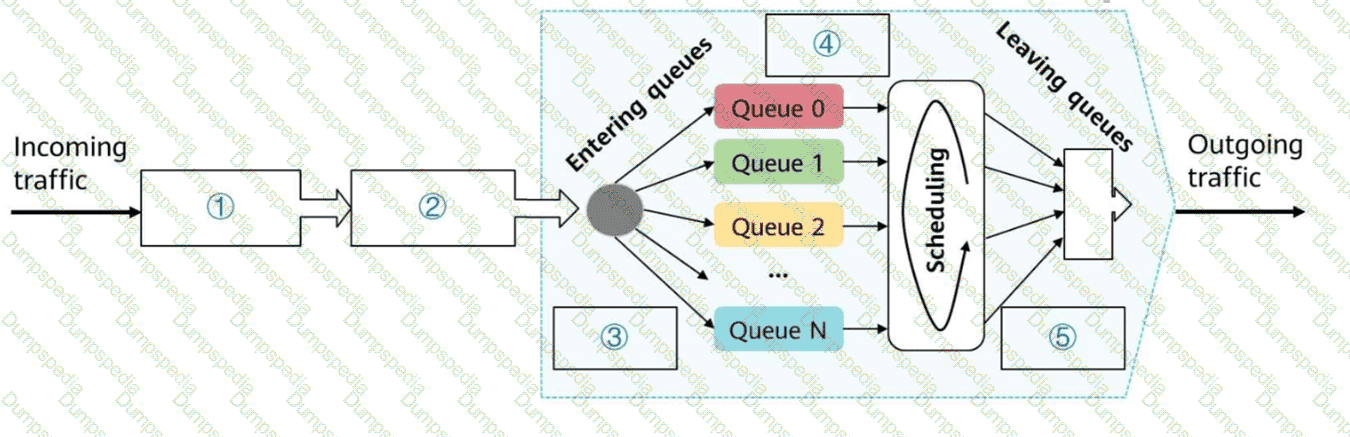
An enterprise has three types of services. Voice and video services are key services and need to be guaranteed, and FTP services are non-key services. Which of the following scheduling modes is optimal for satisfying the service requirements?
The telemetry network model is broadly and narrowly defined. Which of the following modules are involved in telemetry in a narrow sense (device-side telemetry)?
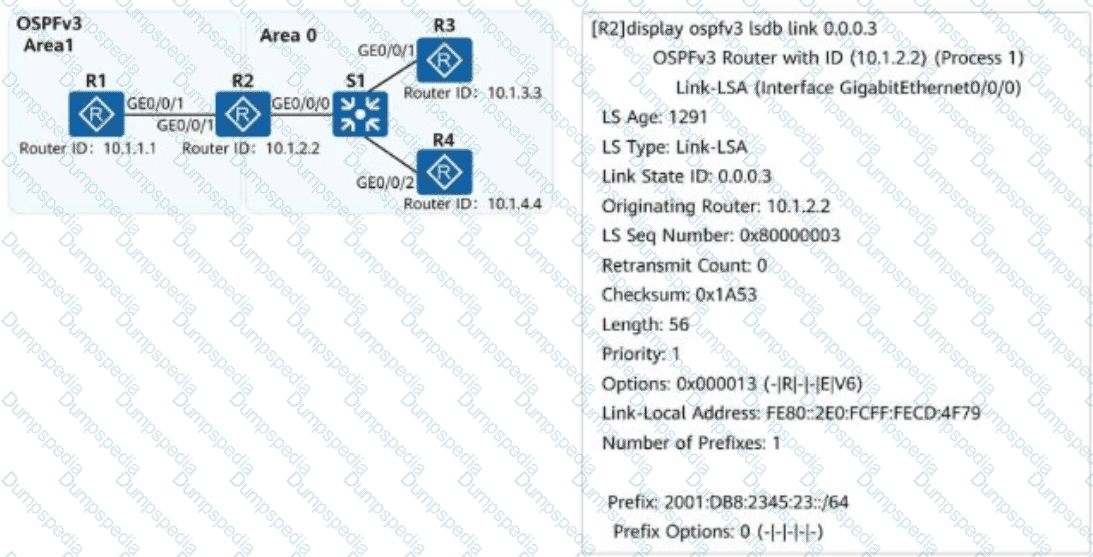
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and OSPFv3 is used for IPv6 network connectivity. An engineer checks the LSDB of R2 and obtains a Link-LSA. Which of the following statements about the LSA are correct?
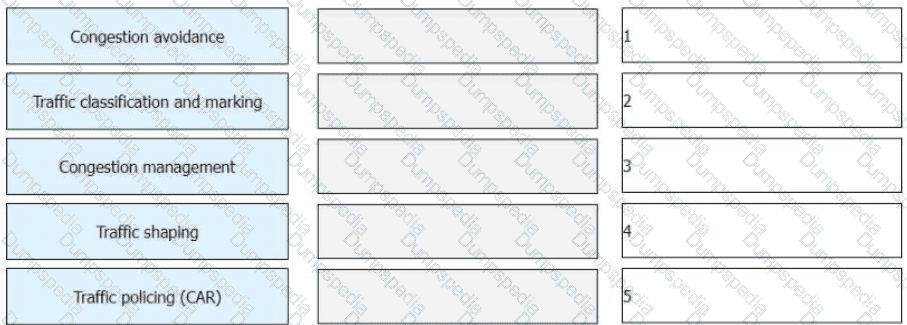
Complete the basic processing procedure for DiffServ model-based QoS shown in the figure
Refer to the figure.
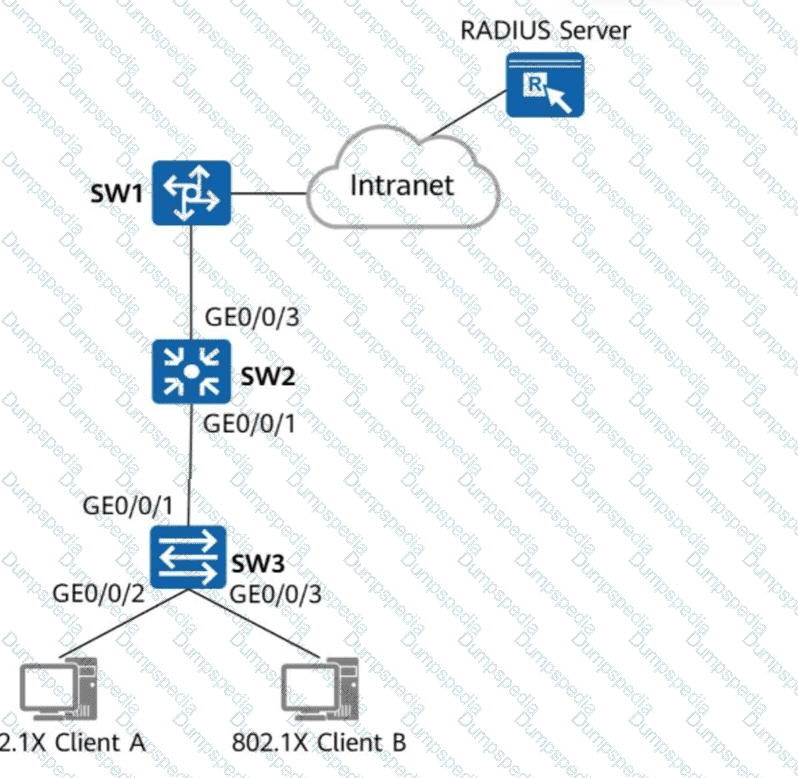
Which of the following steps are mandatory to enable 802.1X authentication on GE0/0/2 and GE0/0/3 of SW3 and configure a RADIUS server to authenticate and deliver network access rights to users?
Which of the following items are included in static information collection and analysis?
Which of the following statements is incorrect about access control on small and midsize campus networks based on the Huawei CloudCampus solution?
As shown in the following figure, OSPF is deployed on a campus network to implement network interconnection, and Area 1 is deployed as an NSSA. To enable R1 to access R4’s loopback interface address, an engineer imports a direct route to R4’s OSPF process. Which of the following statements about this scenario are correct?
[R4-ospf-1] import-route direct
Loopback0: 10.1.4.4/32
Which of the following statements are correct about the command:
ping -aX -cY -sZ -vpn-instance M 10.5.16.2
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following fields is not carried in BGP EVPN Type 2 routes?
The BGP ORF function can be used to control the maximum number of routes that can be sent by a BGP peer. To achieve this, which of the following tools is used to send such a route list to BGP peers?
Which of the following inter-AS MPLS L3VPN solutions needs ASBRs to transmit VPNv4 routes?
An O & M platform mainly provides unified monitoring and performance management for network devices. Which of the following is NOT device monitoring data?
Which of the following technologies can be used to isolate users in the same VLAN?
Which of the following are application optimization functions in the Huawei SD-WAN Solution?
During the evolution from OSPFv2 to OSPFv3, LSA formats and functions remain unchanged, except that the network layer addresses in LSAs are changed from IPv4 to IPv6.