You have a Microsoft 365 E5 subscription
You need to use Microsoft Cloud App Security to identify documents stored in Microsoft SharePomt Online that contain proprietary information.
What should you create in Cloud App Security?
Please wait while the virtual machine loads. Once loaded, you may proceed to the lab section. This may take a few minutes, and the wait time will not be deducted from your overall test time.
When the Next button is available, click it to access the lab section. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
Username and password
Use the following login credentials as needed:
To enter your username, place your cursor in the Sign in box and click on the username below.
To enter your password, place your cursor in the Enter password box and click on the password below.
Microsoft 365 Username:
admin@LODSe00019@onmicrosoft.com
Microsoft 365 Password: #HSP.ug?$p6un
If the Microsoft 365 portal does not load successfully in the browser, press CTRL-K to reload the portal in a new browser tab.
The following information is for technical support only:
Lab instance: 11122308

You need to prevent any email messages that contain data covered by the U.K. Data Protection Act from being sent to recipients outside of your organization, unless the messages are sent to an external domain named adatum.com.
To complete this task, sign in to the Microsoft 365 admin center.
You need to enable and configure Microsoft Defender for Endpoint to meet the security requirements. What should you do?
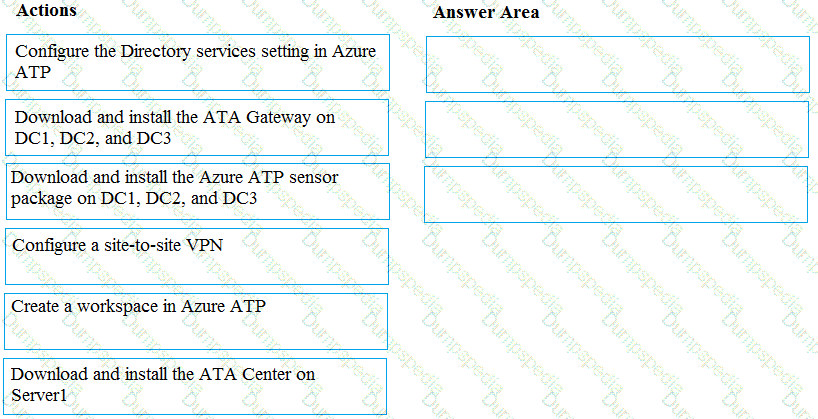
You need to configure threat detection for Active Directory. The solution must meet the security requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
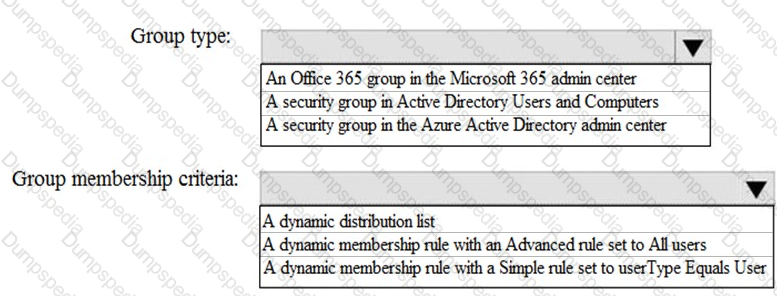
How should you configure Group3? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You haw a Microsoft 365 subscription.
You receive a General Data Protection Regulation (GOPR) request for the custom dictionary of a user From The Compliance admin center you need to create a content search, should you configure the content search?
You have several Conditional Access policies that block noncompliant devices from connecting to services.
You need to identify which devices are blocked by which policies.
What should you use?
You have a Microsoft 365 E5 subscription and a hybrid Microsoft Exchange Server organization.
Each member of a group named Executive has an on-premises mailbox. Only the Executive group members have multi-factor authentication (MFA) enabled. Each member of a group named Research has a mailbox in Exchange Online.
You need to use Microsoft Office 365 Attack simulator to model a spear-phishing attack that targets the Research group members.
The email address that you intend to spoof belongs to the Executive group members.
What should you do first?
You have a Microsoft 365 E5 subscription.
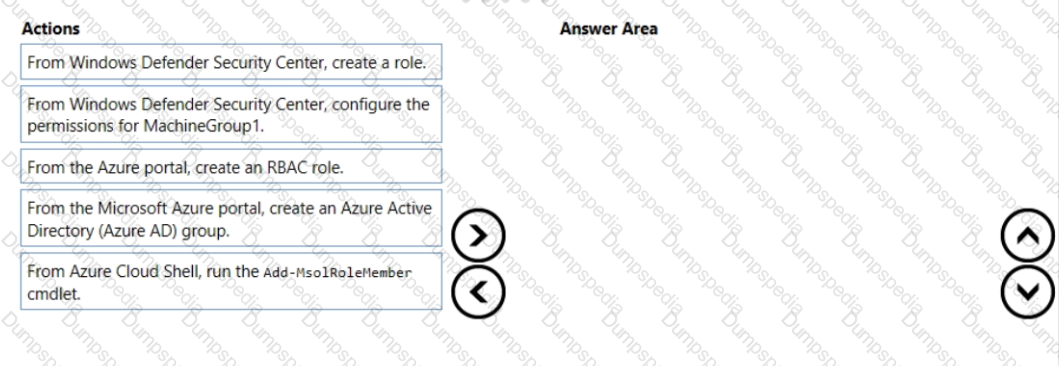
All computers run Windows 10 and are onboarded to Windows Defender Advanced Threat Protection (Windows Defender ATP).
You create a Windows Defender machine group named MachineGroup1.
You need to enable delegation for the security settings of the computers in MachineGroup1.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to implement Windows Defender ATP to meet the security requirements. What should you do?
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.
For contoso.com, you create a group naming policy that has the following configuration.
You plan to create the groups shown in the following table.
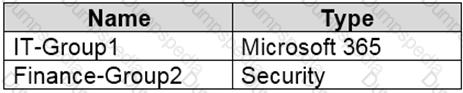
Which users can be used to create each group? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Your company has 500 computers.
You plan to protect the computers by using Windows Defender Advanced Threat Protection (Windows
Defender ATP). Twenty of the computers belong to company executives.
You need to recommend a remediation solution that meets the following requirements:
Windows Defender ATP administrators must manually approve all remediation for the executives
Remediation must occur automatically for all other users
What should you recommend doing from Windows Defender Security Center?
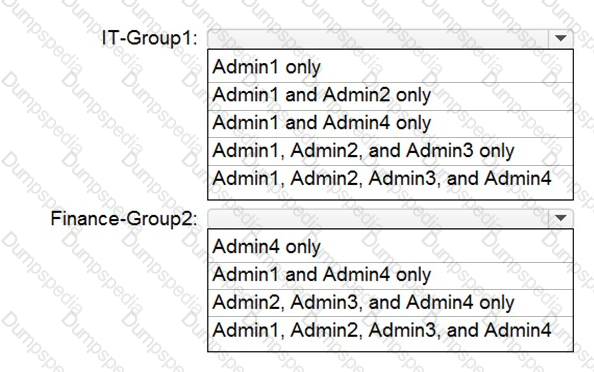
You are evaluating which devices are compliant in Intune.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
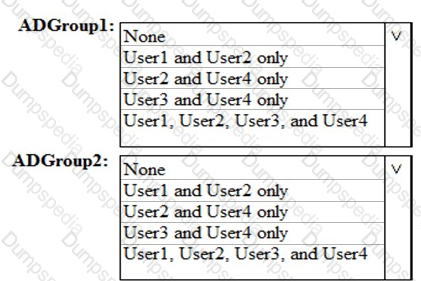
Which users are members of ADGroup1 and ADGroup2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
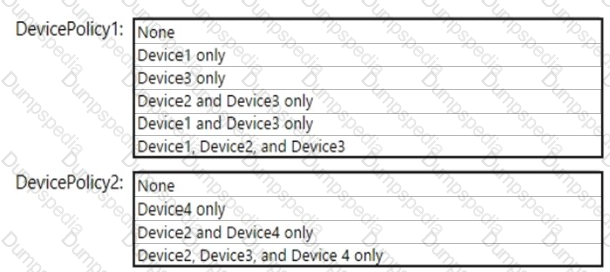
Which policies apply to which devices? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
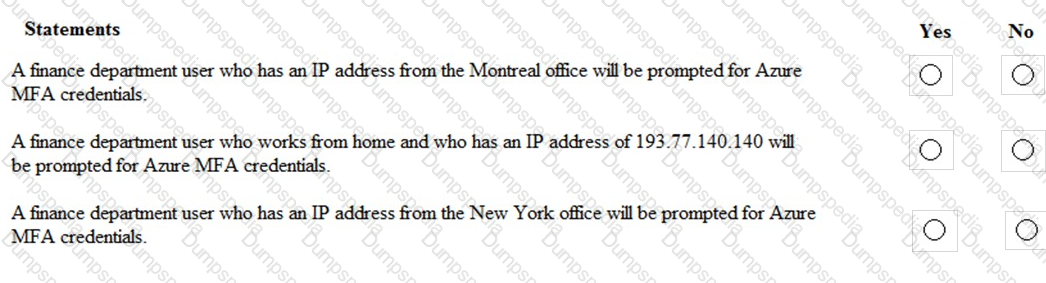
You are evaluating which finance department users will be prompted for Azure MFA credentials.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
NO: 7
You need to resolve the issue that targets the automated email messages to the IT team.
Which tool should you run first?
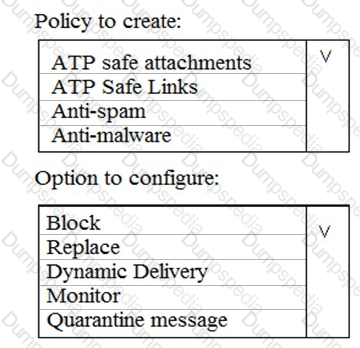
You need to recommend an email malware solution that meets the security requirements.
What should you include in the recommendation? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
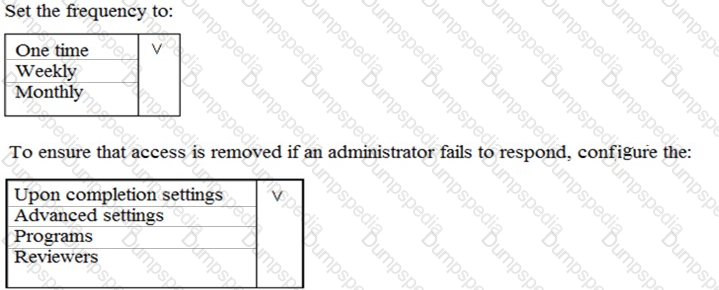
You plan to configure an access review to meet the security requirements for the workload administrators. You create an access review policy and specify the scope and a group.
Which other settings should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to recommend a solution that meets the technical and security requirements for sharing data with the partners.
What should you include in the recommendation? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
An administrator configures Azure AD Privileged Identity Management as shown in the following exhibit.
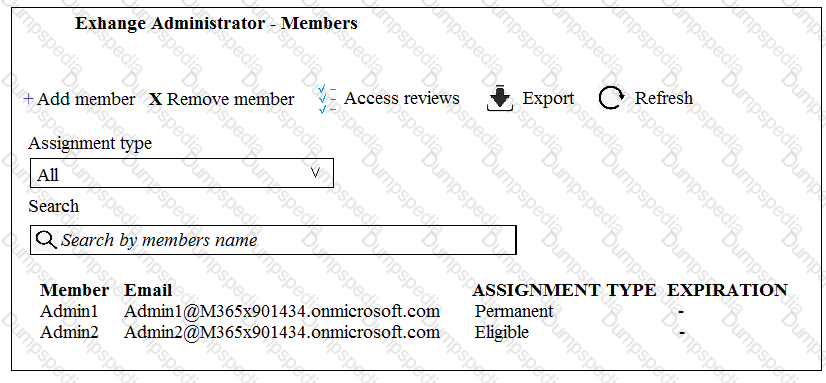
What should you do to meet the security requirements?
You need to recommend a solution for the user administrators that meets the security requirements for auditing.
Which blade should you recommend using from the Azure Active Directory admin center?
You install Azure ATP sensors on domain controllers.
You add a member to the Domain Admins group. You view the timeline in Azure ATP and discover that information regarding the membership change is missing.
You need to meet the security requirements for Azure ATP reporting.
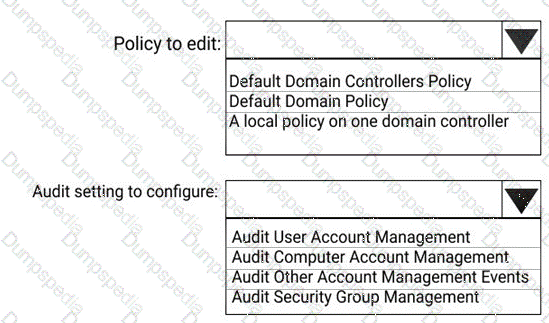
What should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.