A security administrator deployed a Cisco Secure Email Gateway appliance with a mail policy configured to store suspected spam for review. The appliance is the DMZ and only the standard HTTP/HTTPS ports are allowed by the firewall. An administrator wants to ensure that users can view any suspected spam that was blocked. Which action must be taken to meet this requirement?
Refer to the exhibit.
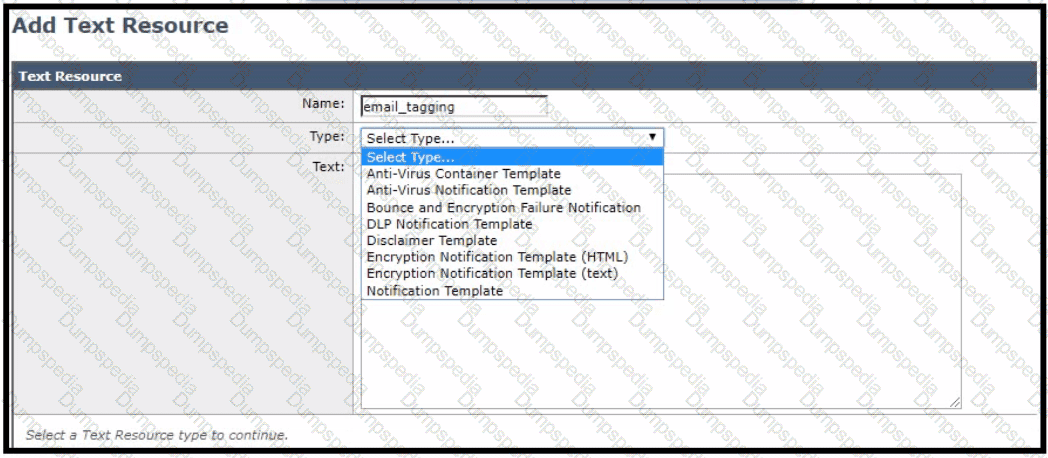
For improved security, an administrator wants to warn users about opening any links or attachments within an email How must the administrator configure an HTML-coded message at the top of an email body to create this warning?
Which type of query must be configured when setting up the Spam Quarantine while merging notifications?
When virtual gateways are configured, which two distinct attributes are allocated to each virtual gateway address? (Choose two.)
Which antispam feature is utilized to give end users control to allow emails that are spam to be delivered to their inbox, overriding any spam verdict and action on the Cisco ESA?
A Cisco ESA administrator was notified that a user wa s not receiving emails from a specific domain. After reviewing the mail logs, the sender had a negative sender-based reputation score.
What should the administrator do to allow inbound email from that specific domain?
An engineer deploys a Cisco Secure Email Gateway appliance with default settings in an organization that permits only standard H feature does not work. Which additional action resolves the issue?
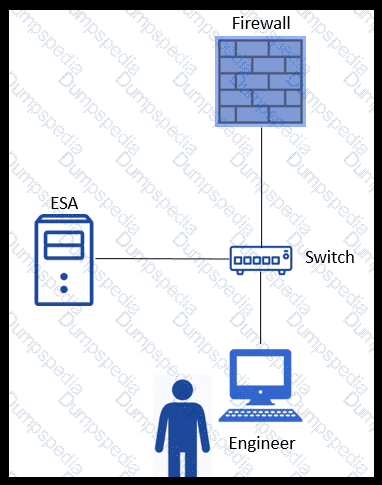
Refer to the exhibit. An engineer is trying to connect to a Cisco E SA using SSH and has been unsuccessful. Upon further inspection, the engineer notices that there is a loss of connectivity to the neighboring switch.
Which connection method should be used to determine the configuration issue?
Which cloud service provides a reputation verdict for email messages based on the sender domain and other attributes?
When a network engineer is troubleshooting a mail flow issue, they discover that some emails are rejected with an SMTP code of 451 and the error message " #4.7.1 Unable to perform DMARC verification " . In the DMARC verification profile on the Cisco Secure Email Gateway appliance, which action must be set for messages that result in temporary failure to prevent these emails from being rejected?
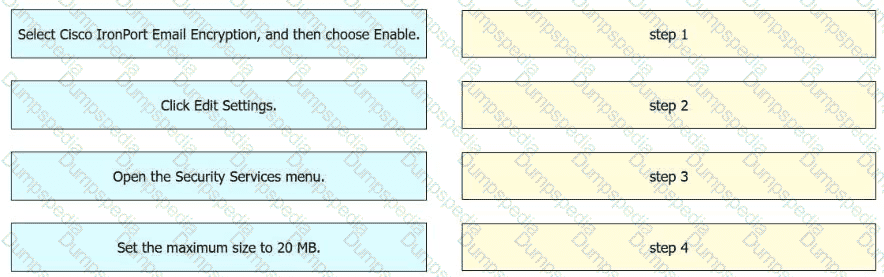
An engineer must enable encryption on a Cisco Secure Email Gateway. The maximum size of each message must be 20 MB. Drag and drop the actions from the left into sequence on the right to meet the requirement.
A network administrator notices that there are a high number of queries to the LDAP server. The mail logs show an entry “550 Too many invalid recipients | Connection closed by foreign host.”
Which feature must be used to address this?
An engineer wants to ensure that emails received by company users that contain URLs do not make them susceptible to data loss from accessing malicious or undesired external content sources Which two features must be configured on Cisco Secure Email Gateway to meet this requirement1? (Choose two.)
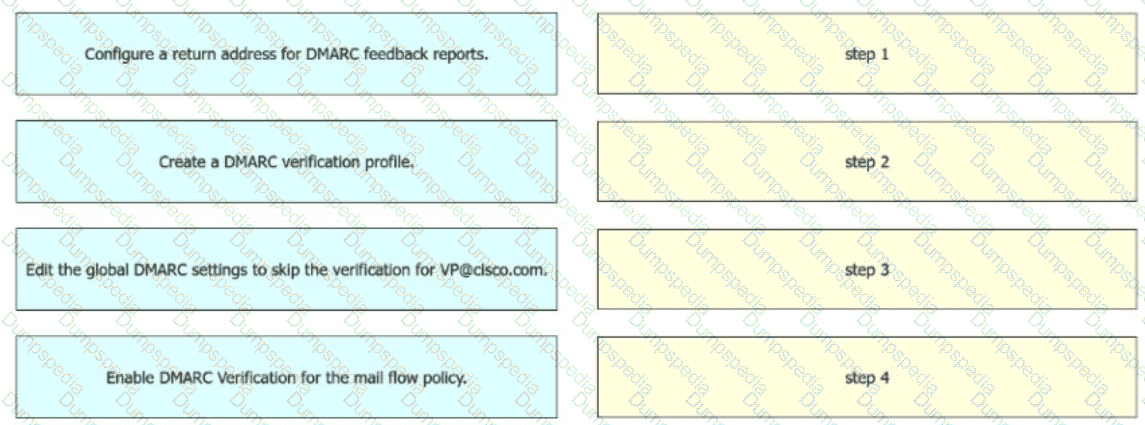
An engineer must configure incoming message verification using DM ARC in Cisco Secure Email Gateway. Emails from VP@cisco.com must skip the verification Drag and drop the actions from the left into the sequence on the right to meet the requirement.
Which two action types are performed by Cisco ESA message filters? (Choose two.)
Which method enables an engineer to deliver a flagged message to a specific virtual gateway address in the most flexible way?
When URL logging is configured on a Cisco ESA, which feature must be enabled first?
An organization wants to use DMARC to improve its brand reputation by leveraging DNS records.
Which two email authentica tion mechanisms are utilized during this process? (Choose two.)
Which Cisco Secure Email Threat Defense visibility and remediation mode is only available when using Cisco Secure Email Gateway as the message source?
An engineer tries to implement phishing simul-ations to test end users, but they are being blocked by the Cisco Secure Email Gateway appliance. Which two components, when added to the allow list, allow these simul-ations to bypass antispam scanning? (Choose two.)
An organization wants to use its existing Cisco ESA to host a new domain and enforce a separate corporate policy for that domain.
What should be done on the Cisco ESA to achieve this?
The CEO sent an email indicating that all emails containing a string of 123ABCDEFGHJ cannot be delivered and must be sent into quarantine for further inspection. Given the requirement, which regular expression should be used to match on that criteria?
An analyst creates a new content dictionary to use with Forged Email Detection.
Which entry will be added into the dictionary?
Spreadsheets containing credit card numbers are being allowed to bypass the Cisco ESA.
Which outgoing mail policy feature should be configured to catch this content before it leaves the network?
Which action is a valid fallback when a client certificate is unavailable during SMTP authentication on Cisco ESA?
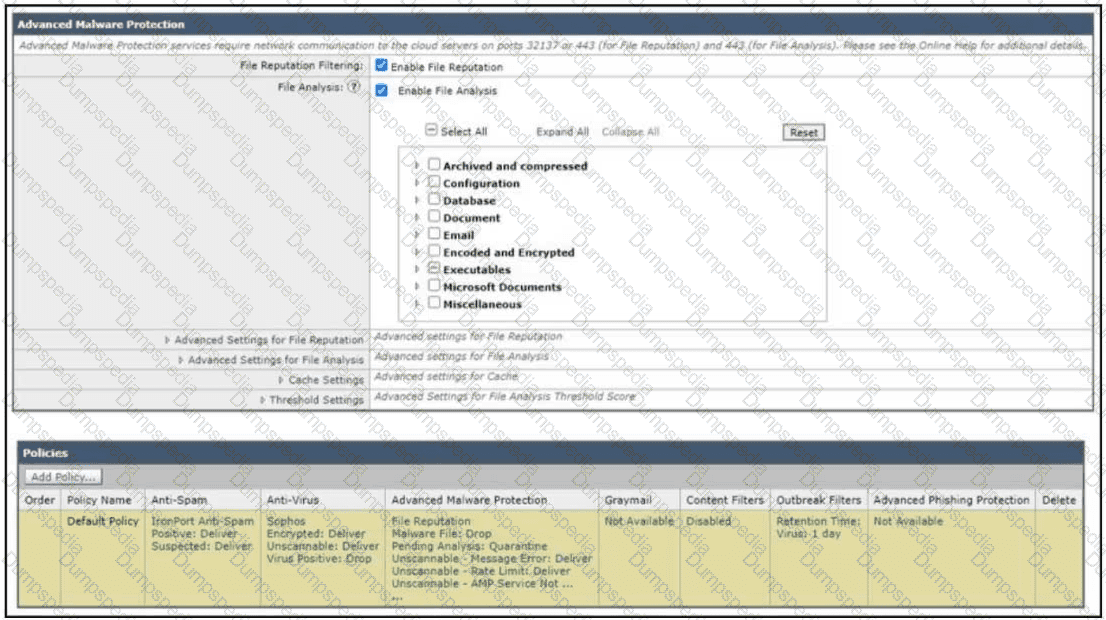
Refer to the exhibit. How does the Cisco Secure Email Gateway handle an email with an unknown Microsoft Word document?
An engineer is configuring a Cisco Secure Email Gateway and needs to reject email messages to a recipient with email address user0516585210@acme.com . Which list contains the allowed recipient addresses?
An engineer wants to utilize a digital signature in outgoing emails to validate to others that the email they are receiving was indeed sent and authorized by the owner of that domain Which two components should be configured on the Cisco Secure Email Gateway appliance to achieve this? (Choose two.)
A content dictionary was created for use with Forged Email Detection. Proper data that pertains to the CEO Example CEO: < ceo@example com > must be entered. What must be added to the dictionary to accomplish this goal?
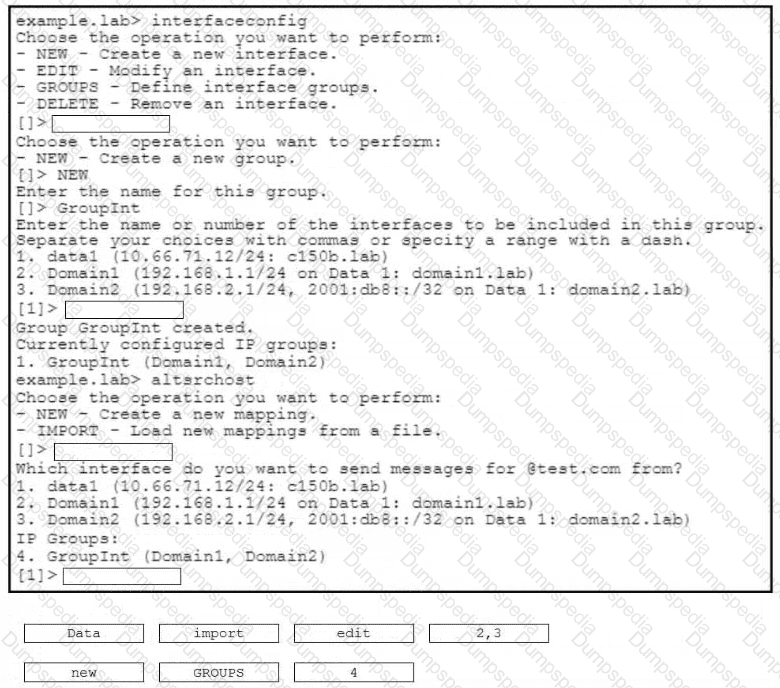
An engineer must configure a virtual gateway on a Cisco Secure Email Gateway to send email for a group named Grouplnt. Grouplnt is part of these domains:
•domain 1 -lab
•domain2.lab
Drag and drop the code snippets from the right onto the boxes to configure the virtual gateway. Not all options are used.
When the Spam Quarantine is configured on the Cisco ESA, what validates end-users via LDAP during login to the End-User Quarantine?
Which scenario prevents a message from being sent to the quarantine as an action in the scan behavior on Cisco ESA?
What is the default method of remotely accessing a newly deployed Cisco Secure Email Virtual Gateway when a DHCP server is not available?
When DKIM signing is configured, which DNS record must be updated to load the DKIM public signing key?
Which two components form the graymail management solution in Cisco ESA? (Choose two.)
Which restriction is in place for end users accessing the spam quarantine on Cisco Secure Email Gateway appliances?
An organization is enforcing TLS with an external party. The external business employs its own internal CA so the Secure Email Gateway cannot verify the TLS connection. Which action must an engineer take for the Cisco Secure Email Gateway to trust the connection?
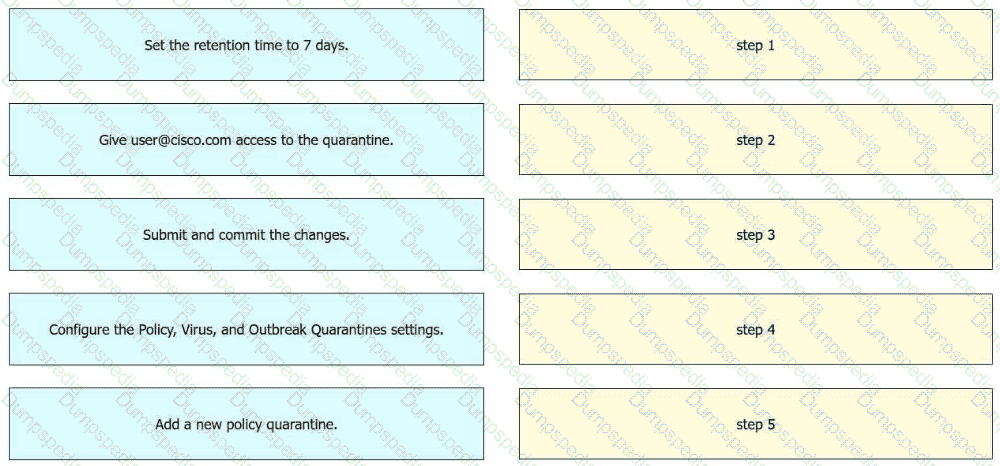
An engineer must configure a policy quarantine in Cisco Secure Email Gateway. The retention time must be 7 days and user@cisco.com must have access to the quarantine. Drag and drop the actions from the left into the sequence on the right to meet the requirements.
What is the order of virus scanning when multilayer antivirus scanning is configured?
A recent engine update was pulled down for graymail and has caused the service to start crashing. It is critical to fix this as quickly as possible.
What must be done to address this issue?
An engineer must configure a mail policy for all incoming email that contains a Microsoft Excel attachment. All such email must be quarantined without any exception. After the incoming mail policy is created, which action must be taken next to meet the requirement?
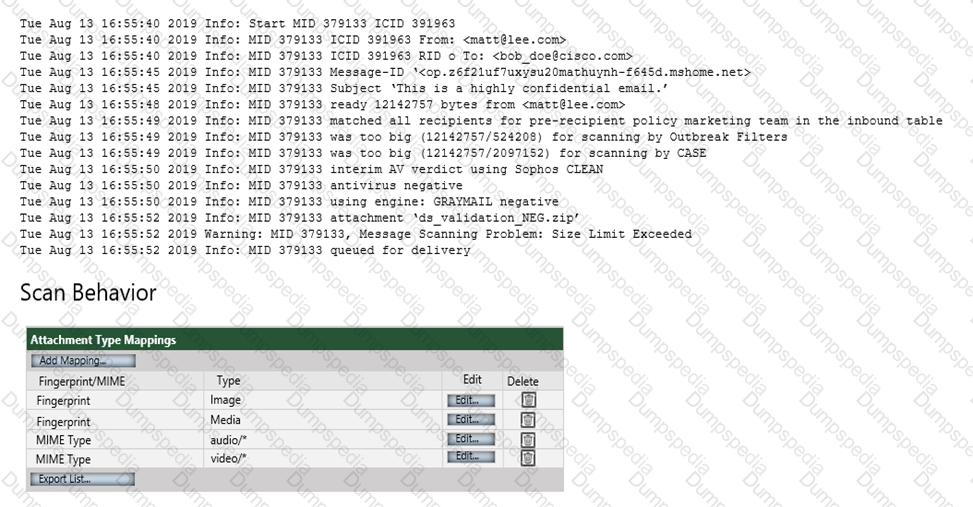
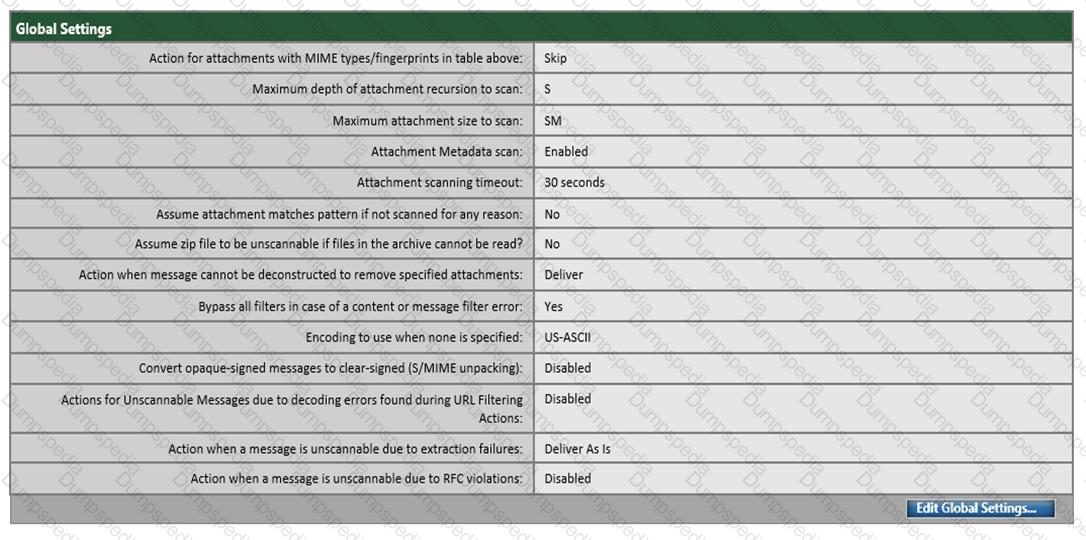
Refer to the exhibit. Which configuration on the scan behavior must be updated to allow the attachment to be scanned on the Cisco ESA?
Which two factors must be considered when message filter processing is configured? (Choose two.)
An organization has a strict policy on URLs embedded in emails. The policy allows visibility into what the URL is but does not allow the user to click it. Which action must be taken to meet the requirements of the security policy?
An engineer is tasked with reviewing mail logs to confirm that messages sent from domain abc.com are passing SPF verification and being accepted by the Cisco ESA. The engineer notices that SPF veri fication is not being performed and that SPF is not being referenced in the logs for messages sent from domain abc.com.
Why is the verification not working properly?
A network engineer is reviewing the record presented.

Which type of DNS record would contain the record as per the DKIM public key RFC 6376?
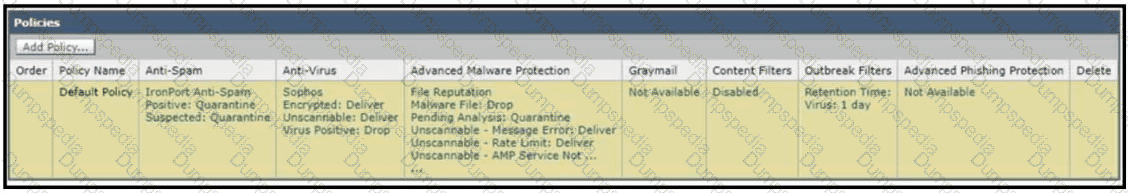
Refer to the exhibit. How does a Cisco Secure Email Gateway handle an email that is identified both as spam positive and outbreak positive by outbreak filters?
A Cisco ESA administrator has noticed that new messages being sent to the Centralized Policy Quarantine are being released after one hour. Previously, they were being held for a day before being released.
What was configured that caused this to occur?
A network engineer is integrating Cisco Secure Email Gateway with Cisco SecureX. Which two actions must be taken before registering Cisco Secure Email Gateway with Cisco SecureX? (Choose two.)