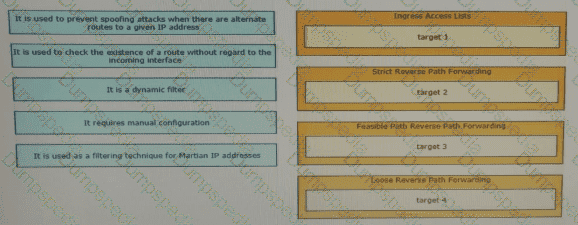
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.
Setting a specific goal for throughput based on per-second data rates between end hosts does not identify the requirements for specific applications When specifying throughput goals for applications, it is important to understand the throughput requirements for each application Which two factors that can constrain application layer throughput? (Choose two.)
A business wants to centralize servies via VDI technology and to replace remote WAN desktop PCs with thin client-type machines to reduce operating costs Which consideration supports the new business requirement?
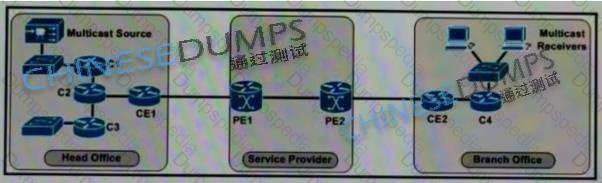
Refer to the exhibit. The enterprise customer wants to stream one-way video from their head office to eight branch offices using multicast. Their current service provider provides a Layer3 VPN solution and manages the CE routers, but they do not currently support multicast. Which solution quickly allows this multicast traffic to go through while allowing for future scalability?
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services Is true?
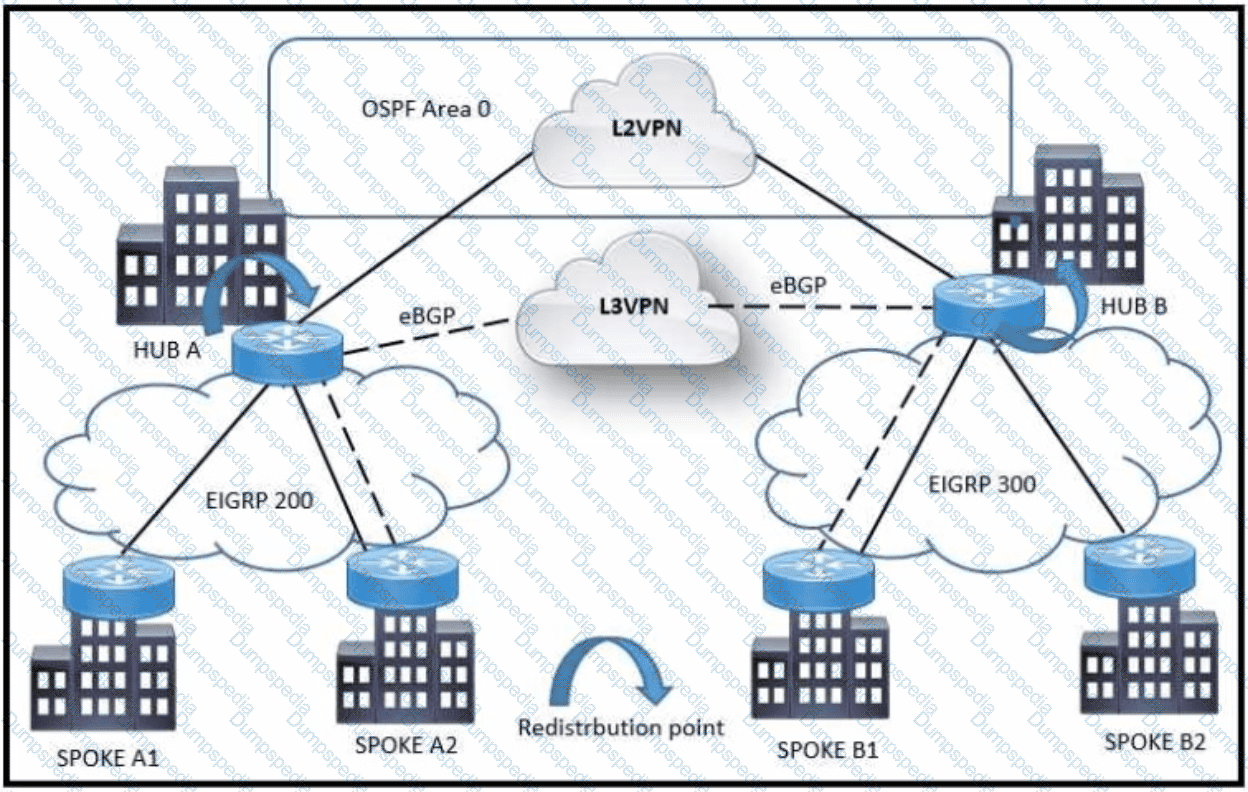
Refer to the exhibit A customer network design team is planning a migration from a legacy TDM-based L2VPN to an MPLS-based L3VPN Migration is planned in a phased approach:
•OSPF backbone Link between HUB A and HUB B sites to be migrated to eBGP
•Spoke A2 and Spoke B1 will be migrated to the L3VPN
Which solution design can be considered to avoid routing loops during backbone link migration
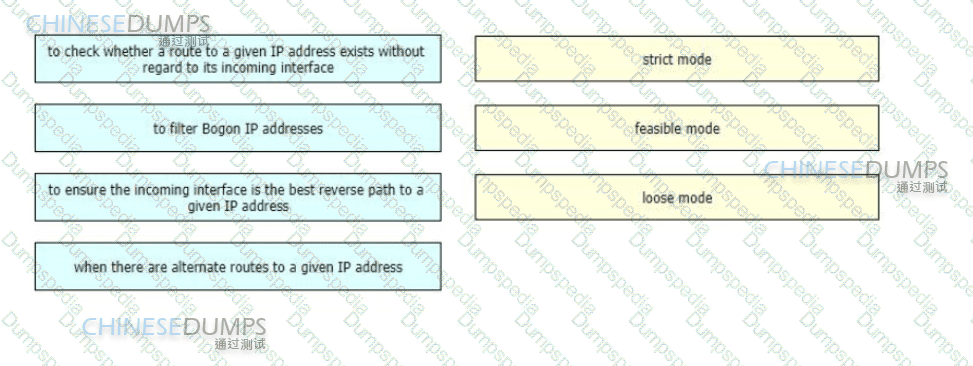
A networking team needs to prevent spoofing attacks They are describing the different uRPF design use cases so they can identify and deploy the optimal mode in various parts of their network
Drag and drop the use cases from the left onto the corresponding uRPF technique on the right Not all options are used
A network automation team plans to develop tasks to configure services on a network by using a Python controller The configuration tasks must be implemented by using operations that support network-wide transactions The candidate configuration must be validated automatically for all targeted devices before being applied to each specific device What can be used to apply the configuration to the network devices?
which two actions must be taken when assessing an existing wireless network implementation for its readliness to support voice traffic? (choose two)
A multinational organization has decided to migrate its business-critical operations to a hybrid cloud solution They are concerned about data governance, particularly regarding data sovereignty, ownership, and locale The company operates in multiple countries with strict data privacy regulations Which solution best ensures compliance with data governance regulations ' ?
The goal for any network designer is to strive to build a resilient network that adapts to changing conditions rapidly with minimal impact on the services running over the network A resilient network can adapt to failures but which soft failure can be harder to define and detect?
Company XYZ has two routing domains in their network, EIGRP and OSPF. The company wants to provide full reachability between the two domains by implementing redistribution on a router running both protocols They need to design the redistribution in a way that the OSPF routers will see link costs added to external routes. How must the redistribution strategy be designed for this network?
In a multi-cloud environment, which two practices should be implemented to safeguard the integrity of Al-driven network decisions? (Choose two.)
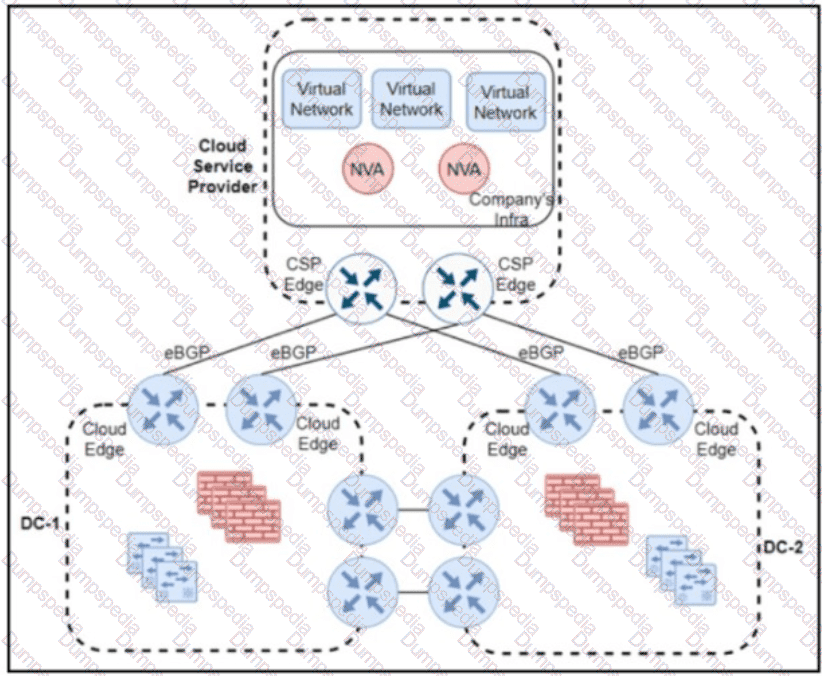
Refer to the exhibit A company has a hybrid cloud architecture with two on-premises data centers that connect to a public cloud service provider by using direct connect and eBGP routing. Encryption is unsupported by the cloud service provider, so the company plans to use an IPsec overlay network over its direct connects. Two virtual network appliances will be installed in the cloud infrastructure to establish tunnels and perform routing The company chose OSPF as the overlay routing protocol because the operations team is familiar with the protocol and because OSPF is the IGP on the on-premises network. The cloud network must be as isolated as possible from the on-premises network. What must be used for the OSPF overlay connectivity ?
A European government passport agency considers upgrading its IT systems to increase performance and workload flexibility in response to constantly changing requirements. The budget manager wants to reduce capital expenses and IT staff and must adopt the lowest-cost technology. Which technology choice is suitable?
Organic growth or decline comes from a company ' s normal business activities, rather than through acquisitions or divestment. Changes in usage patterns can also cause organic change in network requirements Which tool is useful when designing and operationalizing a network that is in the process of change?
monitoring solution, an organization wants to ensure they can collect feedback from network devices, particularly with a focus on being able to perform anomaly detection and automatically react to these events as they come m A key requirement is that the resources required to collect the data must be distributed Which data reporting approach is good fit for this use case?
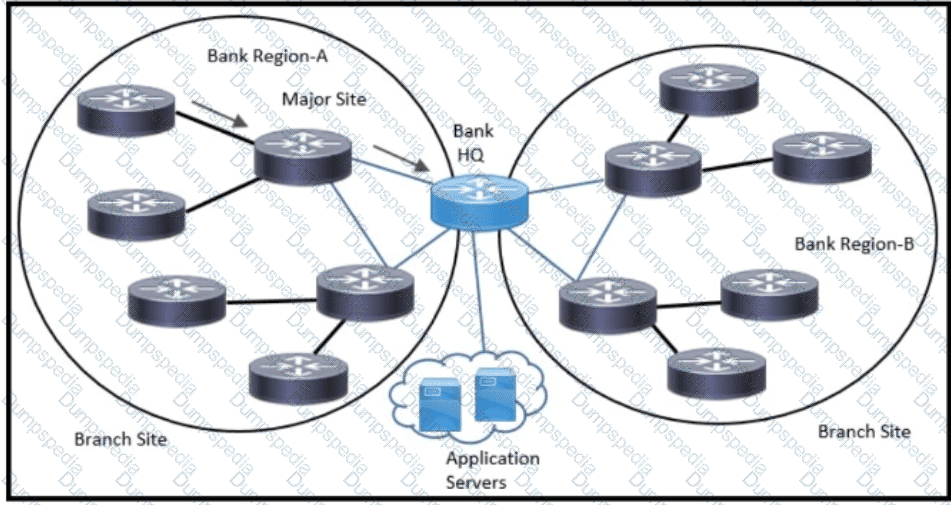
Refer to the exhibit. An architect has been tasked to design an ISIS solution for a medium-size financial customer. The resulting design must meet these requirements:
Which two ISIS design aspects must be included? (Choose two.)
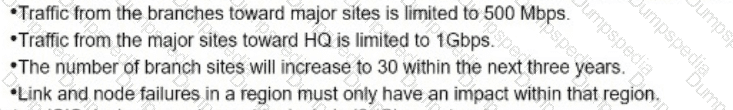
Software-defined network and traditional networks might appear the same to the end-user, but behind the scenes, each has unique sets of characteristics. Drag and drop these characteristic found on the left to the corresponding category on the right in no particular order?
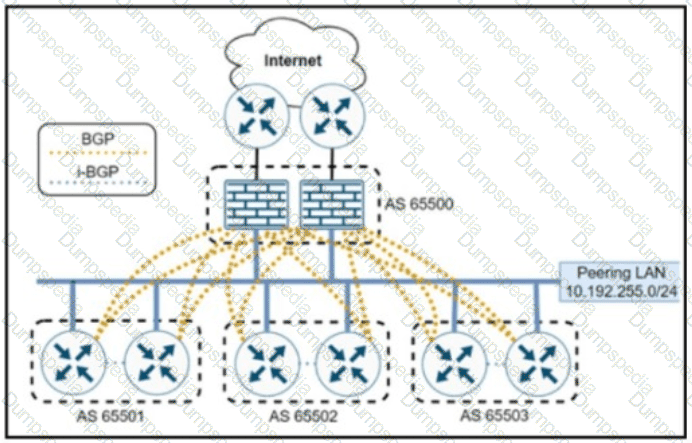
Refer to the exhibit in the topology, each router has a BGP session to each firewall in a hub-and-spoke BGP design The peering LAN implements an Ethernet Virtual Private LAN service from a service provider that offers carrier Ethernet services from its MPLS-enabled network Each router has an IP address in the 10.192 255.0/24 subnet. Spoke BGP routers must communicate with each other directly without traffic passing through the firewall AS PATH is used for policy enforcement.
How can BGP sessions be established between the routers and the firewalls?
Scalability is a desirable attribute of a network, system, or process Poor scalability can result in poor system performance, necessitating the reengineering or duplication of systems Load scalability is the ability of a system to perform gracefully as traffic increases Which two problems can occur due to poor load scalability design? (Choose two )
When planning their cloud migration journey what is crucial for virtually all organizations to perform?
Company XYZ has a multicast domain that spans across multiple autonomous systems The company wants to choose a technology that provides a simplified and controlled approach to interconnecting the multicast domains Which technology is the best fit for this purpose?
Software-defined networking architecture is used for cost-effective, adaptable, and easily manageable applications. In which two software-defined networks is SDN commonly used? (Choose two.)
Which component of the SDN architecture automatically ensures that application traffic is routed according to policies established by network administrators?
Company XYZ asks for design recommendations for Layer 2 redundancy. The company wants to prioritize fast convergence and resiliency elements In the design. Which two technologies are recommended? (Choose two.)
In a controller-based network architecture, between which of the two elements the southbound interface does the communication happen with a goal to program the data plane forwarding tables? (Choose two.)
Which service abstracts away the management of the operating system, middleware, and runtime?
The first step to building en A! strategy is understanding how it helps achieve business goals and objectives Al-first scorecard is an assessment of your organization ' s readiness to adopt and integrate AI technologies to gauge your capabilities and align stakeholders. Which scorecard is useful to understand whether the organization ' s digital infrastructure is strong enough to ensure seamless, standardized data flow between systems with optimal performance?
As part of workspace digitization, a large enterprise has migrated all their users to Desktop as a Sen/ice (DaaS), by hosting the backend system in their on-premises data center. Some of the branches have started to experience disconnections to the DaaS at periodic intervals, however, local users in the data center and head office do not experience this behavior. Which technology can be used to mitigate this issue?
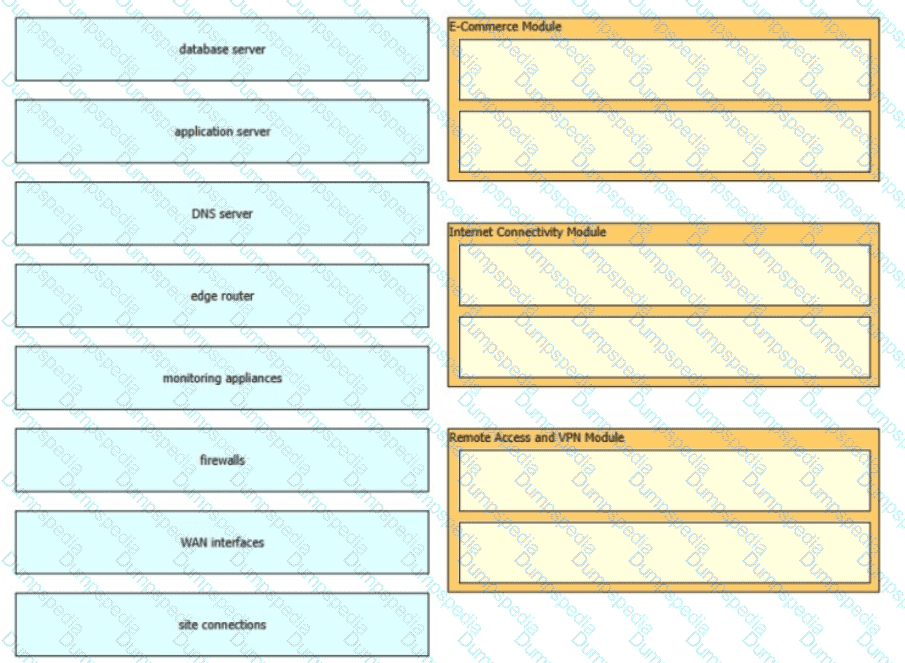
The Enterprise Edge infrastructure modules aggregate the connectivity from the various elements outside the campus—using various services and WAN technologies as needed typicaly provisioned from service providers and route the traffic into the Campus Core layer The Enterprise Edge modules perform security functions when enterprise resources connect across public networks and the internet Drag and drop the network device types from the left onto the corresponding modules on the right Not all options are used
The controller has a global view of the network, and it can easily ensure that the network is in a consistent and optimal configuration Which two statements describe a centralized SDN control path? (Choose two.)
What are two reasons for a company to prefer a hybrid approach rather than a mixed approach while transitioning to a software-defined network? (Choose two.)
When consumers that leverage laaS reach 100% resource capacity what can be used to redirect the overflow of traffic to the public cloud, so there is no disruption to service?
The Layer 3 control plane is the intelligence over the network that steers traffic toward its intended destination Which two techniques can be used in service provider-style networks to offer a more dynamic, flexible, controlled, and secure control plane design? (Choose two.)
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
Network designers often segment networks by creating modules for various reasons Sometimes however a network can be unintentionally segmented For instance, if the only way to connect a remote site to a headquarters or regional site is to connect them both to the public Internet the corporate network is now unintentionally segmented Which of the following option can be used to desegment the network in this situation?
An enterprise service provider is planning to migrate the customer network to MPLS to connect cloud applications The customer network team and service provider team are analyzing all process (tows before live migration and implementation Before planning the migration, what is a crucial task that must be executed?
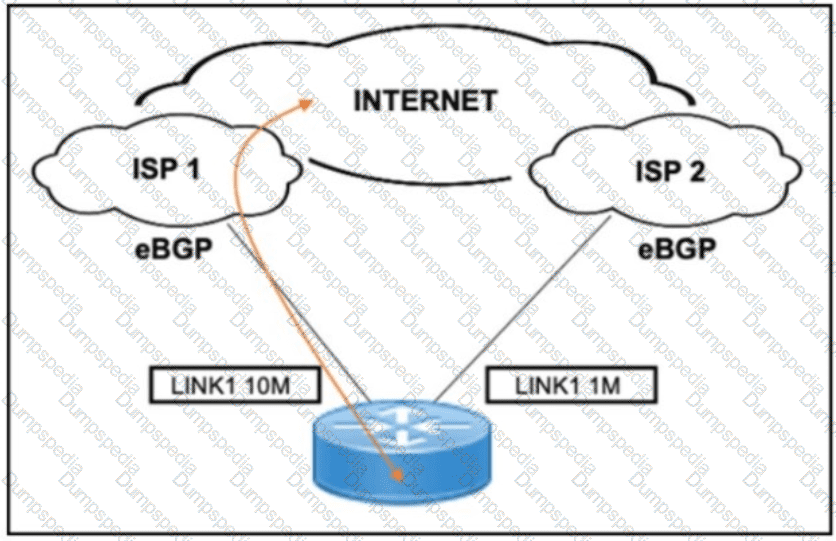
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
The PaaS model provides customers with a virtualized application development platform without the need for them to furnish hardware or system administration using in-house resources All necessary infrastructure components and application development services are provided and managed by the cloud service provider. Which limitation should be considered when selecting PaaS model?
SDN controllers need to sustain healthy operation under the pressure of different objectives from the applications they host. High availability can be achieved through improved southbound APIs and controller placement heuristics and formal models. Which two implementation strategy help to maximize resilience and scalability? (Choose two.)
There are varying requirements and motivations for improving the scalability and resilience of an enterprise application. The relative importance of these requirements and constraints varies depending on the type of app. the profile of the users, and the scale and maturity of the organization in which it is deployed. What are two common business drivers that deals with these aspects? (Choose two.)
As more links are added to the network, information and attributes related to the link is added to the control plane, meaning every link that gets added will slow down the convergence of the control plane by some measurable amount of time As a result when additional redundancy is built or added the MTTR will increase too Which risk increases along with the increased MTTR?
multinational corporation with offices in various regions worldwide are looking for a network architecture that provides a balance between low- latency and cost-effectiveness for connecting their offices to the cloud. Which cloud connectivity option is the best fit for this corporation?
An architect receives a business requirement from a CTO that states the RTO for a new system should be 4 hours, and the RPO should be less than 1 hour. Business continuity must also be ensured in the event of a natural disaster. Which replication method and data center technology should be used?
Refer to the exhibit Which impact of using three or more ABRs between the backbone area and area 1 is true?
A rapidly growing e-commerce business with a global customer base needs a robust network design that can support their business-critical operations and ensure low-latency access for their customers around the globe. The IT team is considering different solutions to meet their requirements. Which network design is suitable for these needs?
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
In traditional network design, the network and data center are confined within a single building In this configuration, a router connects the internal and external networks Basic configuration of an access control list within the router controls the traffic that can pass through Which security technique defines the boundary between an internal/trusted network and an external/untrusted network?
Which two advantages of using DWDM over traditional optical networks are true? (Choose two.)
Which two compliance audit functions are useful to meet business requirements? (Choose two.)
Piggybank, a leading financial institution, is planning to migrate its business-critical operations to a hybrid cloud solution A recommendation of the most appropriate security measure to protect sensitive financial data during data transmission must be given to the board of directors Which solution will meet these requirements?
Two routers R1 and R2 are directly connected through an Ethernet link Both routers are running OSPF. OSPF has been registered with BFD and BFD is running in asynchronous mode with the echo function enabled Which two actions occur that are related to the echo function? (Choose two)

Refer lo the exhibit Company XYZ BGP topology is as shown in the diagram The interface on the LA router connected toward the 10 1 5 0/24 network is faulty and is going up and down, which affects the entre routing domain Which routing technique can be used in the routing policy design so that the rest of the network is not affected by the flapping issue ?
An Agile for Infrastructure transition often means dismantling traditional IT hierarchies and rebuilding it to align with business objectives and workflows Organizations are seeing the benefits of using automation tools in the network such as faster more efficient more effective delivery of products and services. Which two components help increasing overall productivity and improve company culture? (Choose two.)
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)