You are using Smart Search within the PPS Admin UI to investigate the final disposition of a message. Smart Search shows the message is Quarantined/Discard to adqueue. How do you trace the message?
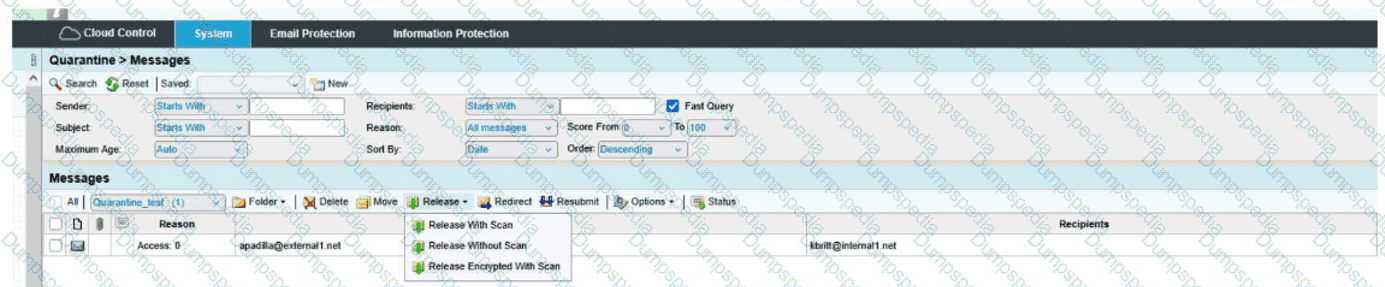
When you are attempting to release a message from the quarantine folder, you have the three choices shown here. The option of Release Encrypted With Scan will do which of the following?
You want an administrator, Peter Smith, to receive alerts when the SMTP Queue exceeds the configured threshold. How would you configure this?
Pick the 2 correct responses below.
You are configuring Proofpoint’s URL Rewrite feature for incoming emails. What is the primary purpose of this feature?
Based on the message details shown, which two actions are available to the administrator for this message?
When setting up an Import/Authentication Profile in PPS, which of the following is a required piece of information to connect to an LDAP server?
A SAML authentication profile is configured on the Proofpoint Protection Server console. Which portals can be accessed using this configuration?
If an email is incorrectly filtered as spam, what should an administrator do first when reviewing the filter logs?
Review the filter log exhibit.
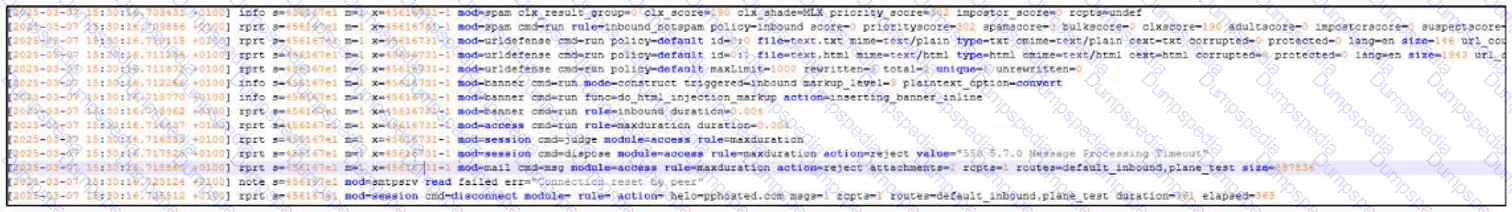
What two actions have taken place in the filter logs for this message?
What the exhibit shows clearly:
- URL Defense processing is present in the log
- A spam-related action/flag is present
In a scenario where an email is quarantined by both a spam policy (Spam) and an email firewall rule (Dictionary), which folder will the message ultimately be sent to?
You wish to ensure that all emails to an external partner are sent over a secure connection. What should you do?
The Abuse Mailbox event source was working in Cloud Threat Protection, but is now showing red under status and is no longer processing emails. After editing the source and clicking “Validate Source,” you receive the error “Unable to validate mailbox.” What is the likely cause of this error?
Smart Search has returned 13 results for a specific recipient address. You click on one of the messages in the Results list. Which of the following information is available for that message?