When auditing databases, which of the following risks would an Internal auditor keep In mind In relation to database administrators?
An internal audit team performed an assurance engagement of the organization's IT security. The audit team found significant flaws in the design and implementation of the internal control framework. IT department managers often disagreed with the audit team on the significance of the findings, claiming that the controls in place partly mitigated the risks. Which of the following should be included when communicating the engagement results to senior management?
To achieve conformance with the Global Internal Audit Standards, the chief audit executive must include which of the following activities in the quality assurance and improvement program (QAIP)?
A company produces water buckets with the following costs per bucket:
Direct labor = 82
Direct material = $5
Fixed manufacturing = 83.50
Variable manufacturing = 82.50
The water buckets are usually sold for $15. However, the company received a special order for 50.000 water buckets at 311 each.
Assuming there is adequate manufacturing capacity and ail other variables are constant , what is the relevant cost per unit to consider when deciding whether to accept this special order at the reduced price?
An investor has acquired an organization that has a dominant position in a mature. slew-growth Industry and consistently creates positive financial income.
Which of the following terms would the investor most likely label this investment in her portfolio?
An internal auditor is assessing the risks related to an organization’s mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal auditor be most concerned about?
During the second half of the audit year, the chief audit executive (CAE) identified significant negative variances to the approved audit budget required to complete the internal audit plan. Which of the following actions should the CAE take?
Management decides to accept the risk on a significant audit observation related to the organization's exposure to fraud risk. The chief audit executive considers the finding to have a high residual risk. Which of the following steps should be performed last?
An organization created a formalized plan for a large project. Which of the following should be the first step in the project management plan?
A manager at a publishing company received an email that appeared to be from one of her vendors with an attachment that contained malware embedded in an Excel spreadsheet . When the spreadsheet was opened, the cybercriminal was able to attack the company's network and gain access to an unpublished and highly anticipated book. Which of the following controls would be most effective to prevent such an attack?
Which of the following best describes meaningful recommendations for corrective actions?
Which of the following statements is most accurate concerning the management and audit of a web server?
Which of the following controls would an internal auditor consider the most relevant to reduce risks of project cost overruns?
Which of the following is a distinguishing feature of managerial accounting, which is not applicable to financial accounting?
An organization’s account for office supplies on hand had a balance of $9,000 at the end of year one. During year two, the organization recorded an expense for purchasing office supplies. At the end of year two, a physical count determined that the organization has $11,500 in office supplies on hand. Based on this information, what would be recorded in the adjusting entry at the end of year two?
An internal auditor is reviewing results from software development integration testing. What is the purpose of integration testing?
While auditing an organization's customer call center, an internal auditor notices that Key performance indicators show a positive trend, despite the fact that there have been increasing customer complaints over the same period. Which of the following audit recommendations would most likely correct the cause of this inconsistency?
Which of the following types of date analytics would be used by a hospital to determine which patients are likely to require remittance for additional treatment?
According to IIA guidance, which of the following best describes an adequate management (audit) trail application control for the general ledger?
Which of the following is most appropriate for the chief audit executive to keep in mind when establishing policies and procedures to guide the internal audit function?
Management has decided to change the organizational structure from one that was previously decentralized to one that is now highly centralized. As such: which of the
following would be a characteristic of the now highly centralized organization?
During which phase of the contracting process are contracts drafted for a proposed business activity?
According to IIA guidance, which of the following statements is true regarding penetration testing?
Which of the following is a disadvantage in a centralized organizational structure?
An organization requires an average of 58 days to convert raw materials into finished products to sell. An additional 42 days is required to collect receivables. If the organization takes an average of 10 days to pay for raw materials, how long is its total cash conversion cycle?
An internal auditor uses a risk and control questionnaire as part of the preliminary survey for an audit of the organization's anti-bribery and corruption program. What is the primary purpose of using this approach?
Which approach should a chief audit executive take when preparing the internal audit plan?
According to IIA guidance, which of the following is a broad collection of integrated policies, standards, and procedures used to guide the planning and execution of a project?
Which of the following is the best example of a compliance risk that is likely to arise when adopting a bring-your-own-device (BYOD) policy?
A large retail customer made an offer to buy 10.000 units at a special price of $7 per unit. The manufacturer usually sells each unit for §10, Variable Manufacturing costs are 55 per unit and fixed manufacturing costs are $3 per unit. For the manufacturer to accept the offer, which of the following assumptions needs to be true?
Which of the following statements is true regarding cost-volume-profit analysis?
An organization's account for office supplies on hand had a balance of $9,000 at the end of year one. During year two. The organization recorded an expense of $45,000 for purchasing office supplies. At the end of year two. a physical count determined that the organization has $11 ,500 in office supplies on hand. Based on this Information, what would he recorded in the adjusting entry an the end of year two?
An internal auditor was asked to review an equal equity partnership, in one sampled transaction. Partner A transferred equipment into the partnership with a Self-declared value of 510 ,000, and Partner B contributed equipment with a self-declared value of 515,000. The capital accounts reach partner were subsequently credited with $12,500. Which of the following statements Is true regarding this transection?
A major IT project is scheduled to be implemented over a three-month period during the year. The chief audit executive (CAE) scheduled significant audit resources to provide consultation. Due to technical challenges from a supplier, the project is postponed until the following year. What should the CAE do in this case?
Which of the following situations best applies to an organization that uses a project, rather than a process, to accomplish its business activities?
Which of the following activities best illustrates a user's authentication control?
Which of the following purchasing scenarios would gain the greatest benefit from implementing electronic data interchange (EDI)?
During a routine bank branch audit, the internal audit function observed that the sole security guard at the branch only worked part time. The chief audit executive (CAE) believed that this increased the risk of loss of property and life in the event of a robbery. The branch security manager informed the CAE that a full-time guard was not needed because the branch was in close proximity to a police station. Still, the CAE found this to be an unacceptable risk due to the recent increase in robberies in that area. Which of the following is the most appropriate next step for the CAE to take?
During which phase of the contracting process ere contracts drafted for a proposed business activity?
Which of the following is the most appropriate way lo record each partner's initial Investment in a partnership?
Which of the following capital budgeting techniques considers the tune value of money?
Which observations should the chief audit executive include in the executive summary of the final engagement communication?
The budgeted cost of work performed is a metric best used to measure which project management activity?
After auditing the treasury function, the internal audit team issued a final report, which included an action plan agreed with management. When the audit team returned three months later to follow up on the action plan, management indicated that the plan had not been implemented because the old treasury system was being replaced with a new system. Which of the following is the most appropriate audit response?
According to Herzberg's Two-Factor Theory of Motivation, which of the following is a factor mentioned most often by satisfied employees?
Which of the following data privacy concerns can be attributed specifically to blockchain technologies?
Under which of the following circumstances can the internal audit function rely most confidently on the work performed by external auditors?
In light of increasing emission taxes in the European Union, a car manufacturer introduced a new middle-class hybrid vehicle specifically for the European market only. Which of the following competitive strategies has the manufacturer used?
At which fundamental level of a quality assurance and improvement program is an opinion expressed about the entire spectrum of the internal audit function’s work?
Which of the following best describes the type of control provided by a firewall?
After purchasing shoes from an online retailer, a customer continued to receive additional unsolicited offers from the retailer and other retailers who offer similar products.
Which of the following is the most likely control weakness demonstrated by the seller?
Which of the following Issues would be a major concern for internal auditors when using a free software to analyze a third-party vendor's big data?
Which of the following organization structures would most likely be able to cope with rapid changes and uncertainties?
When should the results of internal quality assessments be communicated to senior management and the board?
Which of the following common quantitative techniques used in capital budgeting is best associated with the use of a table that describes the present value of an annuity?
An organization that relies heavily on IT wants to contain the impact of potential business disruption to a period of approximately four to seven days. Which of the following
business recovery strategies would most efficiently meet this organization's needs?
An organization requires an average of 5S days to convert raw materials into finished products to sell. An average of 42 additional days is required to collect receivables. If the organization takes an average of 10 days to pay for the raw materials, how long is its total cash conversion cycle?
The internal auditor concluded there was a high likelihood that a significant wind farm development, worth $200 million, would be delayed from its approved schedule. As a result, electricity production would not start on time, leading to considerable financial penalties. Which of the following should be added to the observation to support its clarity and completeness?
Which of the following application controls is the most dependent on the password owner?
Given the information below, which organization is in the weakest position to pay short-term debts?
Organization A: Current assets constitute $1,200,000; Current liabilities are $400,000
Organization B: Current assets constitute $1,000,000; Current liabilities are $1,000,000
Organization C: Current assets constitute $900,000; Current liabilities are $300,000
Organization D: Current assets constitute $1,000,000; Current liabilities are $250,000
Which of the following statements is true regarding user developed applications (UDAs) and traditional IT applications?
During her annual performance review, a sales manager admits that she experiences significant stress due to her job but stays with the organization because of the high bonuses she earns. Which of the following best describes her primary motivation to remain in the job?
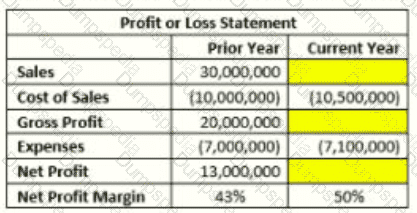
The manager of the sales department wants to Increase the organization's net profit margin by 7% (from 43% in the prior year to 50% in the current year). Given the information provided in the table below, what would be the targeted sales amount for the current year?
Which of the following statements is true concerning the basic accounting treatment of a partnership?
Which of the following network types should an organization choose if it wants to allow access only to its own personnel?
Which of the following IT layers would require the organization to maintain communication with a vendor in a tightly controlled and monitored manner?
An internal auditor discovered that the organization was not in full compliance with a regulatory labeling requirement for one of its products. The responsible manager indicated that the current product labeling has been in use for several years without any problems. If discovered, this regulatory breach could result in significant fines for the organization. What should be the chief audit executive's next course of action?
At what stage of project integration management would a project manager and project management team typically coordinate the various technical and organizational interfaces that exist in the project?
Senior management is trying to decide whether to use the direct write-off or allowance method for recording bad debt on accounts receivables. Which of the following would be the best argument for using the direct write-off method?
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
Which of the following financial statements provides the best disclosure of how a company's money was used during a particular period?
Which of the following capital budgeting techniques considers the expected total net cash flows from investment?
Which of the following principles s shared by both hierarchies and open organizational structures?
1. A superior can delegate the authority to make decisions but cannot delegate the ultimate responsibility for the results of those decisions.
2. A supervisor's span of control should not exceed seven subordinates.
3. Responsibility should be accompanied by adequate authority.
4. Employees at all levels should be empowered to make decisions.
What kind of strategy would be most effective for an organization to adopt in order to Implement a unique advertising campaign for selling identical product lines across all of its markets?
An internal auditor for a pharmaceutical company as planning a cybersecurity audit and conducting a risk assessment. Which of the following would be considered the most significant cyber threat to the organization?
Which of the following scenarios would require the chief audit executive (CAE) to change the internal audit plan and seek approval for the changes from the board?
A new manager received computations of the internal fate of return regarding the project proposal. What should the manager compare the computation results to in order to determine whether the project is potentially acceptable?
Which of the following statements is true regarding internal audit methodologies?
Which of the following physical access control is most likely to be based on ’’something you have" concept?
Which of the following situations best illustrates a "false positive" in the performance of a spam filter?
Which of the following communication characteristics is achieved when the internal audit function avoids redundancies and excludes information that is unnecessary, insignificant, or unrelated to the engagement?
An organization with global headquarters in the United States has subsidiaries in eight other nations. If the organization operates with an ethnocentric attitude, which of the following statements is true?
Which of the following would be a concern related to the authorization controls utilized for a system?
A bond that matures after one year has a face value of S250,000 and a coupon of $30,000. if the market price of the bond is 5265,000, which of the following would be the market interest rate?
An organization suffered significant damage to its local: file and application servers as a result of a hurricane. Fortunately, the organization was able to recover all information backed up by its overseas third-party contractor. Which of the following approaches has been used by the organization?
Which of the following is an indicator of liquidity that is more dependable than working capital?
Which of the following physical access controls is most likely to be based on the "something you have" concept?
How can the chief audit executive best provide the internal audit function with the resources needed to fulfill the annual audit plan?
Which of the following is an example of a physical control designed to prevent security breaches?
Which of the following business practices promotes a culture of high performance?
In an effort to increase business efficiencies and improve customer service offered to its major trading partners, management of a manufacturing and distribution company established a secure network, which provides a secure channel for electronic data interchange between the company and its partners. Which of the following network types is illustrated by this scenario?
An internal auditor found the following information while reviewing the monthly financial statements for a wholesaler of safety glasses: Opening inventory: 1,000 units at $2 per unit; Purchased: 5,000 units at $3 per unit; Sold: 3,000 units at $7 per unit. The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
According to The IIA's Three Lines Model, which of the following IT security activities is commonly shared by all three lines?
Which of the following would most likely serve as a foundation for individual operational goats?
Which of the following controls would be most efficient to protect business data from corruption and errors?
When evaluating the help desk services provided by a third-party service provider which of the following is likely to be the internal auditor's greatest concern?
Internal auditors want to increase the likelihood of identifying very small control and transaction anomalies in their testing that could potentially be exploited to cause material breaches. Which of the following techniques would best meet this objective?
An organization's technician was granted a role that enables him to prioritize projects throughout the organization. Which type of authority will the technician most likely be exercising?
Which of the following biometric access controls uses the most unique human recognition characteristic?
An organization prepares a statement of privacy to protect customers' personal information. Which of the following might violate the privacy principles?
An organization has a declining inventory turnover but an increasing gross margin rate. Which of the following statements can best explain this situation?
Which would provide the board with the highest level of assurance regarding whether an internal audit function can achieve its objectives?
An organization's IT systems can only be accessed using the organization's virtual private network. However, organizational emails, videoconferencing, and file-sharing tools are cloud-based and can be accessed using multi-factor authentication via any device. Which of the following risks should the organization acknowledge?
A retail organization mistakenly did have include $10,000 of Inventory in the physical count at the end of the year. What was the impact to the organization's financial statements?
According to IIA guidance, which of the following are typical physical and environmental IT controls?
Which of the following describes the most appropriate set of tests for auditing a workstation's logical access controls?
Which of the following is a result of Implementing on e-commerce system, which relies heavily on electronic data interchange and electronic funds transfer, for purchasing and biting?
Which of the following describes the most appropriate set of tests for auditing a workstation’s logical access controls?
Management is designing its disaster recovery plan. In the event that there is significant damage to the organization's IT systems this plan should enable the organization to resume operations at a recovery site after some configuration and data restoration. Which of the following is the ideal solution for management in this scenario?
Which of the following is an example of internal auditors applying data mining techniques for exploratory purposes?
Which of the following backup methodologies would be most efficient in backing up a database in the production environment?
Which of the following accounting methods is an investor organization likely to use when buying 40 percent of the stock of another organization?
A new clerk in the managerial accounting department applied the high-low method and computed the difference between the high and low levels of maintenance costs. Which type of maintenance costs did the clerk determine?
Based on test results, an IT auditor concluded that the organization would suffer unacceptable loss of data if there was a disaster at its data center. Which of the following test results would likely lead the auditor to this conclusion?
Which of the following security controls would be me most effective in preventing security breaches?
A third party who provides payroll services to the organization was asked to create audit or “read-only 1 functionalities in their systems. Which of the following statements is true regarding this request?
Which of the following statements. Is most accurate concerning the management and audit of a web server?
While performing an audit of a car tire manufacturing plant, an internal auditor noticed a significant decrease in the number of tires produced from the previous operating
period. To determine whether worker inefficiency caused the decrease, what additional information should the auditor request?
According to IIA guidance on IT, which of the following strategies would provide the most effective access control over an automated point-of-sale system?
Which of the following is true of bond financing, compared to common stock, when alJ other variables are equal?
In reviewing an organization's IT infrastructure risks, which of the following controls is to be tested as pan of reviewing workstations?
Which of the following physical security controls is able to serve as both a detective and preventive control?
What is the first step an internal audit function should take to define its organizational structure, deliverables, communication protocols, and resourcing model?
The internal audit function of a manufacturing organization is conducting an advisory engagement. The engagement team identifies a gap in procedures: there is no documentation for the activities that take place when new site construction projects are completed. In practice, these activities include the transfer of assets from the development department to the production department. What is the most appropriate action for the engagement team?
Which of the following should the chief audit executive agree upon with the board before starting an external assessment of the internal audit function?
Which of the following risks would Involve individuals attacking an oil company's IT system as a sign of solidarity against drilling in a local area?
Which of the following would most likely be found in an organization that uses a decentralized organizational structure?
Which type of bond sells at a discount from face value, then increases in value annually until it reaches maturity and provides the owner with the total payoff?
Which of the following should be included in a data privacy poky?
1. Stipulations for deleting certain data after a specified period of time.
2. Guidance on acceptable methods for collecting personal data.
3. A requirement to retain personal data indefinitely to ensure a complete audit trail,
4. A description of what constitutes appropriate use of personal data.
An internal audit function has commenced its annual follow-up activity. An internal auditor has been assigned to verify whether the recommendations from an audit engagement completed three months ago were implemented by the business unit. The auditor had not participated in that audit engagement. What should the auditor do first?
For employees, the primary value of implementing job enrichment is which of the following?
The IT department maintains logs of user identification and authentication for all requests for access to the network. What is the primary purpose of these logs?
The chief audit executive (CAE) identified an unacceptable risk and believes that the risk is not being mitigated to an acceptable level. Which of the following is the CAE's next step in this situation?
According to I1A guidance on IT. which of the following activities regarding information security Is most likely to be the responsibility of line management as opposed to executive management, internal auditors, or the board?
According to 11A guidance on IT, which of the following spreadsheets is most likely to be considered a high-risk user-developed application?