Refer to the exhibit.
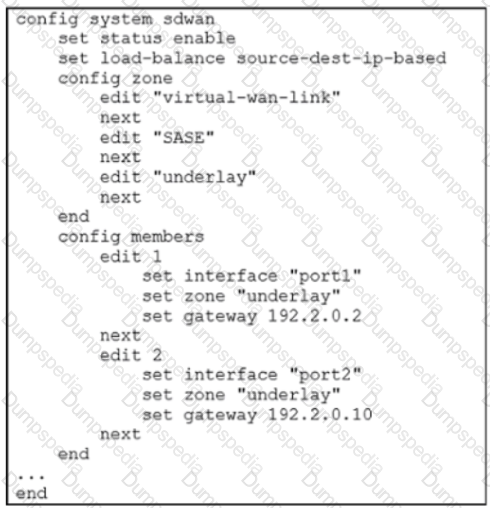
Which algorithm does SD-WAN use to distribute traffic that does not match any of the SD-WAN rules?
Refer to the exhibit.
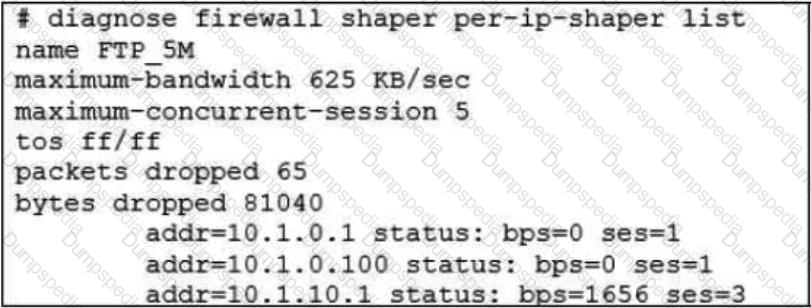
Which are two expected behaviors of the traffic that matches the traffic shaper? (Choose two.)
Refer to the exhibits.
Exhibit A

Exhibit B
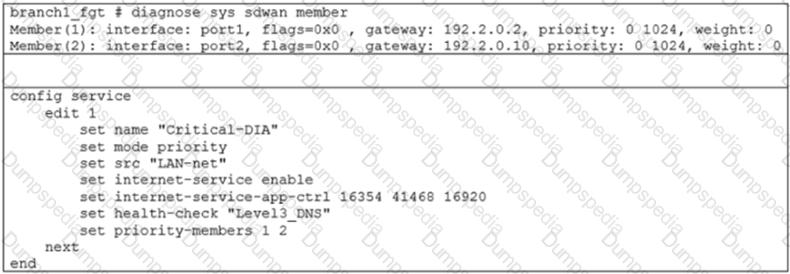
Exhibit A shows an SD-WAN event log and exhibit B shows the member status and the SD-WAN rule configuration.
Based on the exhibits, which two statements are correct? (Choose two.)
Which diagnostic command can you use to show the member utilization statistics measured by performance SLAs for the last 10 minutes?
Refer to the exhibit.

The exhibit shows the BGP configuration on the hub in a hub-and-spoke topology. The administrator wants BGP to advertise prefixes from spokes to other spokes over the IPsec overlays, including additional paths. However, when looking at the spoke routing table, the administrator does not see the prefixes from other spokes and the additional paths.
Based on the exhibit, which three settings must the administrator configure inside each BGP neighbor group so spokes can learn other spokes prefixes and their additional paths? (Choose three.)
Refer to the exhibit.

Based on the output, which two conclusions are true? (Choose two.)
Refer to the exhibit.

Which two SD-WAN template member settings support the use of FortiManager meta fields? (Choose two.)
Refer to the exhibit.

In a dual-hub hub-and-spoke SD-WAN deployment, which is a benefit of disabling the anti-replay setting on the hubs?

Exhibit B –

Exhibit A shows the system interface with the static routes and exhibit B shows the firewall policies on the managed FortiGate.
Based on the FortiGate configuration shown in the exhibits, what issue might you encounter when creating an SD-WAN zone for port1 and port2?
Which two statements describe how IPsec phase 1 main mode is different from aggressive mode when performing IKE negotiation? (Choose two )
Refer to the exhibits.

Exhibit A shows the packet duplication rule configuration, the SD-WAN zone status output, and the sniffer output on FortiGate acting as the sender. Exhibit B shows the sniffer output on a FortiGate acting as the receiver.
The administrator configured packet duplication on both FortiGate devices. The sniffer output on the sender FortiGate shows that FortiGate forwards an ICMP echo request packet over three overlays, but it only receives one reply packet through T_INET_1_0.
Based on the output shown in the exhibits, which two reasons can cause the observed behavior? (Choose two.)
What are two reasons for using FortiManager to organize and manage the network for a group of FortiGate devices? (Choose two )
Refer to the exhibit.
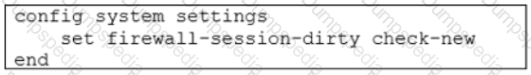
Based on the exhibit, which two actions does FortiGate perform on sessions after a firewall policy change? (Choose two.)